"While it is well known that there are many cyber security threats, sorting out how to protect yourself without accidentally exposing yourself can be a daunting task. For a small organization like ours, this type expertise and time to research..."

In today’s cybersecurity landscape, breaches are rarely caused by a lack of technology. Instead, they stem from...
Read more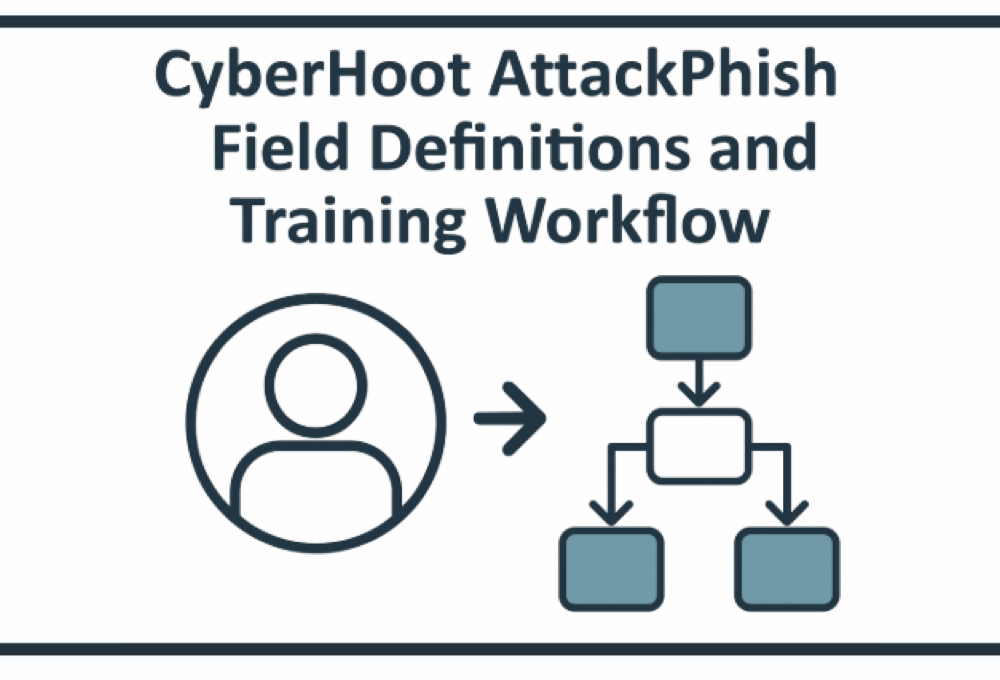
This document explains how CyberHoot AttackPhish populates the various tracking fields when running phishing...
Read more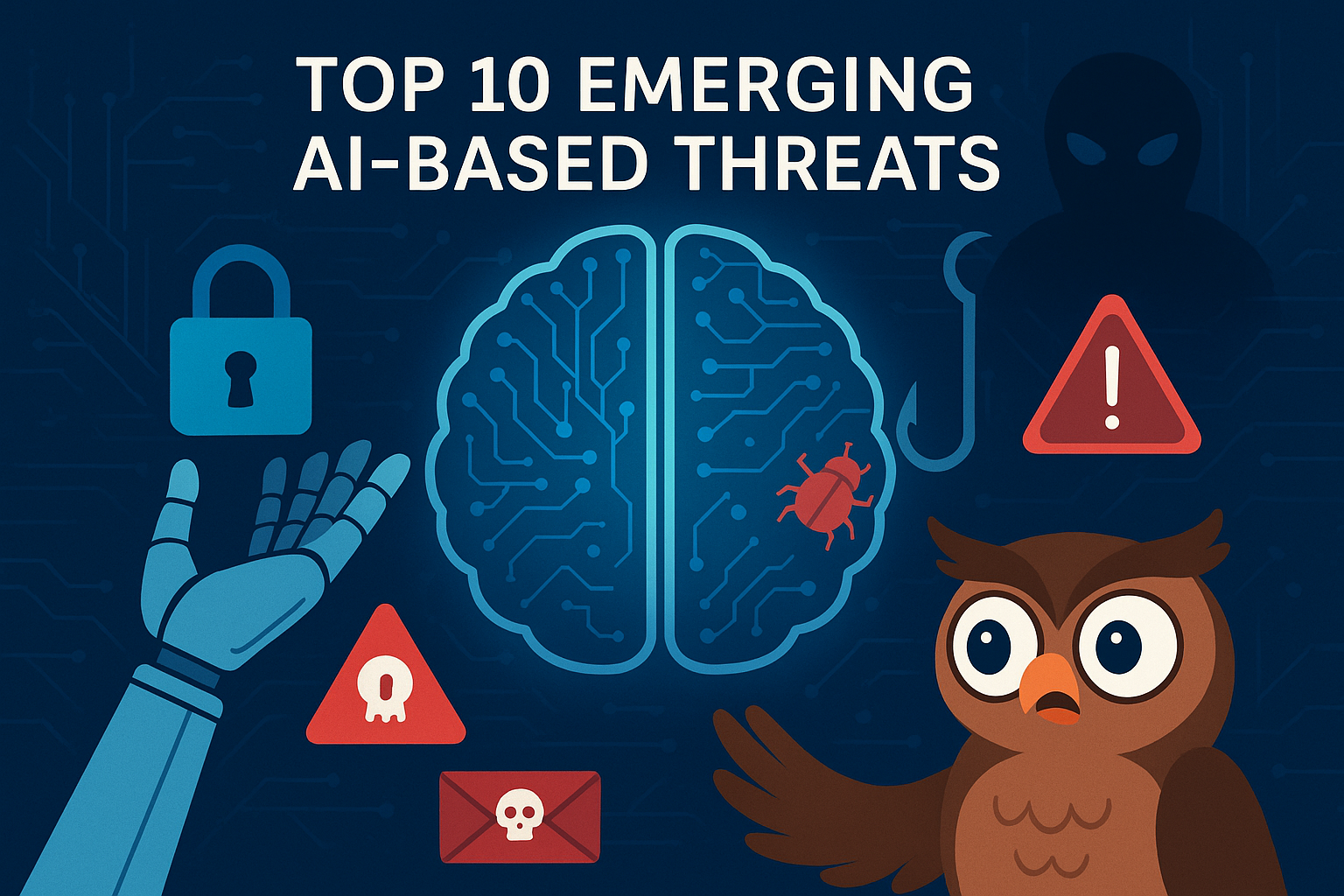
Artificial Intelligence (AI) is transforming productivity and efficiency, but it’s also arming cybercriminals...
