"While it is well known that there are many cyber security threats, sorting out how to protect yourself without accidentally exposing yourself can be a daunting task. For a small organization like ours, this type expertise and time to research..."

The IETF (Internet Engineering Task Force) is the organization that defines standard Internet operating...
Read more
Read-Only Memory (ROM) is storage technology that permanently stores data in a chip built into...
Read more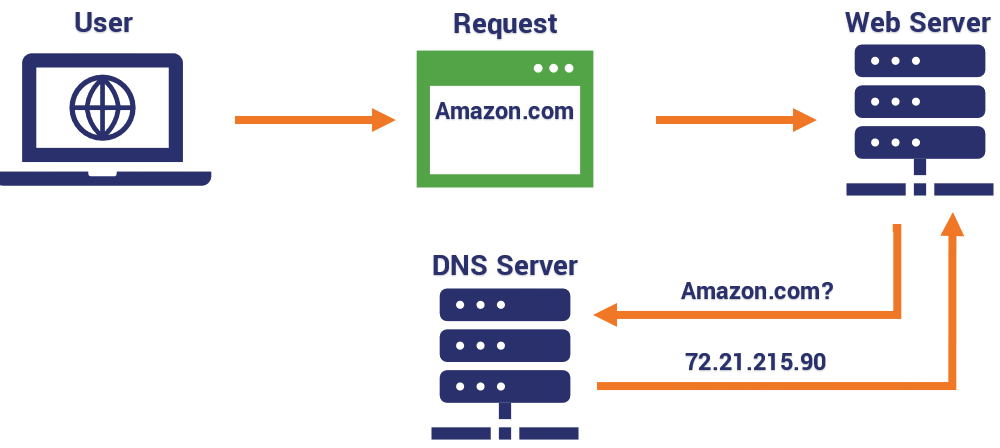
A Domain Name System (DNS) is essentially the 'phonebook' of the Internet. DNS is an elaborate,...
Read more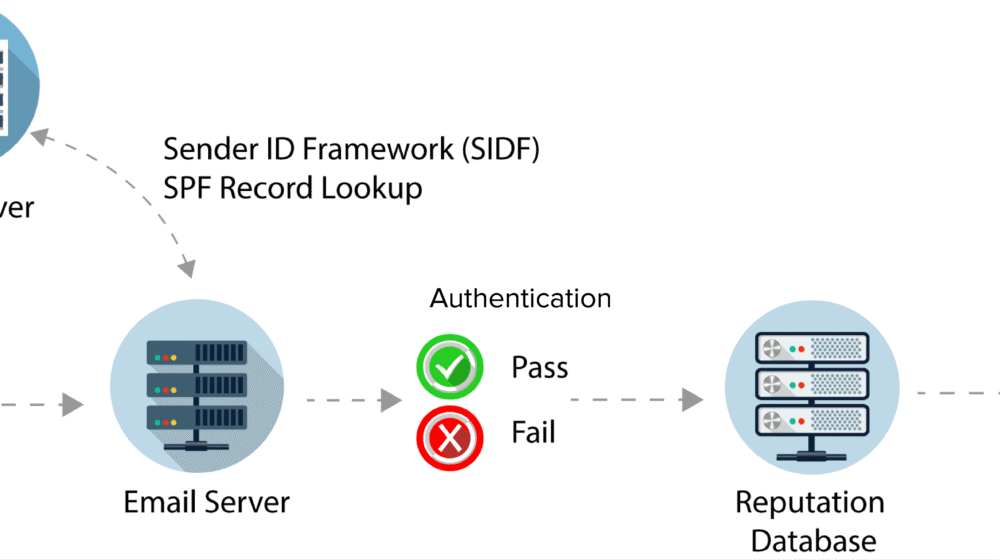
Sender Policy Framework (SPF) is an anti-spam tool where email domains of the senders can be...
Read more
Non-Public Personal Information (NPPI) is personal and private information that's provided by a...
Read more
Anti-Censorship are methods to combat censorship – for example, preventing search results from being...
