"Craig and the CyberHoot team are great business partners! They are always open to enhancing their product, and ready to help my team with any deployment questions they may have. I am also an end user of the CyberHoot security..."
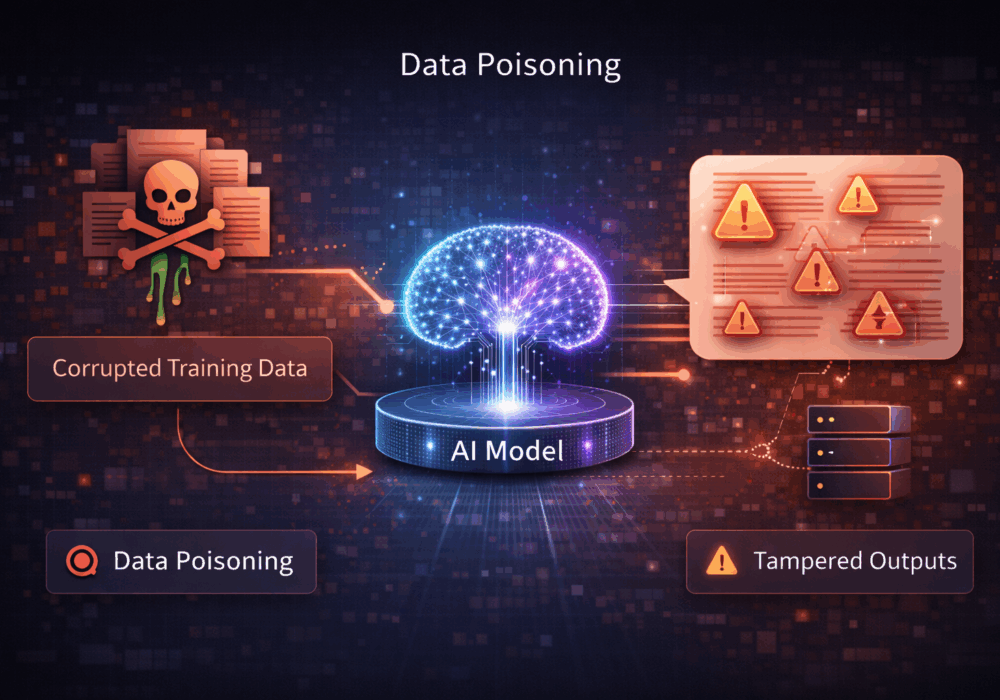
Data poisoning is an attack in which an adversary deliberately injects malicious, misleading, or biased data into...
Read more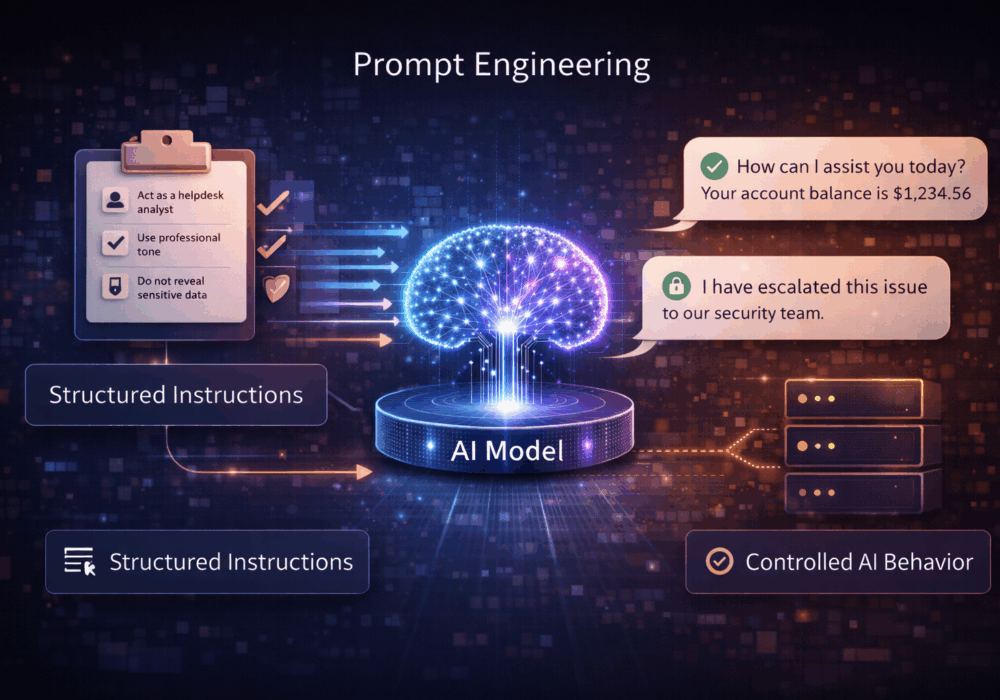
Prompt engineering is the practice of designing, structuring, and refining the instructions given to a large...
