A Vulnerability Alert Management Policy (VAMP) is created within an organization to establish consistent rules for the review, evaluation, application, and verification of system updates to alleviate vulnerabilities in one’s environment and the risks associated with them. This process sets out goals and timing around applying patches to address critical vulnerabilities within your environment. Applicable vulnerability alerts, discovered via threat hunting, vulnerability alert services, and security assessments, require an appropriate, timely, repeatable, and documented response in order to prevent damage to a company’s systems, goodwill, and ultimately their reputation.
A Business’s vCISO and MSP typically provide oversight on vulnerabilities and critical issues through many online sources including cybersecurity email lists, forums like CISA and Microsoft, and even government agency alerts (FBI, NSTAC, and NSA) are reviewed as needed.
Security alerts must be reviewed and assigned to a 3-point criticality scale, defined below and based upon established classifications within the cybersecurity industry. Your cybersecurity lead is responsible for escalating, reviewing, recommending a course of action, and then tracking the resolution and mitigation of each critical vulnerability alert.
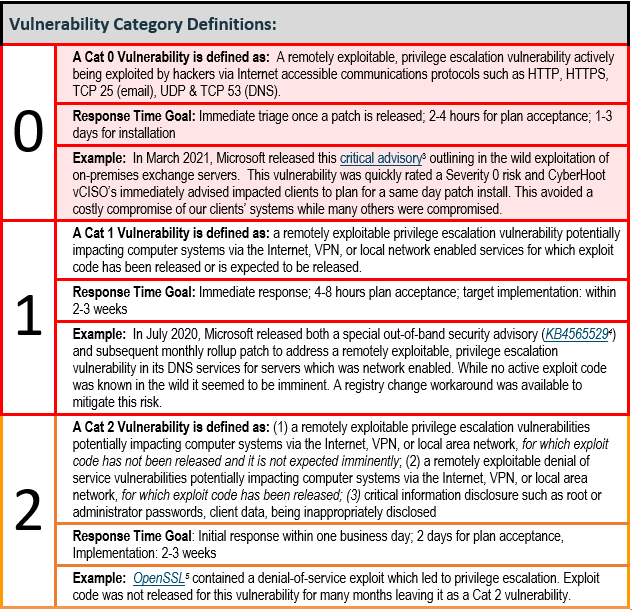
Every Small to Medium-sized Business (SMB) should have a policy in place guiding vulnerability alert management and mitigation. This policy outlines required timeframes for the review of critical alerts as well as the timeframe in which to implement a fix. A repeatable and consistent process for vulnerability alert management is the difference between a robust cybersecurity program and one that is likely to fail.
Additionally, CyberHoot recommends organizations adopt the four policies and one additional process (outlined below) to provide the greatest chance of success defending against hacking attacks within your business. Incidentally, CyberHoot has templates for all of these policies and processes:
There are other actions you should take to protect your business from other attacks and harm including:
Sources:
Additional Reading:
Vulnerability Alert Management Process (VAMP) – Day 15 of NCAM
Related Terms:
CyberHoot does have some other resources available for your use. Below are links to all of our resources, feel free to check them out whenever you like:
Note: If you’d like to subscribe to our newsletter, visit any link above (besides infographics) and enter your email address on the right-hand side of the page, and click ‘Send Me Newsletters’.
Discover and share the latest cybersecurity trends, tips and best practices – alongside new threats to watch out for.

Spoiler alert: If you’re still using “password123” or “iloveyou” for your login… it’s time for an...
Read more
Stop tricking employees. Start training them. Take Control of Your Security Awareness Training with a Platform...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
