Maximise engagement
Interactive, positive training methods, and fun, competitive ‘Hoot Ranks’ keep employees engaged, confident and secure.
Protect your organization with the positive approach to security awareness that reduces costs, effort and risk.
Interactive, positive training methods, and fun, competitive ‘Hoot Ranks’ keep employees engaged, confident and secure.
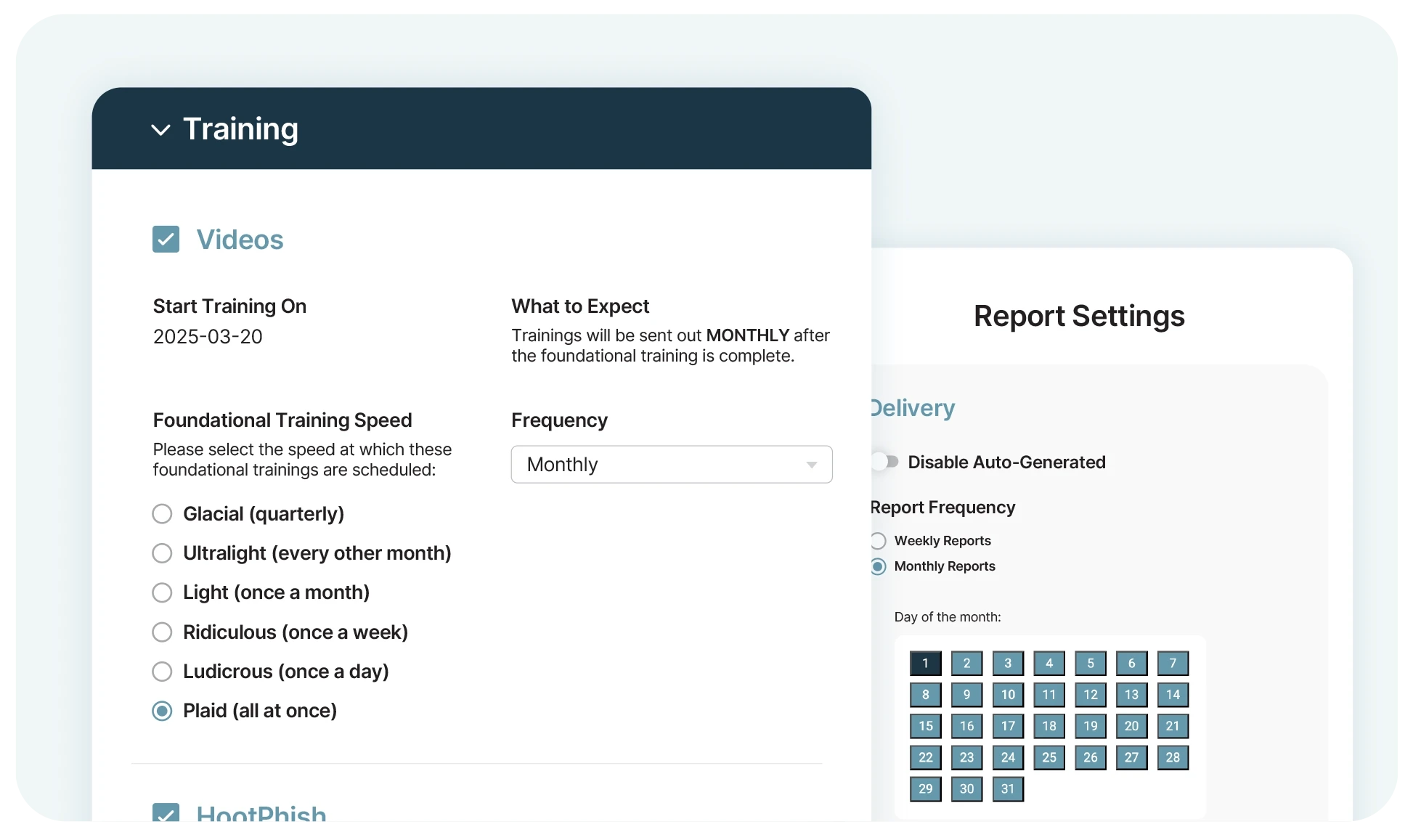
Automated schedules, reminders and reports handle all the tedious work of security awareness management.
