
The SQL Slammer Virus, also known as the Sapphire Virus, is malware in the form of a worm that caused a Denial of Service on many internet hosts in 2003, and caused thousands of network outages and even dramatically slow down Internet traffic! The worm spread rapidly, infecting the majority of its 75,000 victims within ten minutes. This worm exploited a vulnerability in Microsoft’s SQL Server.
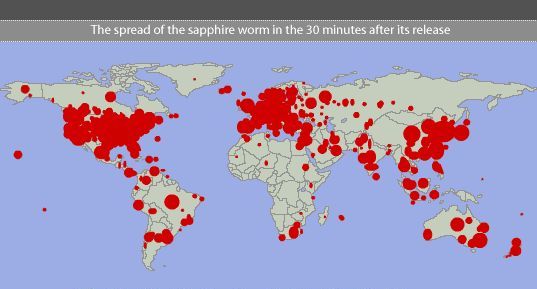
Social isolation is the 2020 solution to flatten the curve on Coronavirus infections. In 2003 preventing the spread of SQL Slammer required network Isolation (blocking TCP 1434 – SQL’s communications port). However, as witnessed by the COVID-like map from 2003, due to the speed of computer infections, network isolation couldn’t be put in place fast enough to stop the spread of SQL Slammer. Whether the world has learned enough to put social isolation in place quickly enough to slow and stop the spread of COVID19 remains to be seen.
Related Topics: ILOVEYOU Virus, Coronavirus Advisory
Source: NC State Study
The SQL Slammer worm costs companies an estimated $750 Million to over $1 Billion in damages. In this case the risks were easily avoided if these companies had patched their systems. Therefore, as a business owner, make sure your company’s cybersecurity program includes the following protections:
These seven measures are all defense-in-depth cybersecurity strategies for lowering your risk.
https://www.youtube.com/watch?v=HH2_m4BqJZo
Discover and share the latest cybersecurity trends, tips and best practices – alongside new threats to watch out for.

A guide to spotting senior executive impersonation scams before the fake CEO gets a real wire transfer. It...
Read more
Artificial Intelligence (or AI) is making phishing emails smarter, malware sneakier, and credential theft easier...
Read more
DocuSign has become one of the most trusted tools in modern business. Contracts, HR paperwork, NDAs, vendor...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
