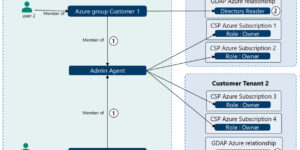
Granular Delegated Admin Privileges (GDAP)
Microsoft’s Granular Delegated Admin Privileges (GDAP) is a way of assigning specific administrative permissions to individuals or groups within an organization through Microsoft Azure. This approach enables a more refined …