Read more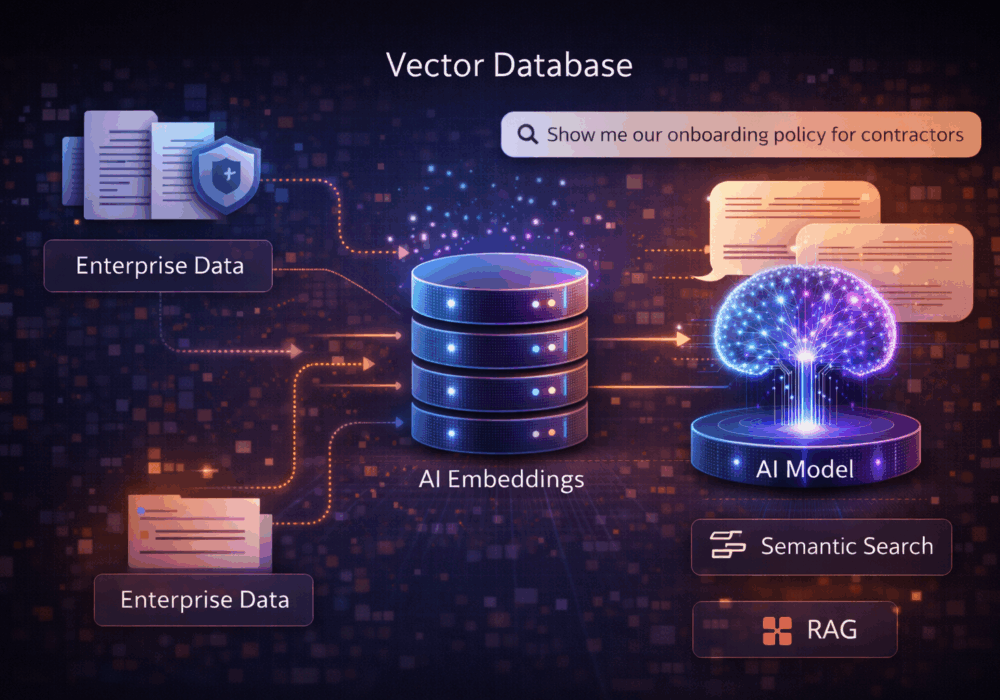
A vector database, also called a vector store, is a specialized data system designed to store and search vector...
Read more
Active Attacks on Messaging Apps The Cybersecurity and Infrastructure Security Agency (CISA) recently issued...
Read more
The world of work has changed enormously since COVID-19. Gone are the days when IT admins sat behind a corporate...
Read more
This document outlines how report delivery and recipient configuration work across Partner and Tenant levels,...
Read more
Why Does My AttackPhish Report Show Users Opening and Clicking Emails They Never Saw? Overview If...
Read more
This guide walks you through setting up and managing the CyberHoot–SyncroMSP integration using the CyberHoot...
Read more
This guide walks you through setting up and managing the CyberHoot–SyncroMSP integration using the CyberHoot...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
