"While it is well known that there are many cyber security threats, sorting out how to protect yourself without accidentally exposing yourself can be a daunting task. For a small organization like ours, this type expertise and time to research..."

End-to-End Encryption (E2EE) is a method of securing digital communications so that only the sender and the...
Read more
Operational Disruption is any unexpected event, failure, or interruption that prevents normal business processes,...
Read more
Microsegmentation is a security technique that divides a network into smaller, isolated zones down to the...
Read more
A brushing scam is a deceptive tactic where online sellers or scammers send unsolicited packages...
Read more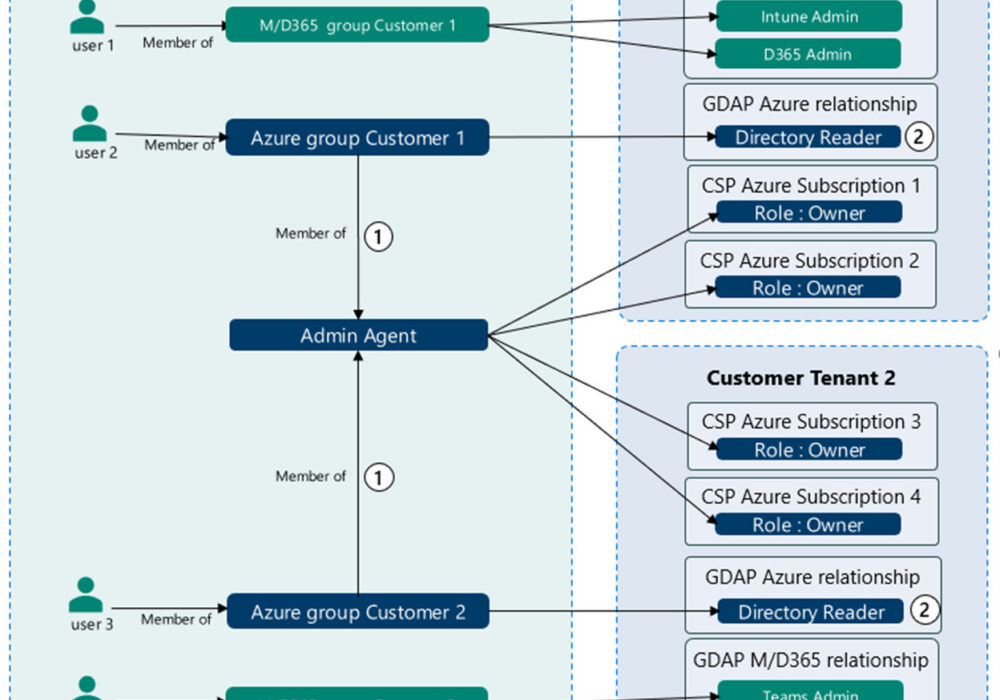
Microsoft's Granular Delegated Admin Privileges (GDAP) is a way of assigning specific...
Read more
Advertising Clean Room An "advertising clean room", also referred to as a Data Clean Room (DCR), is a term used...
Read more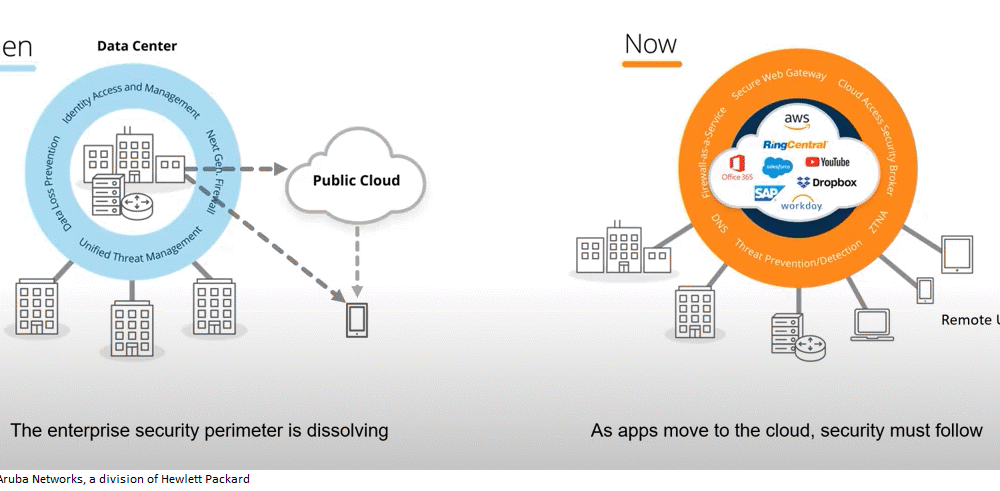
SASE Secure Access Service Edge (Pronounced: Sassy) SASE is a term coined by Gartner in 2019 to describe an...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Time-To-Live (TTL) is a value for the period...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Call Admission Control (CAC) is the method...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
