"CyberHoot lets us access expert cybersecurity guidance without hiring a full-time specialist."
High-Level Instructions: This HowTo video walks you through allow-listing CyberHoot’s Mail-Relay by either...
Read more
The Coronavirus has been on the front of everyone's mind lately, causing fear and concern across the...
Read more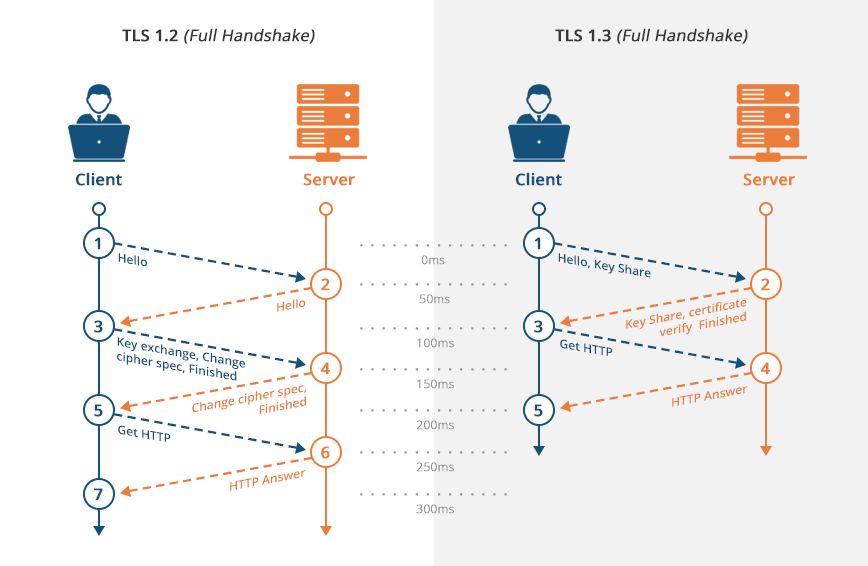
Transport Layer Security (TLS) is a security protocol made for privacy and data security for...
Read more
Dissemination of Information refers to the distributing of a company's or customer specific information to the...
Read more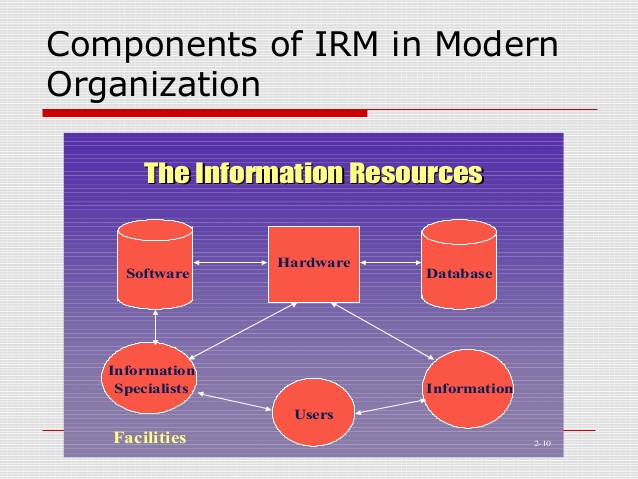
Information Resources Management (IRM) is the planning, budgeting, organizing, directing,...
Read more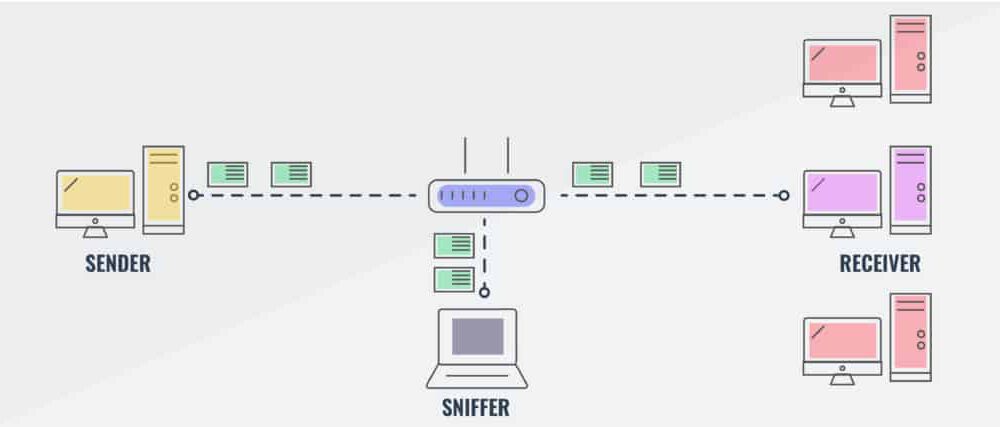
Packet Sniffing is the practice of gathering, collecting, and logging the packets that pass through a...
Read more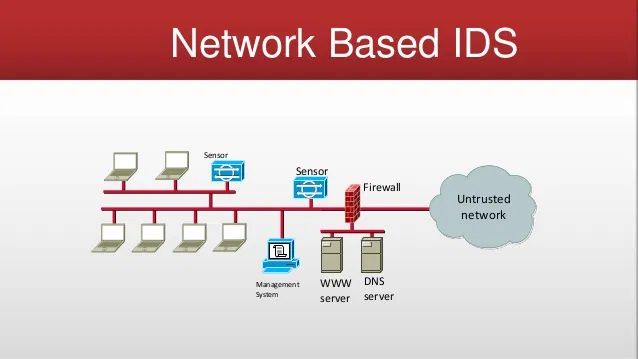
A Network Based Intrusion Detection System (NIDS), or Network Based IDS, is security hardware that is placed...
Read more
SQL Slammer Spread 30 min Coronavirus Spread 90+ Days The SQL Slammer Virus, also known as the Sapphire Virus,...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