Read more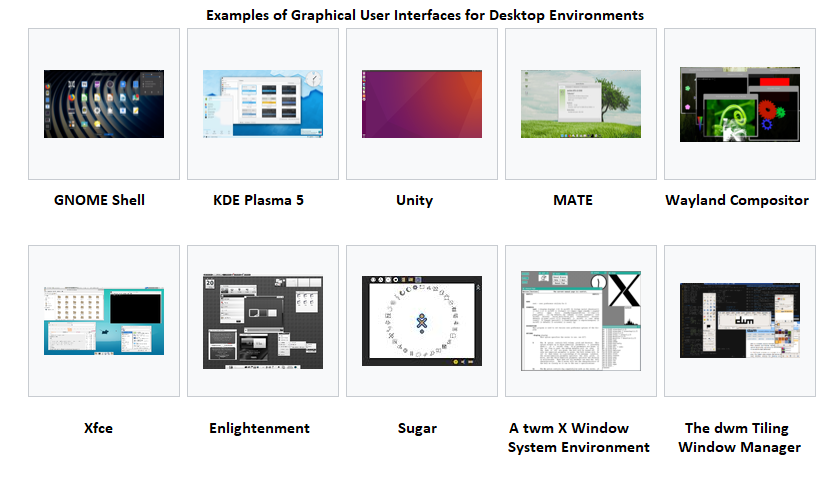
A Graphical User Interface (GUI), often pronounced 'gooey', is a user interface that includes...
Read more
A Solid State Drive (SSD) is a type of storage device that supports reading and writing data and stores...
Read more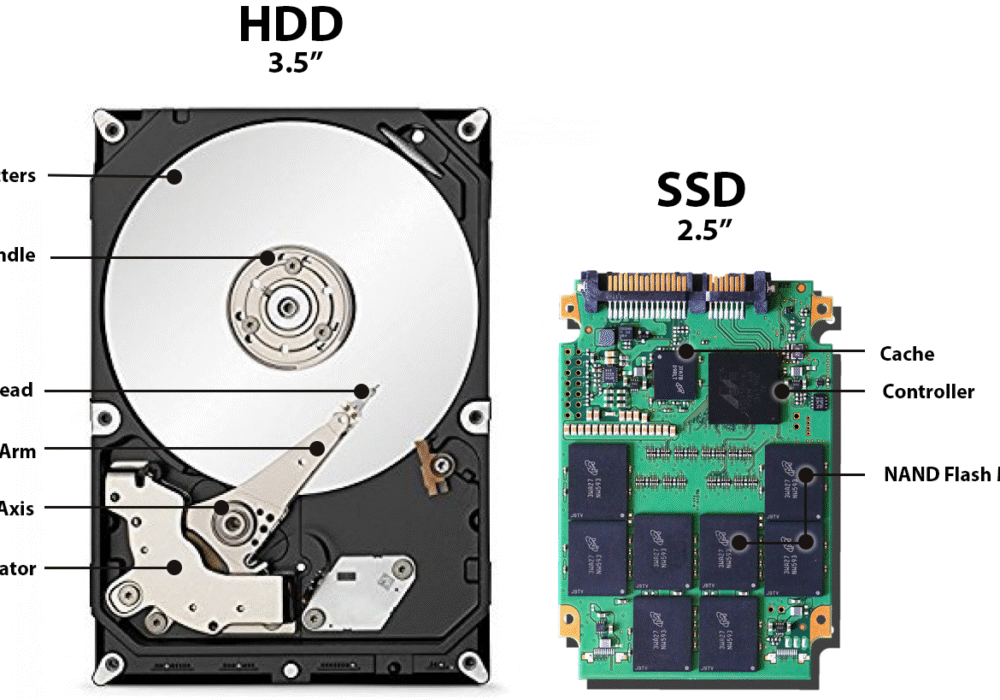
A Hard Disk Drive (HDD), also known as a hard drive, is a computer storage device holding magnetic...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
