"CyberHoot is a great option for Cybersecurity for our schools. The videos and other training are very user-friendly. Their support is fantastic as well."
Discover and share the latest cybersecurity trends, tips and best practices – alongside new threats to watch out for.

Secure your business with CyberHoot Today!!! Sign Up Now Time-To-Live (TTL) is a value for the period...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Call Admission Control (CAC) is the method...
Read more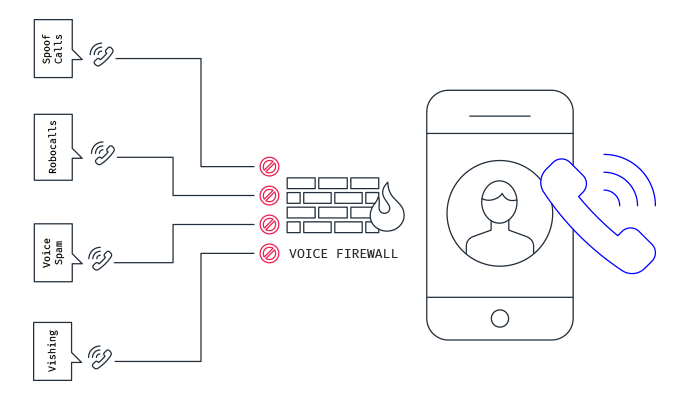
Source: Mobileum Secure your business with CyberHoot Today!!! Sign Up Now A Voice Firewall...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Traceroute is a network diagnostic tool used...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now A HoneyMonkey is a system created by...
Read moreSecure your business with CyberHoot Today!!! Sign Up Now The Universal Authentication Framework...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Indicators of Compromise (IoC) are pieces of...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Extended Detection and Response (XDR) is...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Fast Identity Online (FIDO) is a set of...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Active Directory...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