A proven, positive reinforcement approach to training builds lasting behavioral change that safeguards your business.
Customize training the way that works for your organization, with modular power-ups that provide seamless protection, without the expensive investment.
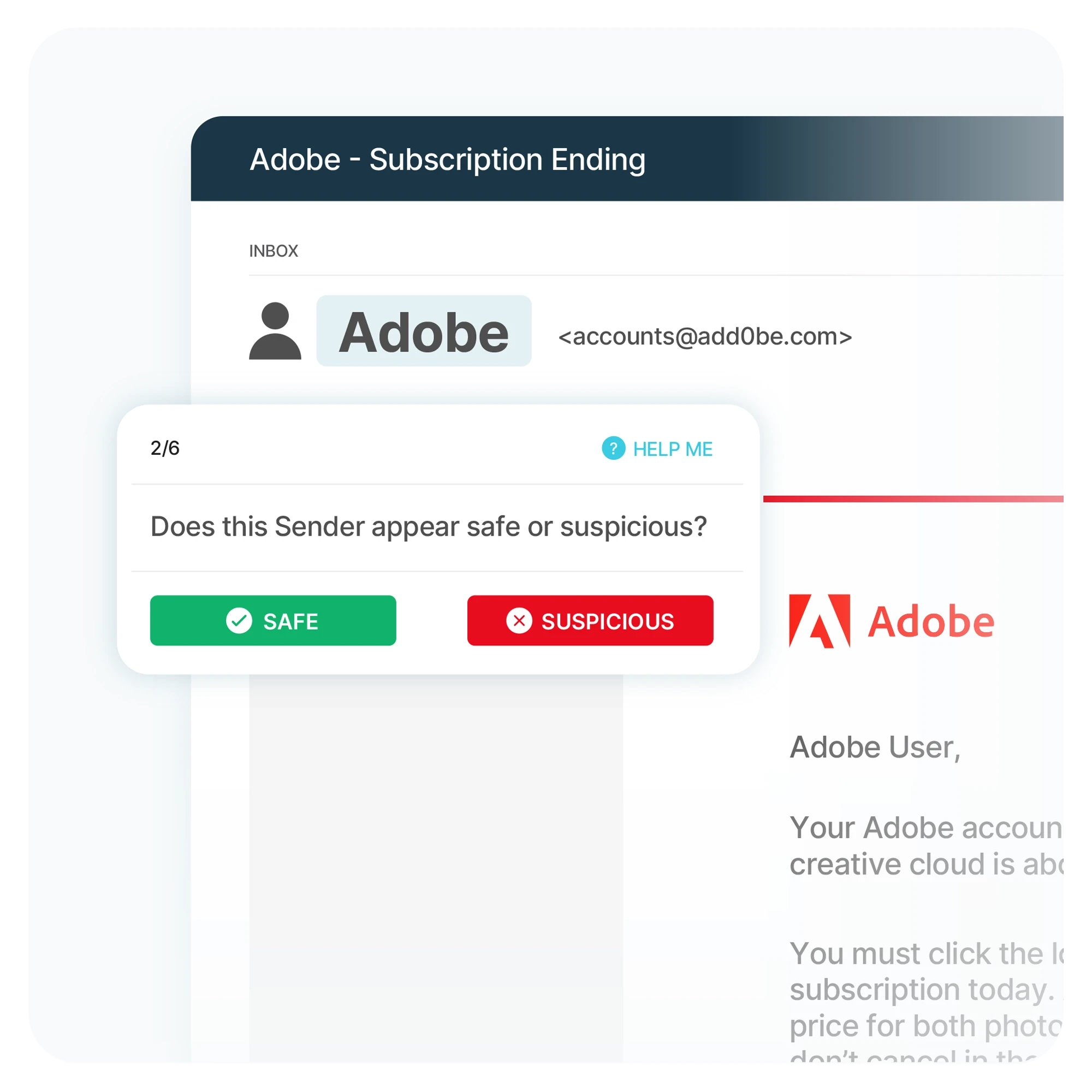
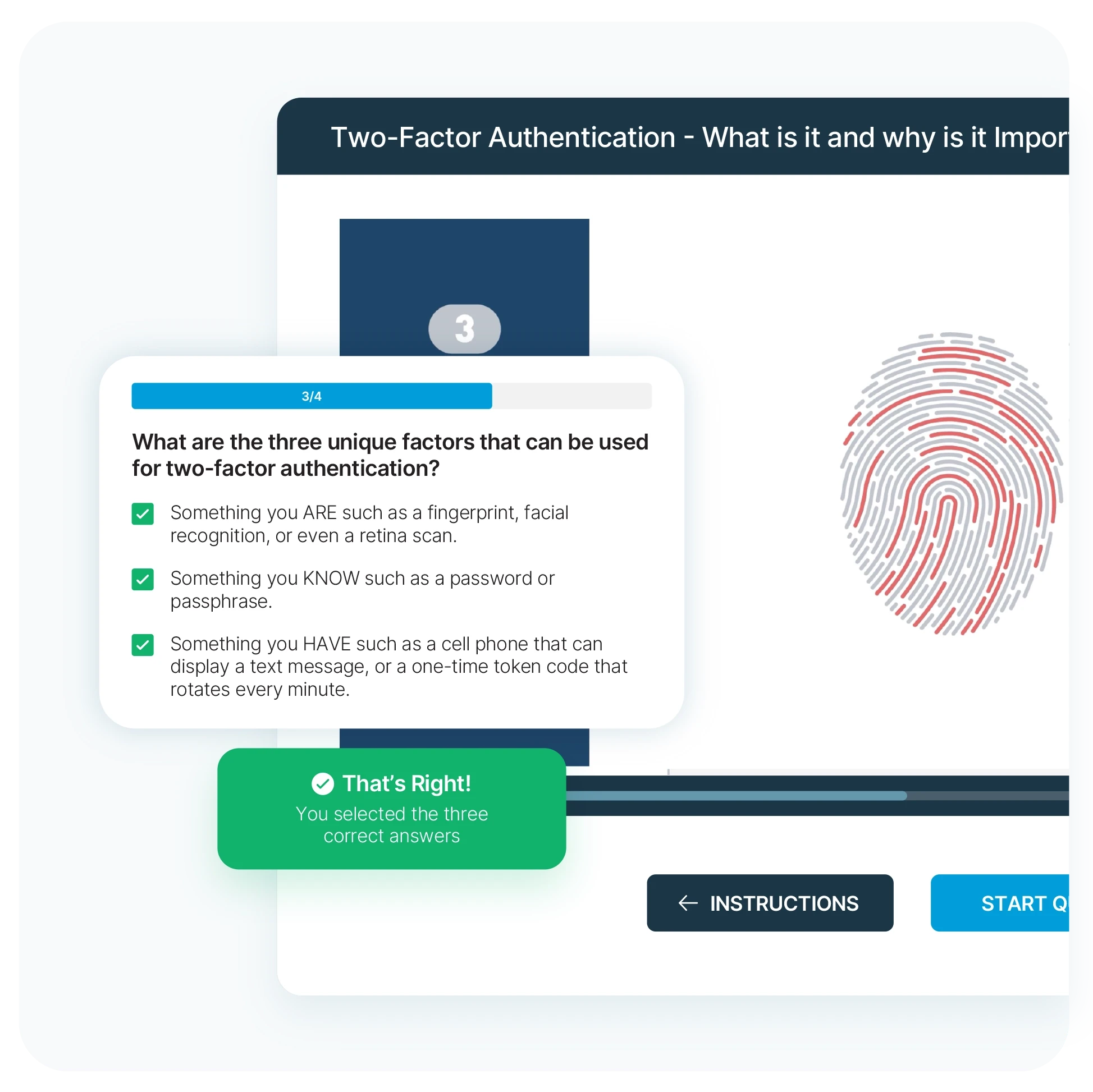
Transform traditional phish testing with interactive training that walks users through real phishing scenarios.
