"CyberHoot is a great option for Cybersecurity for our schools. The videos and other training are very user-friendly. Their support is fantastic as well."

Non-Public Personal Information (NPPI) is personal and private information that's provided by a...
Read more
Anti-Censorship are methods to combat censorship – for example, preventing search results from being...
Read more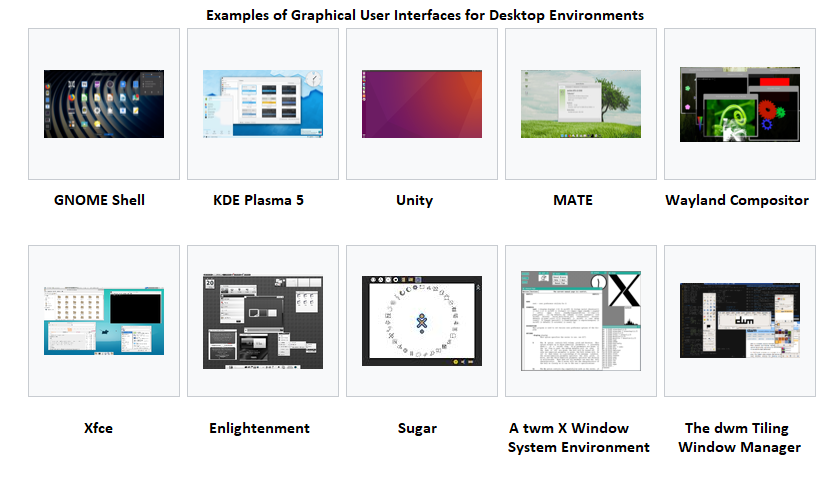
A Graphical User Interface (GUI), often pronounced 'gooey', is a user interface that includes...
Read more
A Solid State Drive (SSD) is a type of storage device that supports reading and writing data and stores...
Read more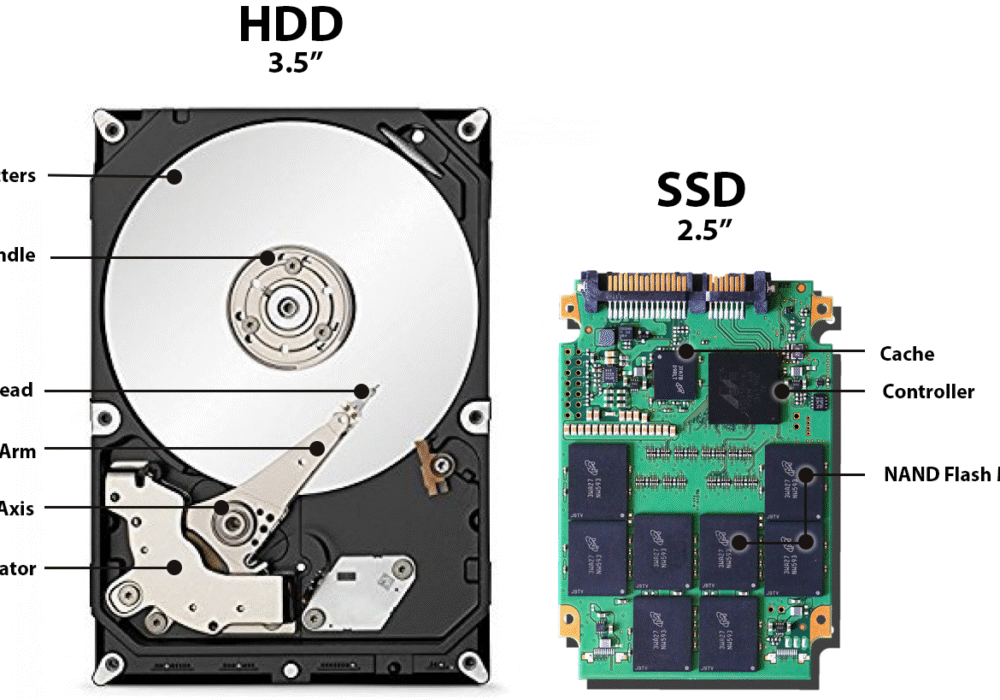
A Hard Disk Drive (HDD), also known as a hard drive, is a computer storage device holding magnetic...
Read more
A Polymorphic Virus is a type of 'shape-shifting' virus, producing malicious code that is able to...
Read moreApple Wireless Direct Link (AWDL) is a low latency/high-speed Wi-Fi peer-to peer-connection Apple uses...
Read more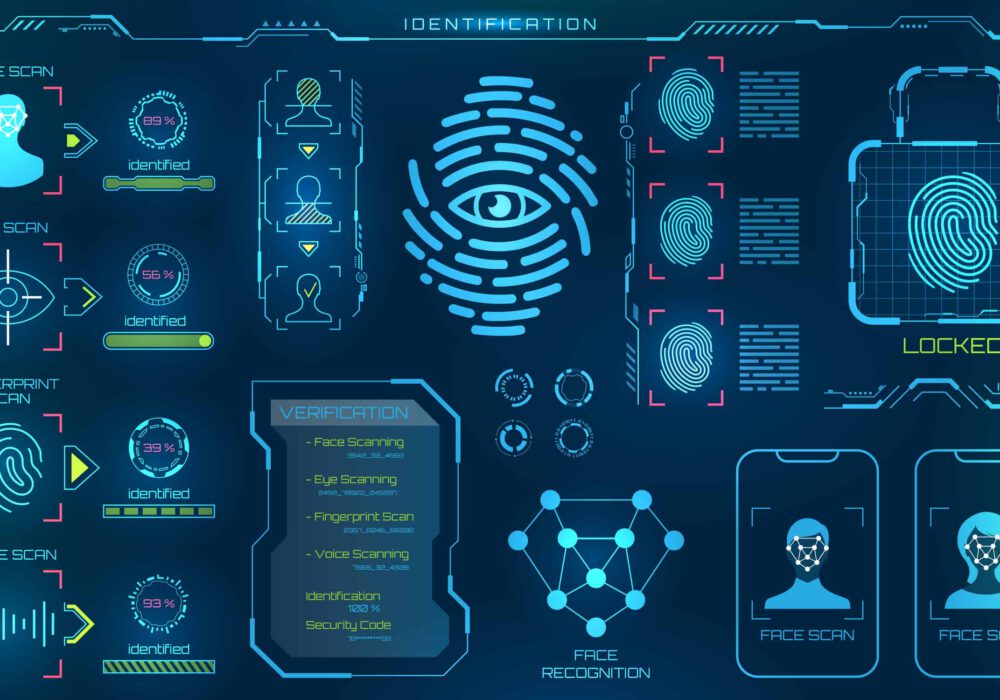
Biometrics identification refers to computer-based data that identifies a person based on unique...
Read more
A Parasitic Virus, also known as a file virus, is spread by attaching itself to executable programs....
Read more
A Boot Sector Virus is a virus that infects the 'boot sector' of floppy disks or the 'Master Boot...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
