"Craig and the CyberHoot team are great business partners! They are always open to enhancing their product, and ready to help my team with any deployment questions they may have. I am also an end user of the CyberHoot security..."
Access Control Access control is a security technique that regulates who or what can view or use...
Read more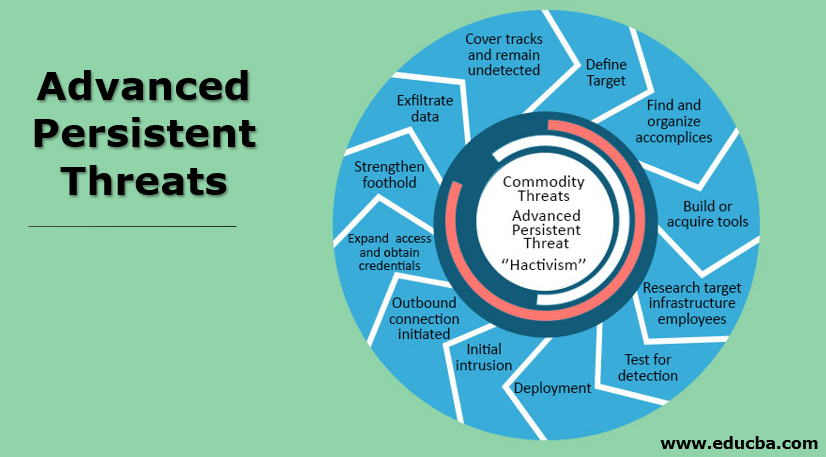
An Advanced Persistent Threat (APT) is an adversary that possesses sophisticated levels of expertise and...
Read more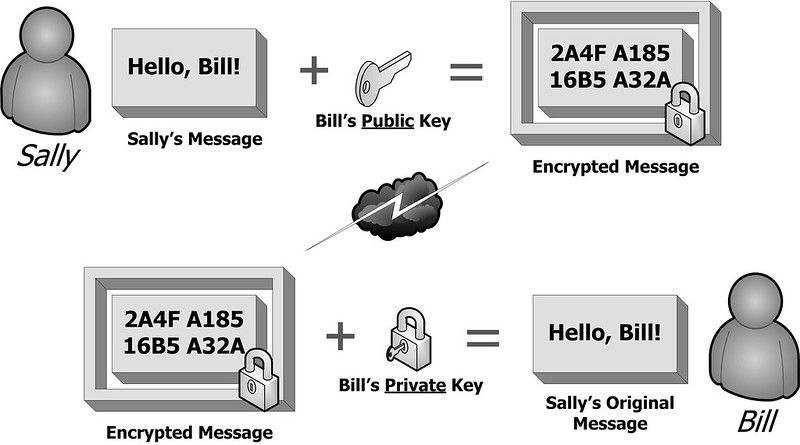
Image Source Public Key Cryptography is technically known as asymmetric encryption, is a...
Read more
Image Source An Adversary is an individual, group, organization, or government that conducts or has...
Read more
Image Source Antivirus Software is a program that monitors a computer or network to detect or...
Read more
Compromised Credentials occurs when an unsuspecting user's login username and password are in the possession...
Read more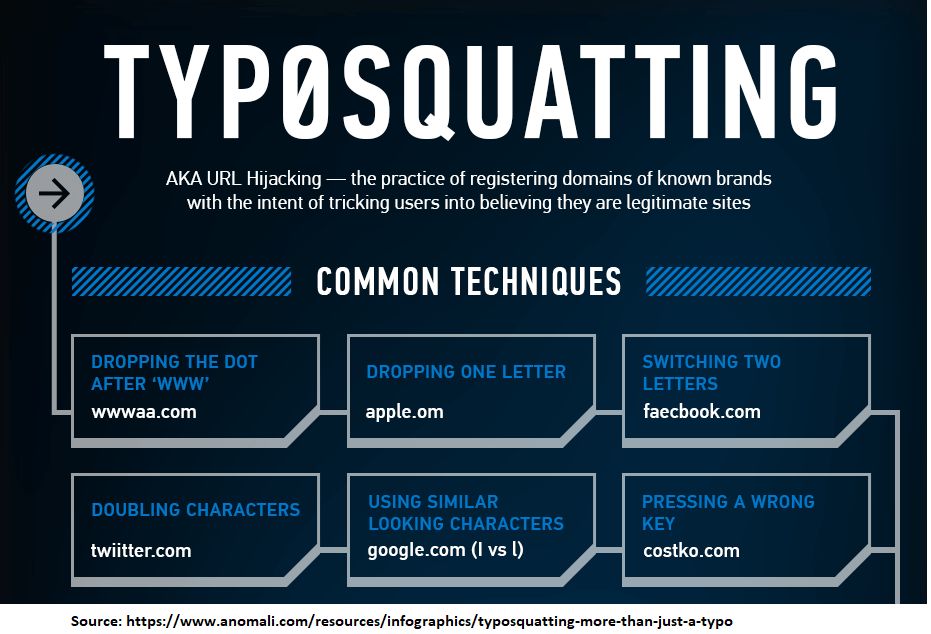
Typosquatting is also called URL hijacking. It is a form of cybersquatting which relies on mistakes such as...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