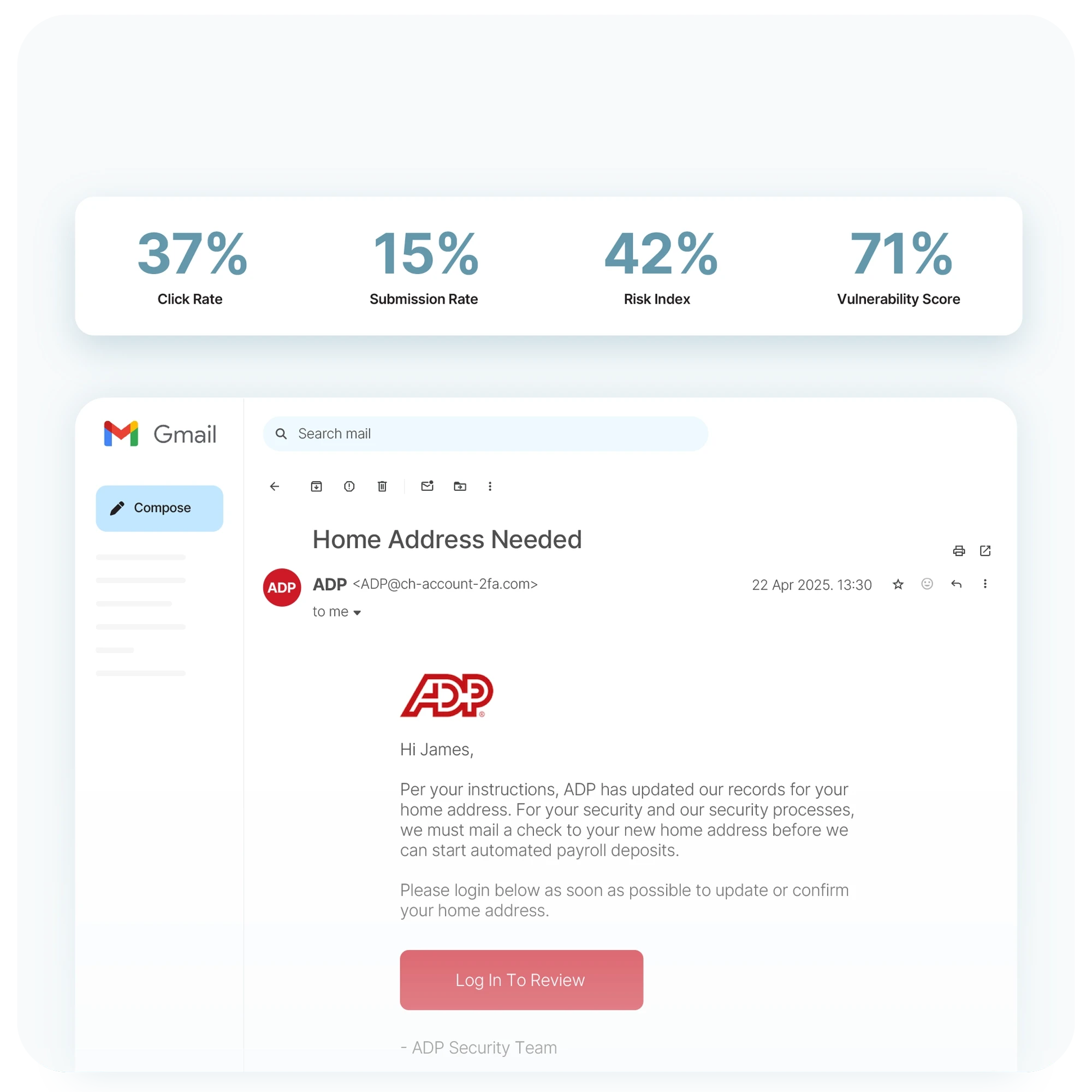
Send realistic phishing emails that give you meaningful insights into your organization’s security readiness.