Read more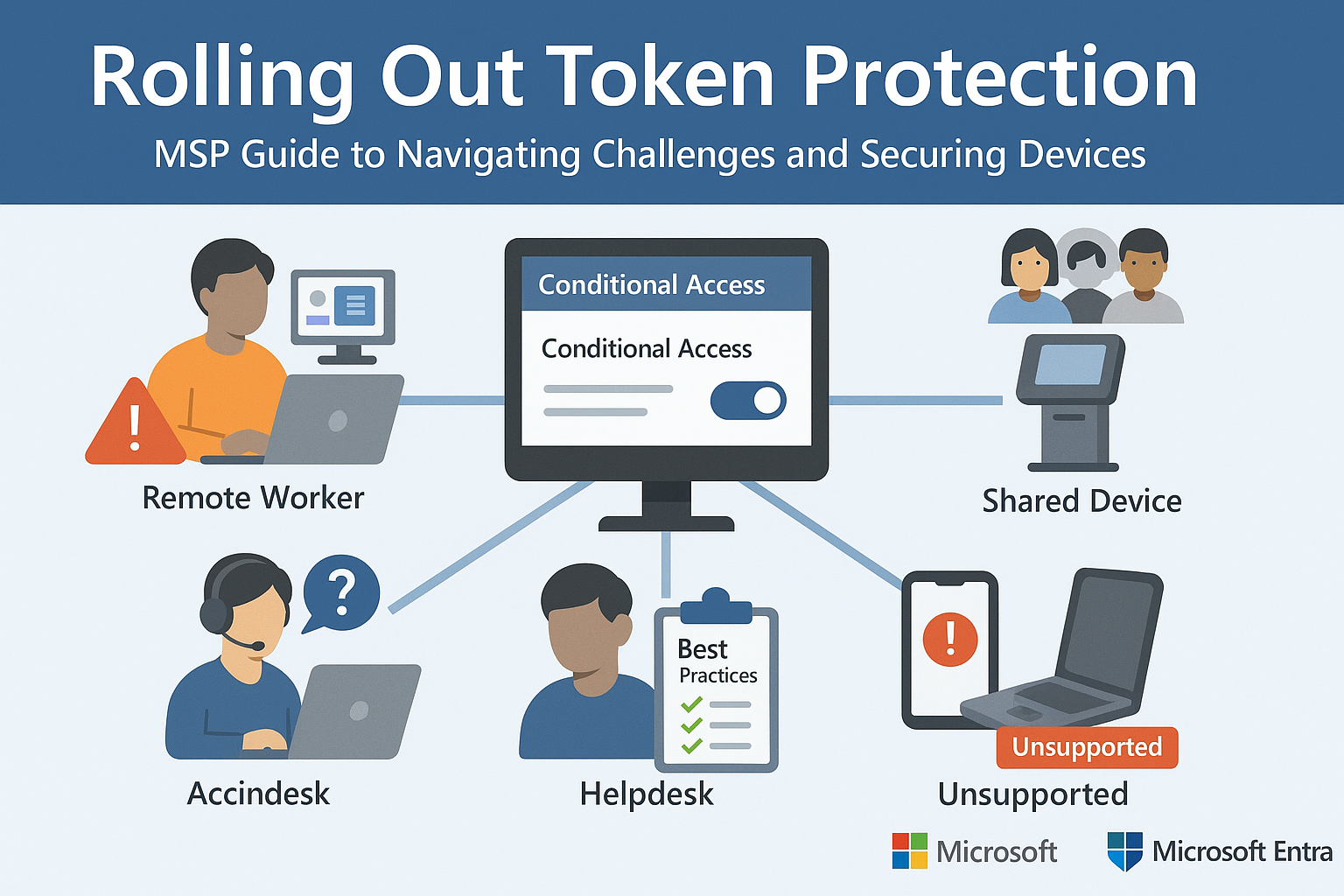
Part 2 of Our Microsoft Entra Security Series In Part 1, we explored how Microsoft’s Token Protection...
Read more
Malvertising is short for malicious advertising. It refers to the use of online ads to deliver malware to...
Read more
Privacy-Enhancing Computation (PEC) refers to a set of technologies and methods that allow organizations to...
Read more
Clear Text (or plaintext) is data that is stored or transmitted without any form of encryption or obfuscation. In...
Read more
Privileged Access Management (PAM) is a cybersecurity framework and set of tools designed to secure, manage, and...
Read more
Identity Management (IDM) is the framework of policies, processes, and technologies used to ensure the right...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
