July 15, 2020: Cybersecurity researchers today disclosed a new highly critical “wormable” vulnerability, carrying a severity score of 10 out of 10 on the CVSS scale – affecting Windows Server versions 2003 to 2019. This critical vulnerability allows an unauthenticated, remote attacker to gain domain administrator privileges over targeted servers and seize complete control of an organization’s IT infrastructure. This is accomplished by attacking a commonly open port on internal networks used to access websites called Domain Name Services (DNS), which is something like the old telephone book that listed a phone number for a person’s name. DNS converts website names to IP Addresses. This is what has the zero-day flaw that was reported today by security researchers. It is so significant that its been given a name: SigRed. Vulnerabilities that gain special names are usually bad! Think CodeRed, SQL Slammer, HeartBleed to name some recent bad ones!
A hacker exploits this vulnerability by sending a specially-crafted malicious DNS query to a Windows DNS server that leads to arbitrary code execution. Since DNS Server runs with elevated privileges [SYSTEM], a hackers can take complete and unrestricted control of the entire windows based server infrastructure. That is really, really, bad. Furthermore, security researchers reporting on this state it is “wormable” which means self-replicating, not unlike COVID-19 but worse, spreading at the speed of packets on a network to all other servers running DNS services. Read more about Worms in CyberHoot’s Cybrary articles such as SQL Slammer or the Morris Worm (1st Internet Worm ever).
Impacted Systems: Windows Server versions 2003 to 2019
What Should You Do?
- Given the severity of the vulnerability and the high chances of active exploitation, it’s recommended that users patch their affected Windows DNS Servers as soon as possible.
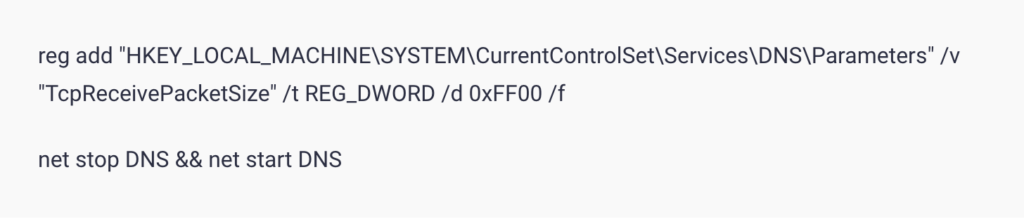
- A temporary but effective workaround if you can’t patch immediately is to make a registry change as outlined in this Microsoft’s knowledge base article and also shown below.
- Pay attention to vulnerabilities that are disclosed in the COTS software you purchase and use at your business. Sometimes they will have vulnerabilities that can lead to compromise of your computing systems. Always monitor your vendors security advisories and apply patches in a timely fashion to ensure your software environment is safe and secure from these and many other vulnerabilities.
Sources:
Microsoft Patching and Work-Around Knowledge Base Article
17-Year-Old Critical ‘Wormable’ RCE Vulnerability Impacts Windows DNS Servers