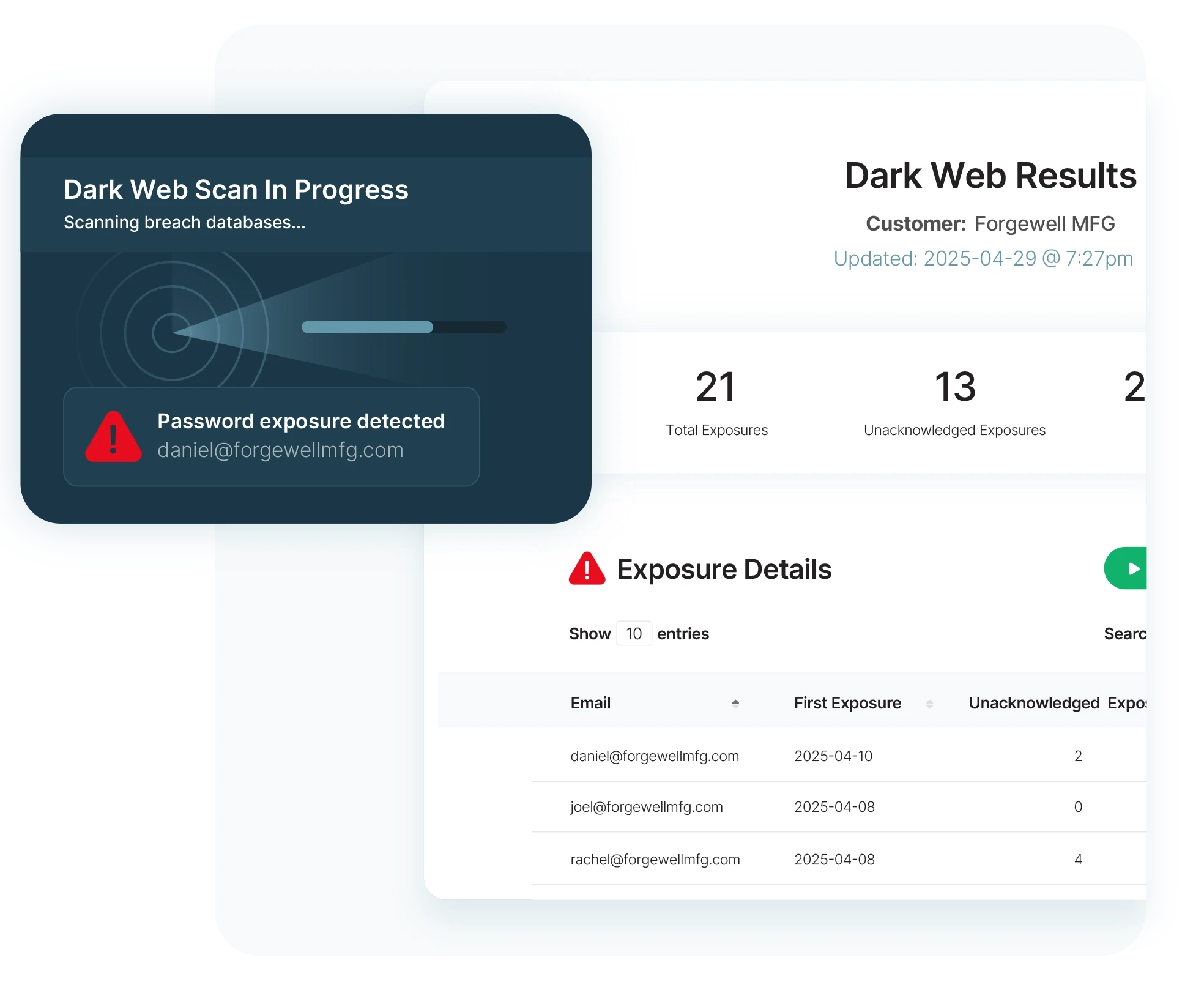
Continuously scan the dark web for exposed organizational credentials and compromised employee information.

Deploy automated security awareness videos on your schedule, and keep your entire organization updated on the latest threats and best practices.
