
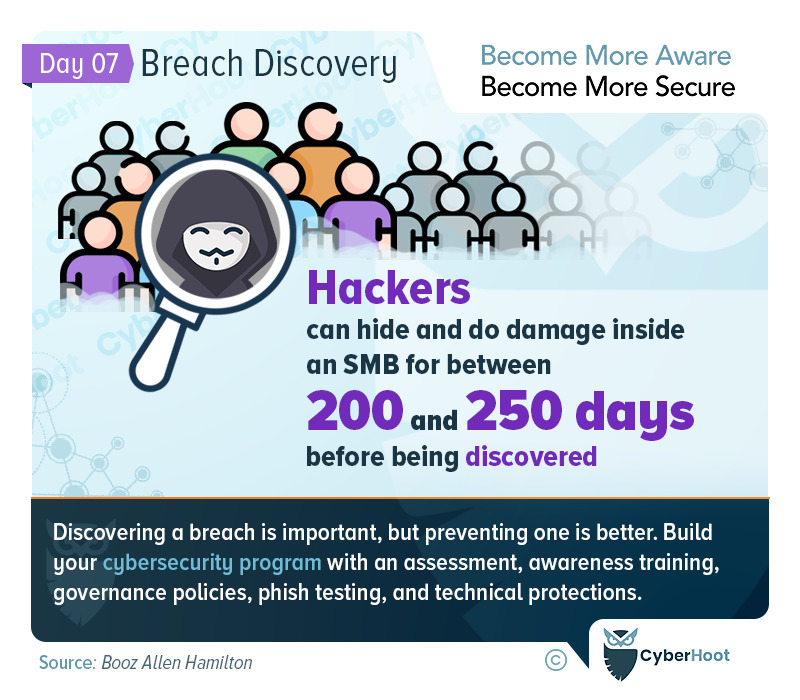
Breach Discovery is Often Quite Hard for Businesses
Breaches can be exceedingly difficult for businesses to discover. The average time hackers spend in our networks after a compromise is between 200 and 250 days. Imaging that! This is well more almost 2/3s of a year.
For highly targeted companies such as those in the Defense Industry fighting off nation state attackers, or healthcare companies where the data is extremely valuable, there are additional sometimes costly protective measures to be followed:
- Consider deploying a Security Event and Incident Management (SEiM) solution to collect all the logs from various security devices across your network (think Firewall, Network and Host Intrusion Prevention Systems, and Server logs) to analyze your normal network traffic and alert when things are off baseline.
- Always use Multi-Factor Authentication for every remote access connection into your network no matter what. Be careful which method of MFA you use… some are more susceptible than others to exploits (SMS being less trustworthy than other methods).
- Consider implementing network segmentation at a minimum or an Air Gap at the maximum to protect your most critical data from internet hackers.
For everyone, including the companies mentioned above, CyberHoot recommends the following protective measures:
CyberHoot Best practices:
- Train your employees on the common attacks that are out there. From weak passwords and password managers, to the importance of multi-factor authentication and how to spot phishing attacks. Awareness is the key to defending your business.
- Govern you employees with cybersecurity policies including Acceptable Use, Password, Information Handling and a Written Information Security Policy.
- Establish cybersecurity best practice processes such as a Vulnerability Alert Management Process (VAMP) and a Cybersecurity Incident Management Process (CIMP) to guide and require action in the face of an emergency. Then move on onboarding and offboarding processes, SaaS management processes, and 3rd party risk management.
- Establish strong technical protections including: a Firewall, antivirus, anti-malware, anti-spam, multi-factor authentication on all critical accounts, Enable full disk encryption, manage the keys carefully, and most importantly, adopt, train on and require all employees to use a Password Manager.
- Test employees on how to spot and avoid phishing attacks. CyberHoot has released a disruptive method of Phish Testing the fills in gaps in your employees knowledge without punishing them for failure. Instead we reward them for success. More info is available here.
- Backup your data by following our 3-2-1 Backup methodology to ensure you can recover your business from a cybersecurity event.
- In the modern Work-from-Home era, make sure you’re managing personal devices connecting to your network by validating their security (patching, antivirus, DNS protections) or prohibiting their use entirely.
- If you haven’t had a risk assessment by a 3rd party in the last 2 years, you should have one now. Establishing a risk management framework in your organization is critical to addressing your most egregious risks with your finite time and money.
- Buy Cyber-Insurance to protect you in a catastrophic failure situation. Cyber-Insurance is no different than Car, Fire, Flood, or Life insurance. It’s there when you need it most.
CyberHoot believes that for many small to medium sized businesses and MSPs, you can greatly improve your defenses and chances of not becoming another victim of cyberattack if you follow the advice above.
We hope you’re enjoying Cybersecurity Awareness Month (CAM). Visit or subscribe to CyberHoot’s Facebook, LinkedIn, or Twitter pages to get daily updates throughout the month.
Sources:
Booz Allen Hamilton – Dwell Time inside your Network
Secure your business with CyberHoot Today!!!
Sign Up Now


