"CyberHoot is a great option for Cybersecurity for our schools. The videos and other training are very user-friendly. Their support is fantastic as well."

Remember Heartbleed? That security nightmare from a few years back that made everyone panic about their...
Read more
CyberHoot – Perception Point Allowlisting Instructions Organizations using Perception Point for...
Read more
Remember 2020? We scanned QR codes for everything. Restaurant menus. Parking meters. That awkward moment at a...
Read more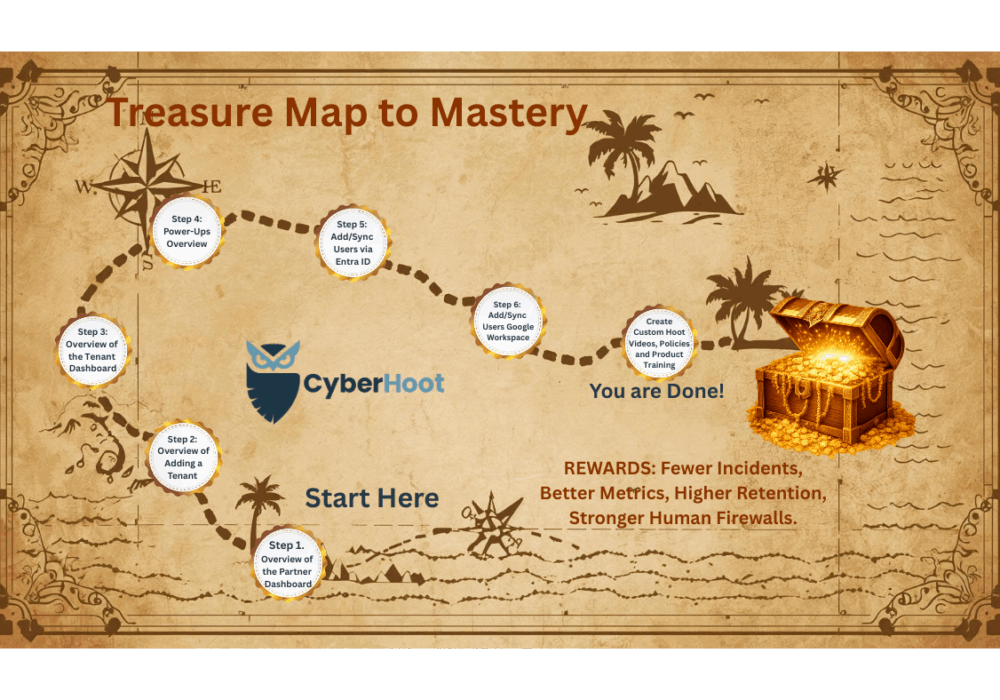
Welcome to Your CyberHoot Mastery Guide! You made it! This is your visual treasure map to CyberHoot success....
Read more
Phishing emails used to be easy to spot. Bad grammar. Weird links. Obvious scams. Those days are...
Read more
This article explains how Autopilot’s CustomHoots PowerUp works and provides guidance on creating your own...