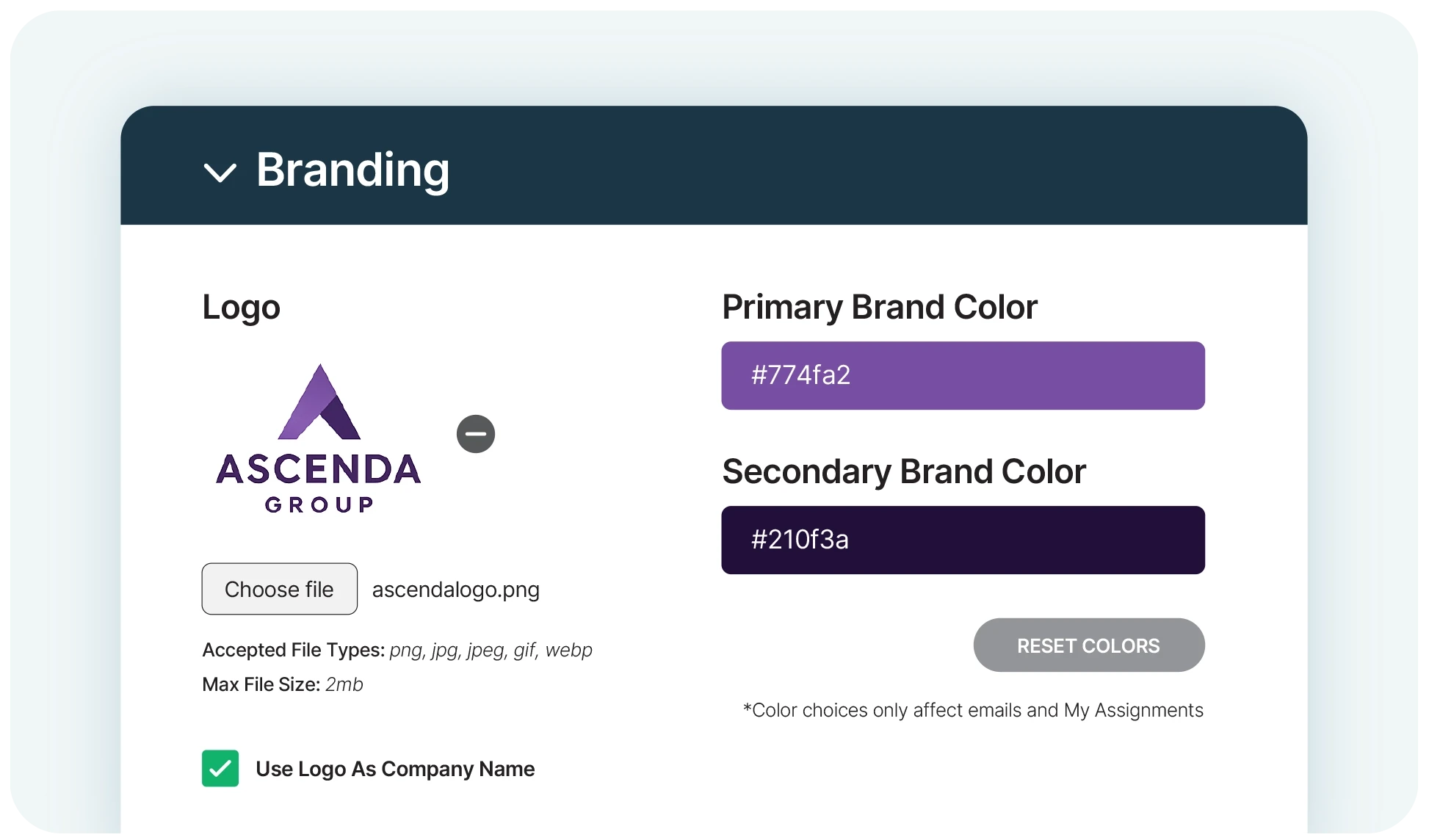
Brand CyberHoot as your own with customizable logos, colors and a unique identity for every client.
