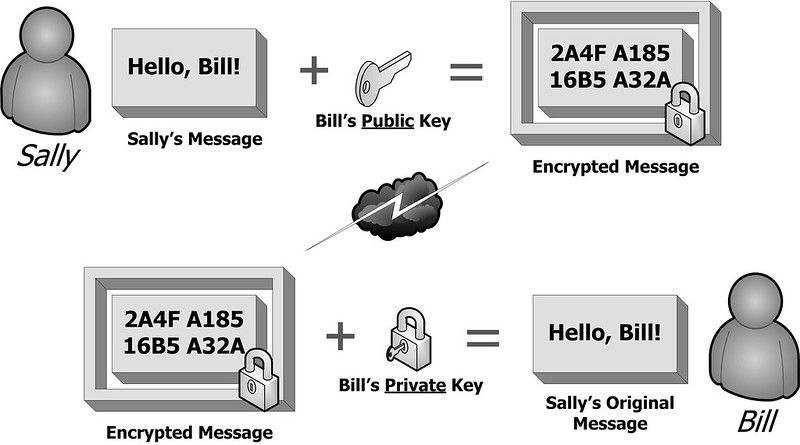
Public Key Cryptography is technically known as asymmetric encryption, is a cryptographic system that uses pairs of keys: public keys which may be disseminated widely, and private keys which are known only to the owner. The generation of such keys depends on cryptographic algorithms based on mathematical problems to produce one-way functions. Effective security only requires keeping the private key private; the public key can be openly distributed without compromising security.
In such a system, any person can encrypt a message using the receiver’s public key, but that encrypted message can only be decrypted with the receiver’s private key.
Synonyms: Encryption, Public Key Cryptography
Sources: CNSSI 4009, FIPS 140-2, InCommon Glossary
CyberHoot does have some other resources available for your use. Below are links to all of our resources, feel free to check them out whenever you like:
Note: If you’d like to subscribe to our newsletter, visit any link above (besides infographics) and enter your email address on the right-hand side of the page, and click ‘Send Me Newsletters’. Sign up for the monthly newsletter to help CyberHoot with their mission of making the world ‘More Aware and More Secure!’
Discover and share the latest cybersecurity trends, tips and best practices – alongside new threats to watch out for.

Spoiler alert: If you’re still using “password123” or “iloveyou” for your login… it’s time for an...
Read more
Stop tricking employees. Start training them. Take Control of Your Security Awareness Training with a Platform...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
