Anyone who owns a cellphone has likely received an unexpected text message from a number they don’t recognize containing a link to be clicked on. Since April 1st of 2021, there has been a 6-fold increase in these nuisances and potentially dangerous texts. If you are to click on one of those links, you may be handing hackers valuable information they can use to swipe your bank account balance, fake your identity or even track your whereabouts. This type of social engineering attack is called ‘Smishing‘, which is simply Phishing through SMS text messages. They tout obvious bait such as energy-boosting supplements, cash prizes from major retailers, or CBD gummies in new flavors. Some are more subtle, masquerading as COVID test results, shipping notifications, or alerts for online payments that didn’t go through. Either way, they’re dangerous and getting more popular with cybercriminals.
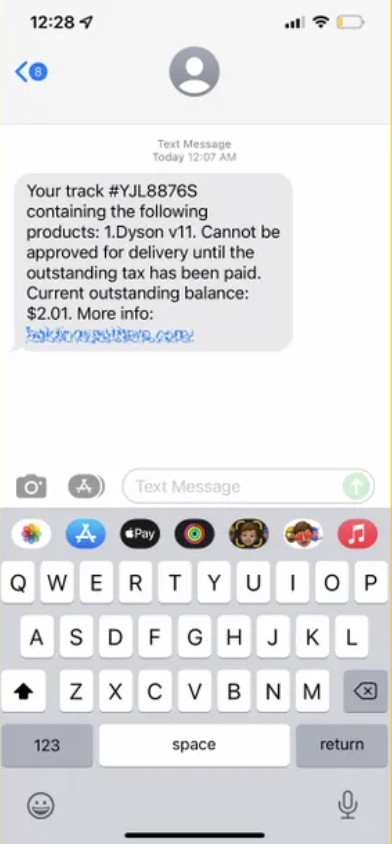
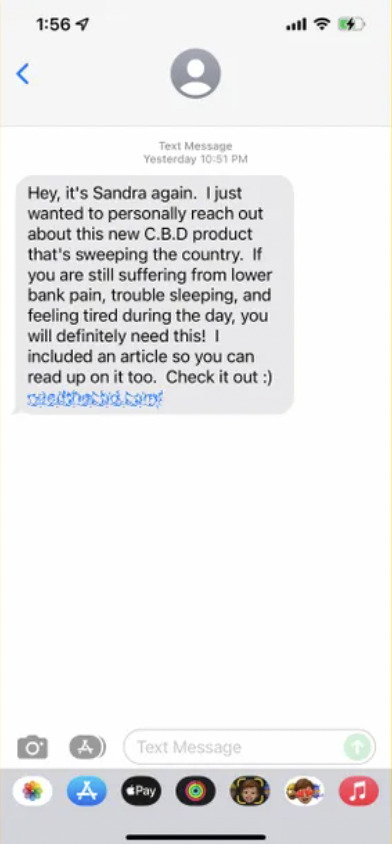
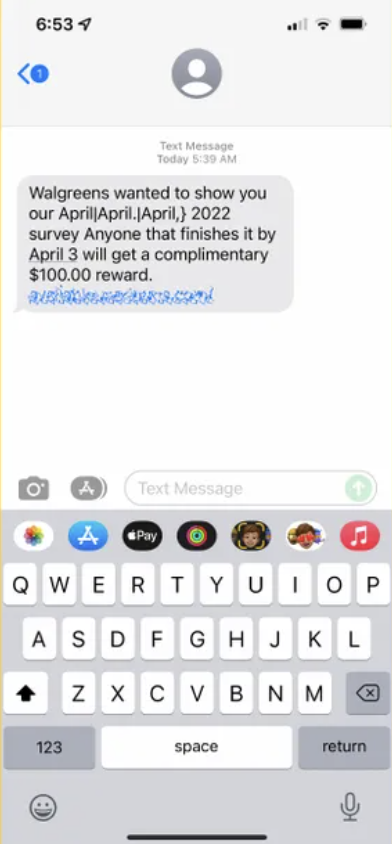
The vast majority of phishing attacks are attempting to grab personal data from unsuspecting consumers by way of an email. Cybercriminals, however, are increasingly taking advantage of distracted consumers who are rarely without their smartphones to trick people out of their logins and passwords, credit card or other financial information, or even access to their corporate networks. Take a look at the images below to get an idea of how they’re trying to trick unsuspecting users:
The Federal Trade Commission reports that scam texts cost US consumers $131 million last year, up from $86 million in 2020, and accounted for 21% of all reported fraud. More recently, Proofpoint detected a five-fold jump in mobile malware attacks in Europe starting in February. Those attacks included smishing attempts, as well as attacks in which malware was sent directly to devices through a malicious app. Could it be tied to the war in Ukraine which started then? CyberHoot suspects but cannot prove a link.
Proofpoint researchers note that smishing is becoming the attack method of choice for cybercriminals looking to compromise mobile devices, especially Apple’s iPhones. Recently, Pegasus, one of the most powerful pieces of spyware ever developed, was first able to worm its way into the phones of countless government officials, journalists, and human rights activists after they clicked on a malicious link in a text message or email.
In general, you don’t want to reply to text messages from people you don’t know. That’s the best way to remain safe. This is especially true when the text comes from a phone number that doesn’t look like a phone number, such as “5000”, or “452-981” number. This is a sign that the text message is actually just an email sent to a phone. You should exercise basic precautions when using your phone such as:
Remember, it only takes one bad text to compromise your data, phone, and personal security. With just a little bit of common sense and caution, you can make sure that you don’t become a victim of a smishing attack.
Additionally, these recommendations below will help you and your business stay secure with the various threats you may face on a day-to-day basis. All of the suggestions listed below can be gained by hiring CyberHoot’s vCISO Program development services.
All of these recommendations are built into CyberHoot the product or CyberHoot’s vCISO Services. With CyberHoot you can govern, train, assess, and test your employees. Visit CyberHoot.com and sign up for our services today. At the very least continue to learn by enrolling in our monthly Cybersecurity newsletters to stay on top of current cybersecurity updates.
Sources:
Additional Readings:
Discover and share the latest cybersecurity trends, tips and best practices – alongside new threats to watch out for.

You now have five important reasons to start a router security conversation with your small business clients this...
Read more
OAuth tokens don't expire when employees leave, passwords change, or apps go rogue. Your security program needs...
Read more
Most breaches don't start with a hacker in a hoodie cracking code at 3am. They start with your username and a...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