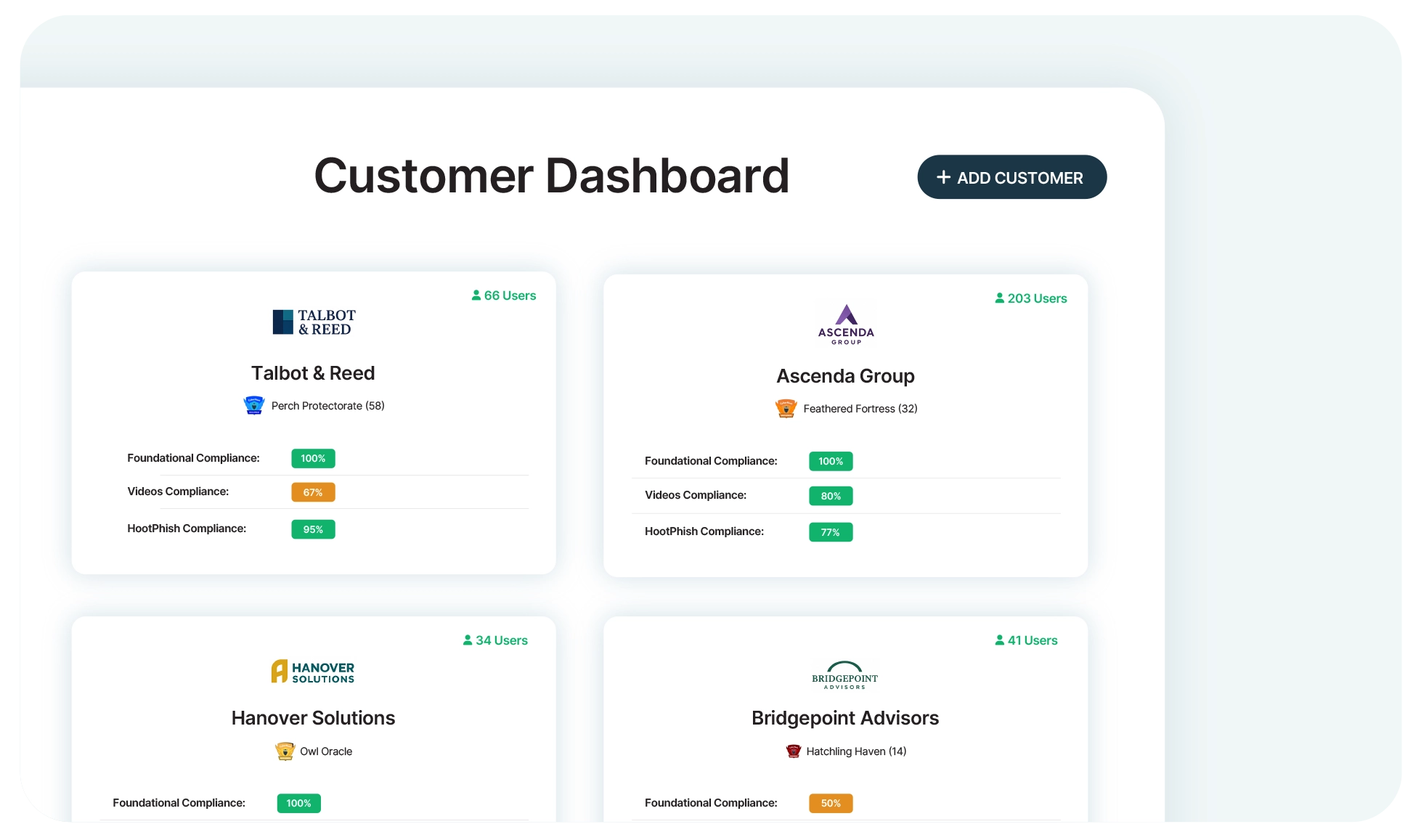
Protect multiple departments or clients from one place, with an adaptable platform that grows with your business.
‘Set and forget’, with training tools that need no user logins, no administration and no manual reporting.
CyberHoot integrates effortlessly with your existing tech stack – including EntraID and Google Workspace – to save the time and effort of switching between tools.



Eliminate the frustration of forgotten passwords and reduce your management time with direct link logins.
Deploy CyberHoot training in over ten different languages to make sure your global team is always security aware.
Get all the white-glove guidance you need to tailor your training program, including one-to-one onboarding meetings.
Simply add your user list and send an instant, automated notification about the new training.
Automatically send assignments to employees with no need to sign up or login.
Automate all reminders, escalations to managers and progress reports for admins.
Set your preferred frequency for an automated Cybersecurity compliance and progress report.
Get sharper eyes on human risks, with the positive approach that beats traditional phish testing.