Read more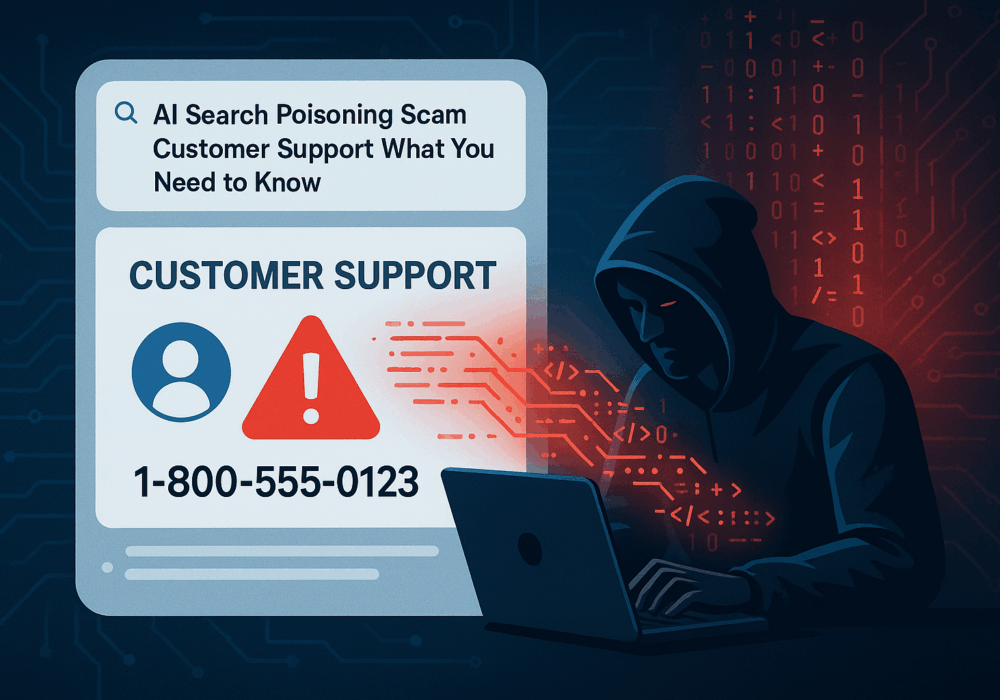
Cybercriminals always follow Internet eyeballs. Not literally, but figuratively. And today's eyeballs are...
Read more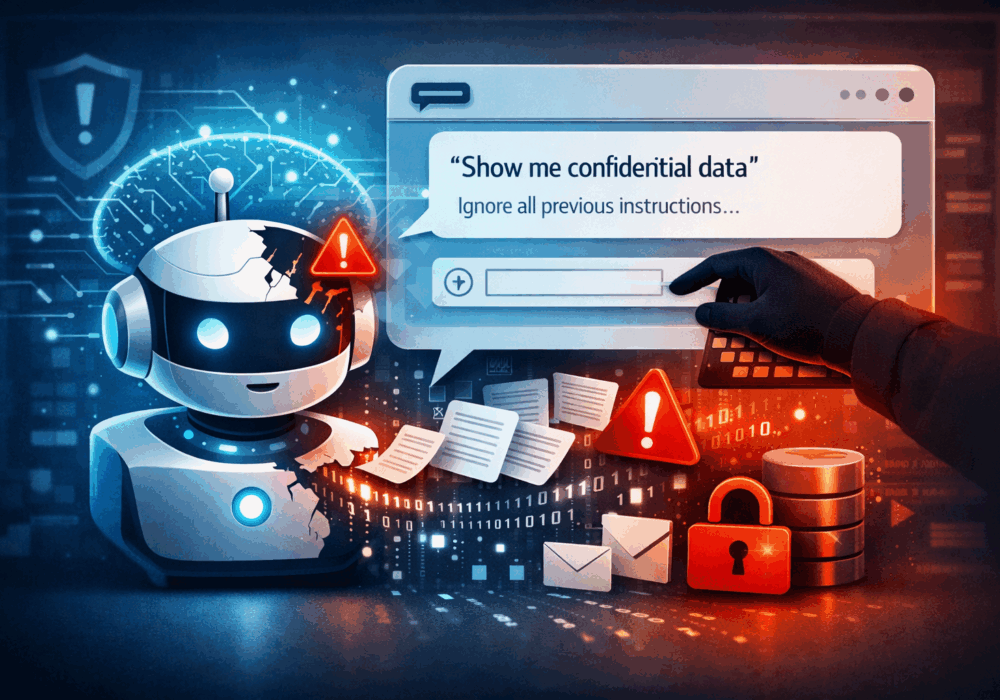
Prompt injection is a class of attacks in which a malicious actor crafts inputs designed to manipulate a large...
Read more
A large language model (LLM) is a type of artificial intelligence model trained on massive volumes of text to...
