"Cybersecurity training is complicated, partnering with CyberHoot keeps it simple. Our users are engaged with little administrative overhead."

A brushing scam is a deceptive tactic where online sellers or scammers send unsolicited packages...
Read more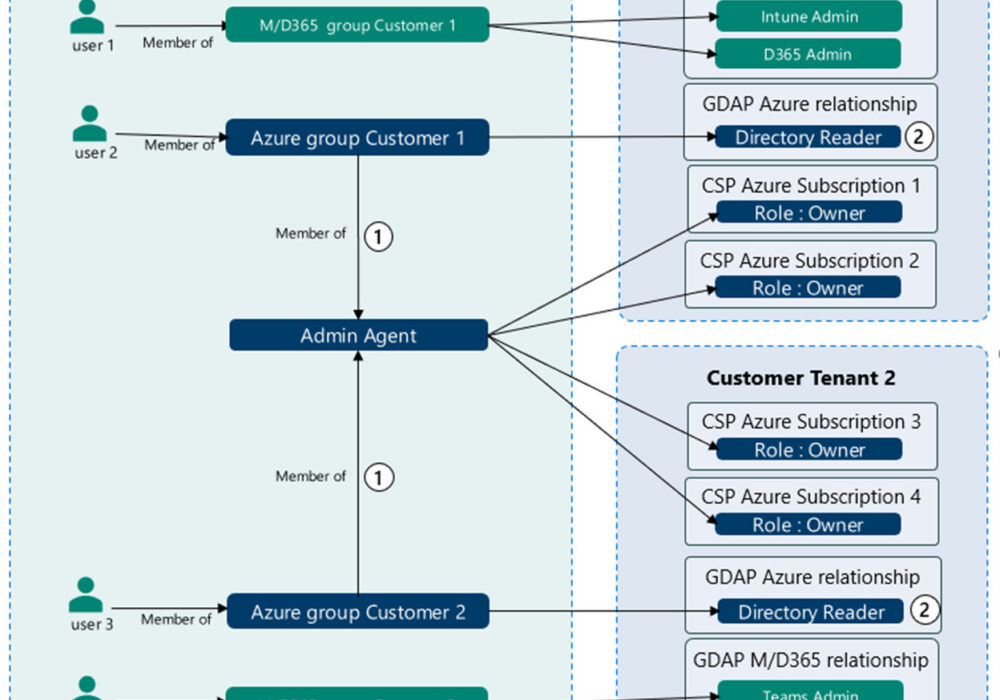
Microsoft's Granular Delegated Admin Privileges (GDAP) is a way of assigning specific...
Read more
Advertising Clean Room An "advertising clean room", also referred to as a Data Clean Room (DCR), is a term used...
Read more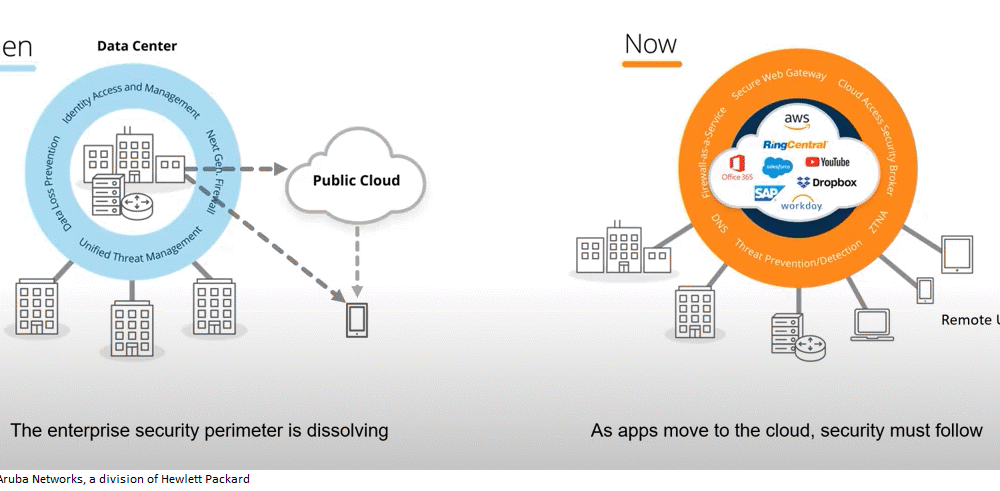
SASE Secure Access Service Edge (Pronounced: Sassy) SASE is a term coined by Gartner in 2019 to describe an...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Time-To-Live (TTL) is a value for the period...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Call Admission Control (CAC) is the method...
Read more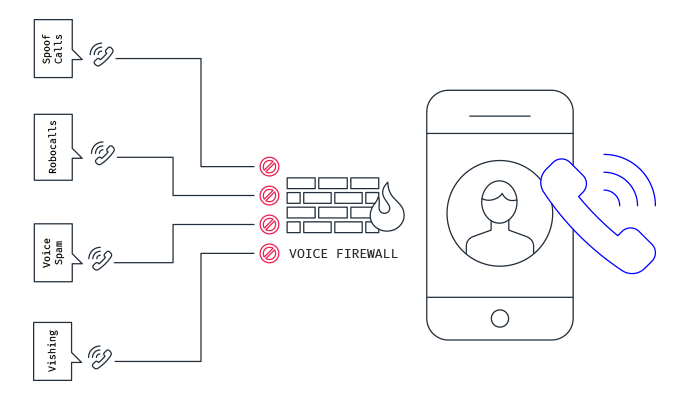
Source: Mobileum Secure your business with CyberHoot Today!!! Sign Up Now A Voice Firewall...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Traceroute is a network diagnostic tool used...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now A HoneyMonkey is a system created by...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
