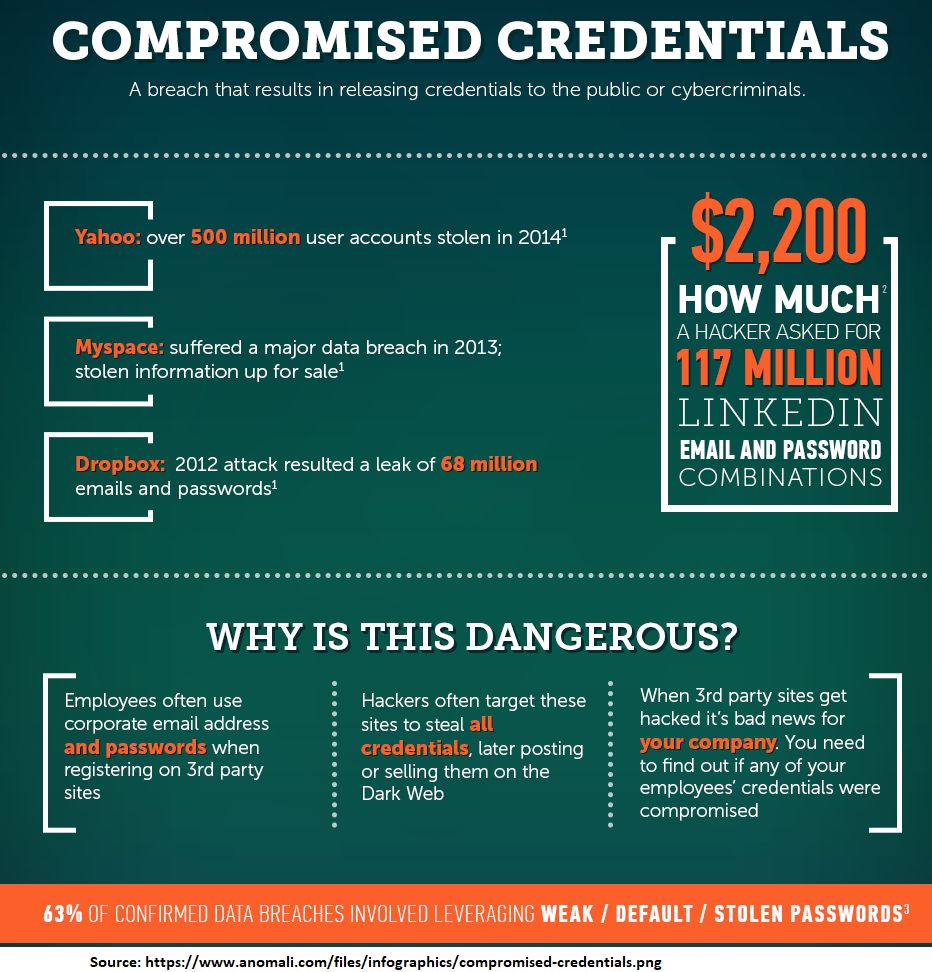
Compromised Credentials occurs when an unsuspecting user’s login username and password are in the possession of a hacker. Those credentials have been compromised. How they are compromised can occur in many different ways. Two of the most common are breached online websites as shown in the graphic above (Yahoo, Myspace, and DropBox being examples of large-scale breaches).
Another way is the result of a successful phishing campaign in which employees attempt to open a document or file sent by a colleague or business partner and it immediately requests your Google or Microsoft credentials. What is really happening is you are at a Hacker Website which will steal your Email Account credentials if you enter them.
The results can be devastating. Hackers know that once they get into one employees email account, they can send another phishing attack to steal other people’s credentials to ALL the EMAIL addresses in that compromised email account. This is what makes these attacks so devastating, quick, and effective. For more information on a real-world event, read the Blog article titled: Domino Attack.
Discover and share the latest cybersecurity trends, tips and best practices – alongside new threats to watch out for.

Spoiler alert: If you’re still using “password123” or “iloveyou” for your login… it’s time for an...
Read more
Stop tricking employees. Start training them. Take Control of Your Security Awareness Training with a Platform...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
