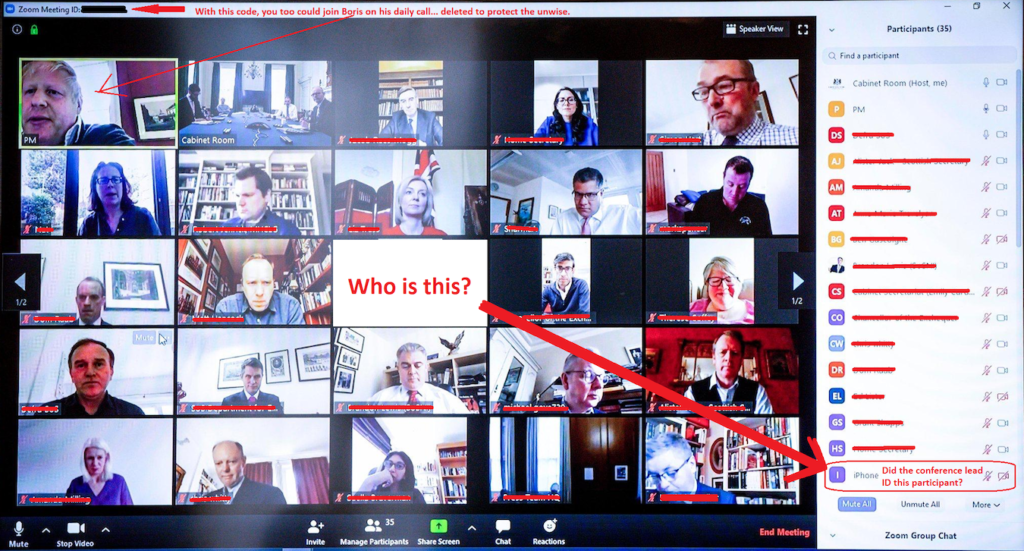
Zoom Bombing is where an unauthorized person enters your Zoom video conference to cause disruptions or to gain sensitive information. Many companies and schools have begun using video conferencing extensively and there’s been numerous news reports of “zoom bombing” problems. While Zoom appears to be taking the brunt of the complaints on securing Web Conferencing, it’s important to realize any web conference can be attacked and to take precautions by securing your meetings appropriately. Read on for information on how to secure your Zoom meetings and be sure to watch the “How To” video which reviews the critical Zoom Security features you need to enable and features to disable to secure your Zoom meetings from being bombed.
Source: CBS Boston
Additional Reading:
‘Zoom-Bombing’ Hijacks Online Class Meetings In Massachusetts, FBI Warns
What does this mean for an SMB or Schools?
- If you are the host of the meeting, make the meeting private, requiring a password or private link to join the conference call;
- When the meeting is made private, control access to the meeting by enabling the “waiting room” feature so you can manually let authorized people into the meeting; you would get a message similar to, “Bob Johnson would like to join the meeting” and would need to approve;
- Do a roll call and keep track of the amount of users that are supposed to be in the meeting, if you invited 8 users and there are 10 in the meeting, you may want to check out who the two (2) extra users are;
- Don’t share the meeting ID, password, or meeting link on a public platform, such as your website or related social media site;
- Once every authorized user has joined the meeting, lock the meeting so nobody else can join;
- Only allow the Conference Host to have control of screen sharing;
- Disable file-sharing so people aren’t flooded with content.
Specific Zoom Settings to Examine
The following are recommended settings for hardening your Zoom Meetings:
- Participant video off on join
- Join before host off
- Require a password when scheduling new meetings on
- Require password for participants joining by phone on
- Mute participants upon entry on
- Chat on (group chat)
- Private Chat off
- Co-host on
- Allow the host to put attendee on hold on
- Allow removed participants to rejoin off
- Waiting room on
To learn more about Zoom Bombing, watch this short 2 minute video:
If you would like a walkthrough of securing Zoom for your business or school, watch this video:
April 10th, 2020 Editor Updates
An email update on security improvements direct from Zoom's CEO Eric Yuan:
https://cyberhoot.com/uncategorized/zoom-security-update-from-their-ceo-eric/
April 15th, 2020 Editor Update
Zoom awarded Leaders Quadrant status by Gartner. Alongside Cisco WebEx and Microsoft Teams.
http://click.zoom.us/e/84442/gartner-zcid-1564/98wf2c/1548053644?
Links to Web Conferencing Solution Reviews
CyberHoot clients have been asking “should I switch to another Web Conferencing tool that is more secure?”. My response is, it depends. It’s now coming to light that other Web Meeting companies may have their own security challenges. For example, GoToMeeting.com allegedly has some cookie and privacy issues being reported about their website. Zoom may become the safest Web Meeting tool available due to the scrutiny it is facing today.
Video Conference Software Review Articles
Secure Alternatives to Zoom Article from Vice.com
Forbes.com article with 5 alternatives to Zoom