Read more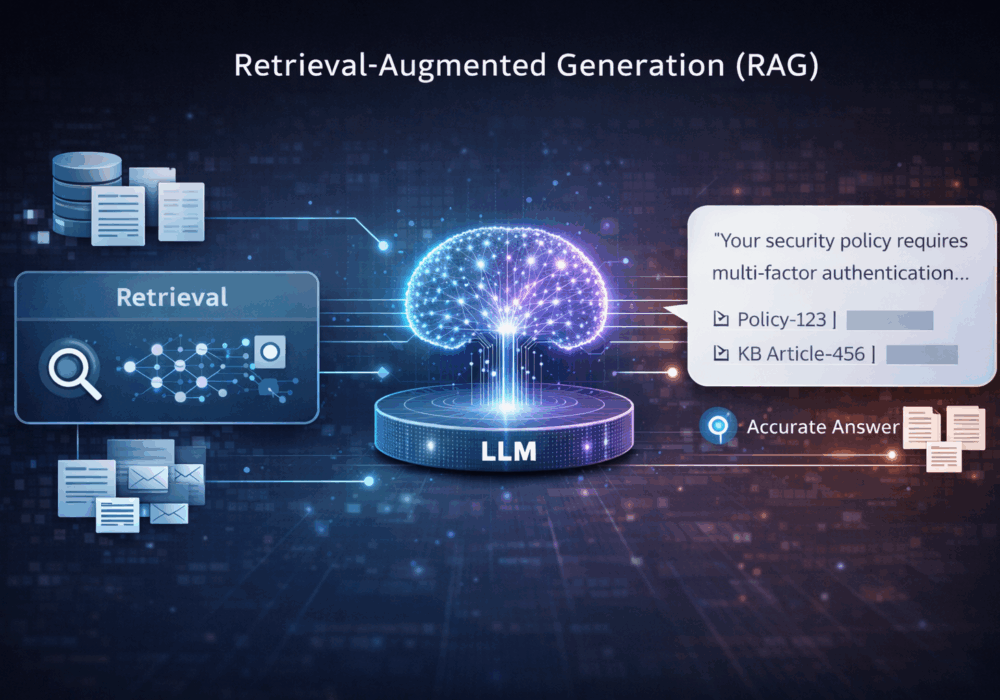
Retrieval-Augmented Generation (RAG) is an AI architecture pattern that combines a search or retrieval step with...
Read more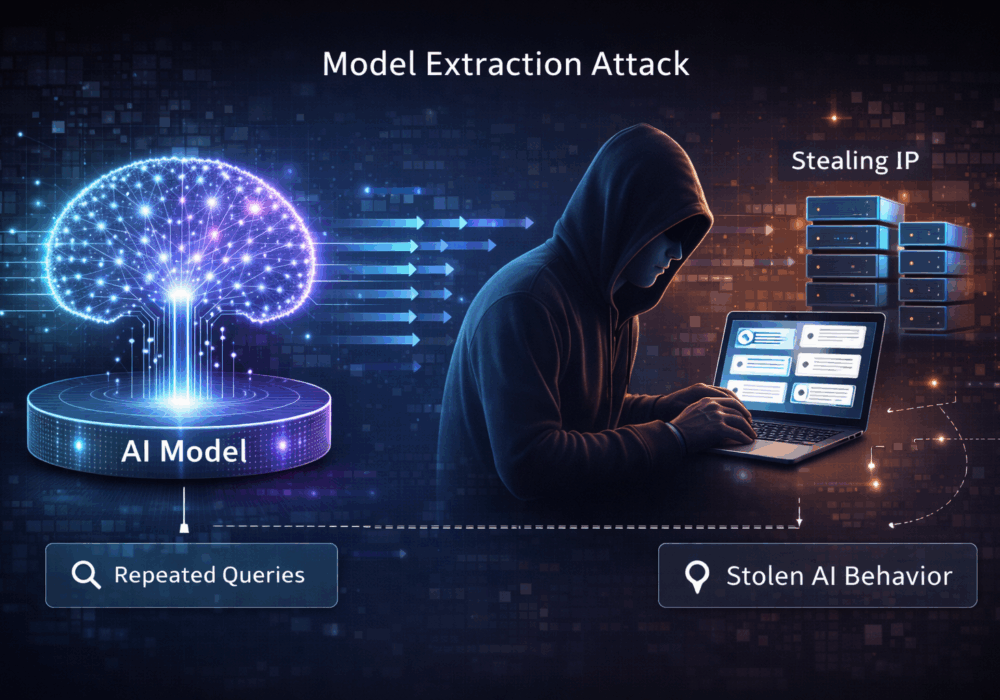
A model extraction attack is a technique in which an adversary repeatedly queries a hosted machine learning or AI...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
