"Managed Service Providers (MSP's) are constantly bombarded with new vendors and products that either overlap with a product already in our line cards or is difficult to get client buy in. Cyberhoot brings a new product/service to the MSP space..."
Data Confidentiality is the assurance that information is only accessible to authorized individuals and is not...
Read more
Data Integrity is the assurance that information remains accurate, complete, and unaltered from its origin to its...
Read more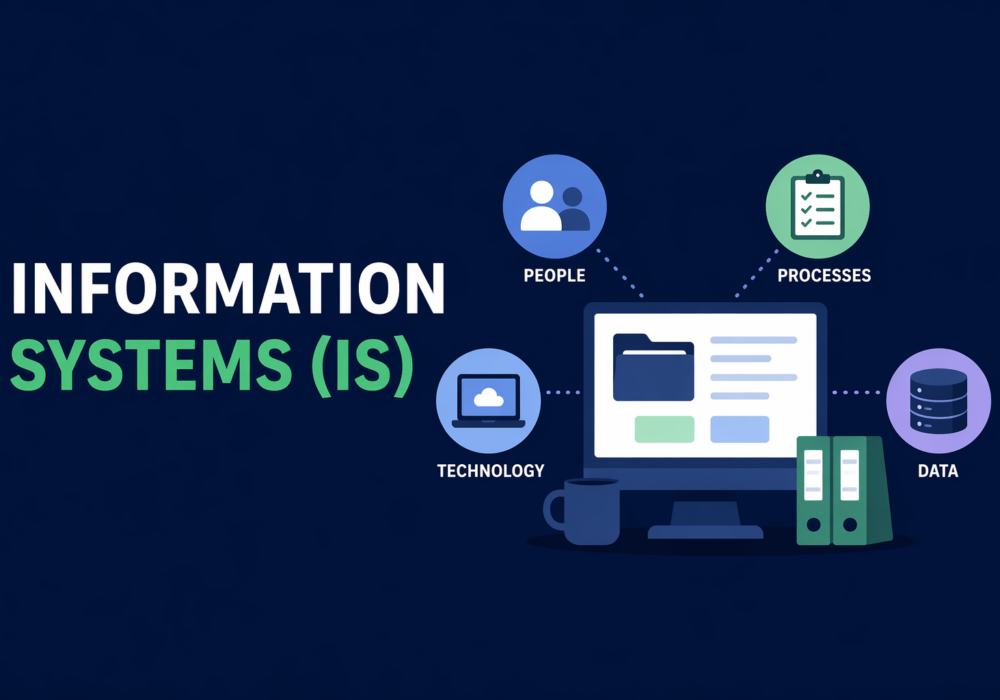
Information Systems (IS) are the organized collection, processing, maintenance, transmission, and dissemination...
Read more
A membership inference attack is a machine learning privacy attack in which an attacker tries to determine...
Read more
Chain of thought, or chain of thought prompting, is a prompt engineering technique where the user asks an AI...
Read more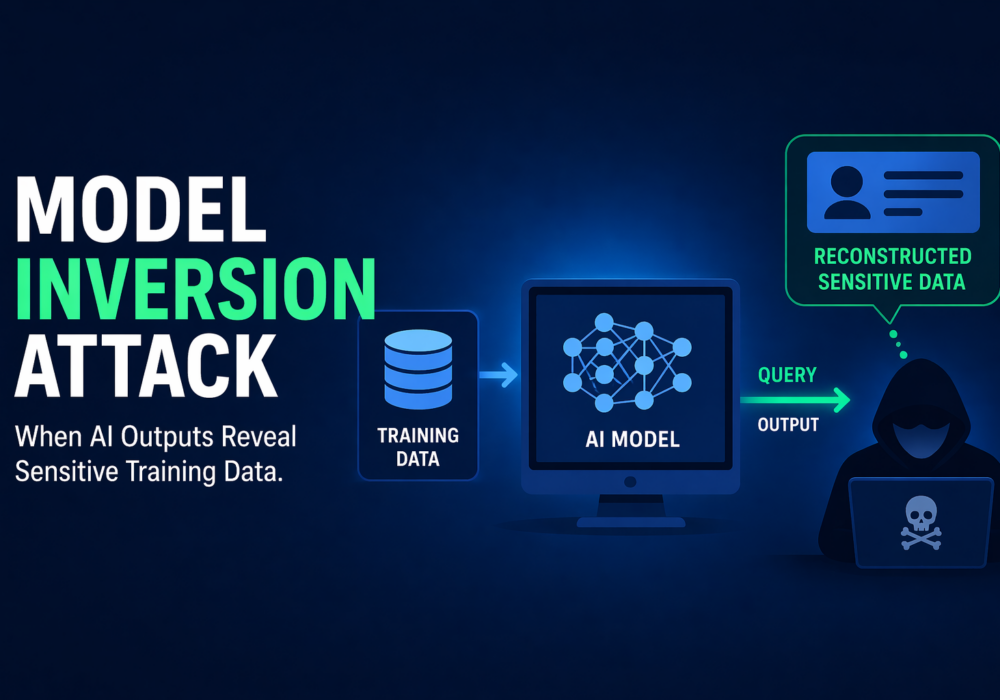
A model inversion attack is a machine learning privacy attack in which an attacker uses a model’s outputs to...
Read more
Adversarial Example / Adversarial Machine Learning (Adversarial ML) refers to techniques where attackers...
Read more
DocuSign has become one of the most trusted tools in modern business. Contracts, HR paperwork, NDAs, vendor...
Read more
And yes, Google's Gemini AI had no idea it was working for the bad guys. Malware has always followed a script....
Read more
Microsoft 365 Built-in “Report Phish” Integration 🔹Overview Microsoft 365 supports a...
Read more
Ransomware groups are not breaking in organizations the same way they did five years ago. The entry methods have...
Read more
If a Chrome extension promises to remove security pop-ups and generate MFA codes, that should make you...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
