"Using CyberHoot was one of the best decisions we made regarding SAT. Fully automated, training is interesting, staff participation is high compared to other vendors."

Governments across the world are starting to realize how important cybersecurity really is....
Read more
General Information, also known as Public information, is data that is commonly found in marketing...
Read more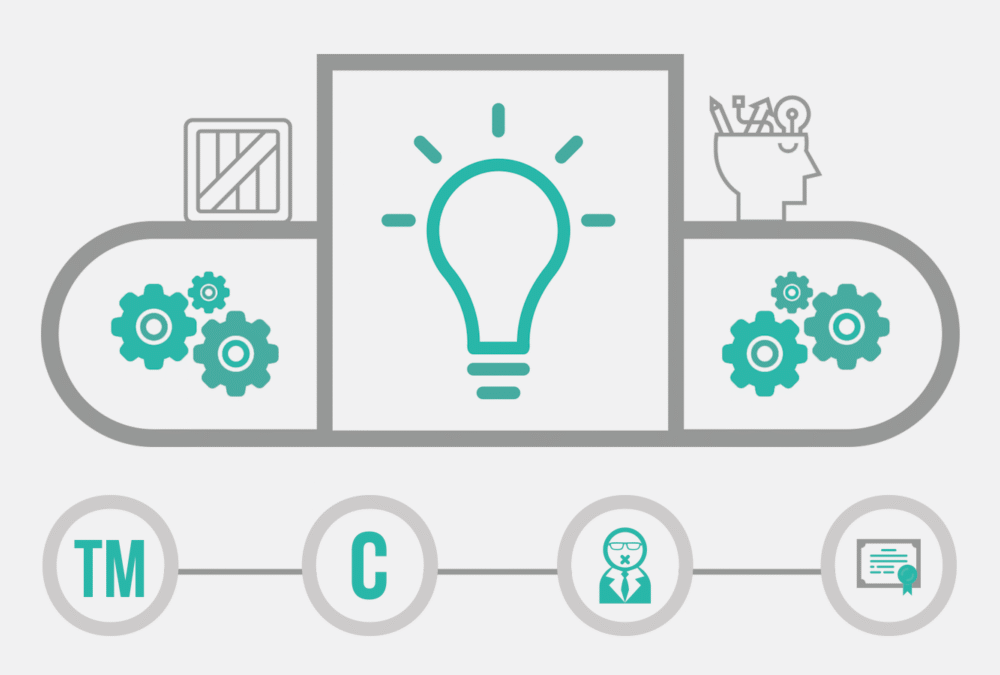
Intellectual Property (IP) refers to the ownership of a specific idea, design, manuscript, etc. by the...
Read more
The ILOVEYOU Virus, also known as, the Love Bug, is a computer worm that infected over 10 million...
Read more
This HowTo video outlines how to restore an archived user or employee in a Training Program. When an archived...
Read more
Mandatory Controls, also known as Mandatory Access Controls (MAC), are a type of access control that restricts the...
Read more
Discretionary Access Controls, also known as DAC, are types of cybersecurity measures that allow or restrict...
Read more
Sensitive (or restricted) Information is data from a company or organization that is generally not regulated but...
Read more
Critical (or Confidential) Information in a Small to Medium-sized Business (SMB) is most easily understood to be...
Read more
Clearview AI has created one of the broadest and most powerful facial recognition databases in the...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
