"CyberHoot lets us access expert cybersecurity guidance without hiring a full-time specialist."

The Active Cyber Defense Certainty Act (ACDC), also known as the "Hack Back" bill was first introduced...
Read more
The Morris Worm goes down in history as the first worm in existence. This self repeating computer...
Read more
Crypto-Mining, also known as Cryptocurrency Mining, is a process in which transactions of various...
Read more
A Brute Force Attack is a strategy used by hackers trying to break into your data, password, or...
Read more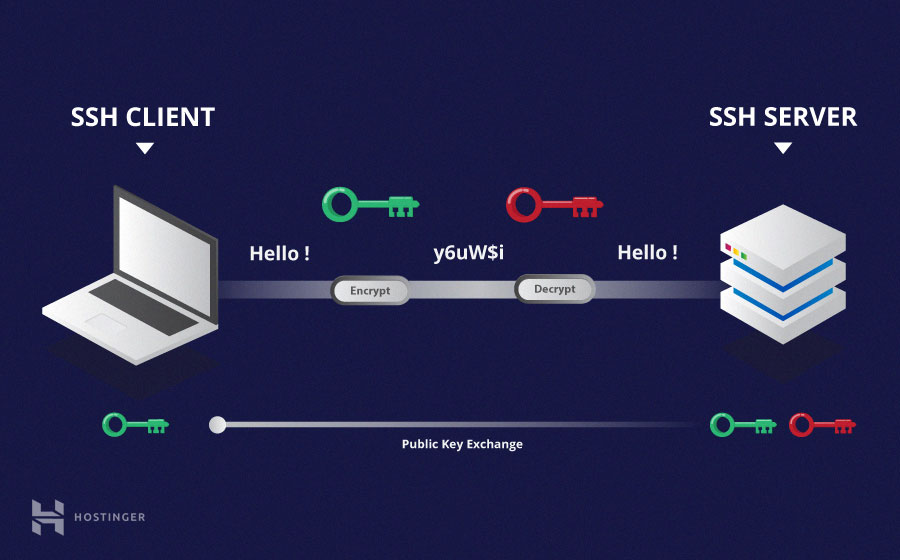
Secure Shell (SSH) is a cryptographic network communications protocol for operating network...
Read more
Password Cracking refers to the various methods hackers use to learn exactly what password you use to...
Read more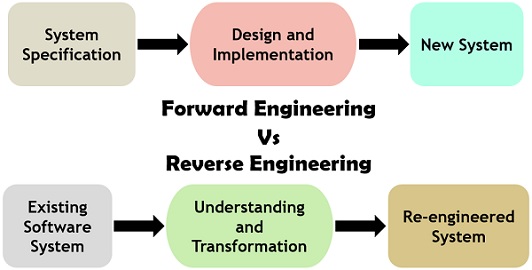
Reverse Engineering occurs when you take a finished product and work backward to determine how it was...
Read more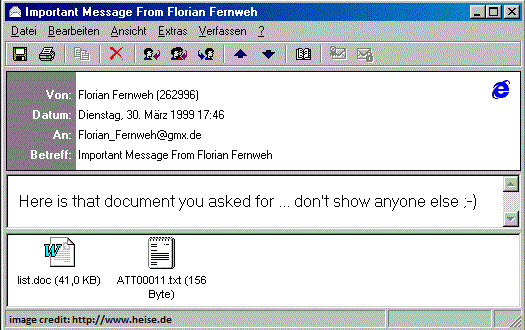
The Melissa Virus is malware that was was deployed in late March of 1999. A programmer by the name of...
Read more
Reverse Intent the name given to a common hacker technique of flip-flopping a piece of security...
Read more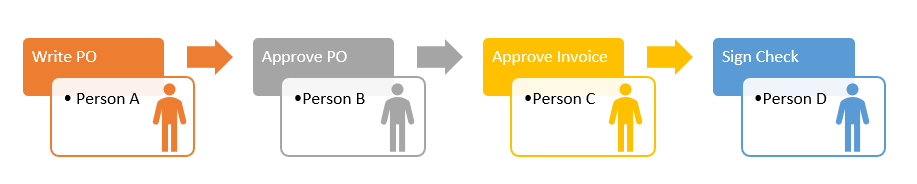
Separation of Duties involves dividing roles and responsibilities to minimize the risk of a single...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
