Co-Authored by Craig Taylor
In an ever-changing cybersecurity world, data breaches continue to increase in frequency and impact. Cybersecurity threats come in various forms, including social engineering, credential theft, phishing attacks, and even web application attacks. If your organization experiences a cybersecurity incident, this article will help walk you through the steps you need to take to respond to this incident. CyberHoot assumes you have a Cybersecurity Incident Management Process (CIMP) in place to help guide you.
The tips and tricks in this article may identify gaps in your plan. Following CyberHoot’s guide below will help you work through the cybersecurity incident efficiently and effectively. If you don’t have a CIMP, you should engage CyberHoot’s vCISO program to help you create one.
In any incident, people are encouraged to move quickly to limit the damage caused by a breach. However, CyberHoot wants to caution folks on two higher-order priorities.
The first is protecting human lives. If the breached system is performing life-saving services, you may not be able to shut it down to address the breach. Human lives come first.
Second, if a forensic investigation is important to the system owners, you must handle the incident with evidence preservation at the forefront of your remediation efforts. This could mean taking an image of the hard drive using advanced forensic tools like Encase.
With the forensics question and human safety answered, you now can begin to move quickly toward incident identification and then containment. In order to contain an event, you need to know what happened. To answer that, you need to assemble your response team.
Hopefully, before an incident occurs, your Cybersecurity Incident Management Process (CIMP) identified the members of your response team and notified them of the assembly requirements day or night. Get them together now so you can ascertain what happened. This team will always include information security, information technology, operations, and senior management.
This article assumes you have confirmed an incident is in progress but that you may not know what happened. Many times, things go bump in the night, but they have a simple explanation that is anything but a security incident. Disk drives do fill up, causing servers to crash, that is not an incident. It just happened to occur at 3 am, sending your SOC into a panic.
A word of caution: in an incident, speculation and unsupported conjecture run rampant. As an incident handler, you need to ask everyone to take a deep breath and review the facts. If you’re missing key information, get it. The first goal in incident containment is figuring out what happened. To do that, you need your team assembled to help piece things together.
Did a scheduled change go poorly? Is a system missing critical patches? Do you have a malicious insider? What are the indicators of compromise you do see? Answers to these questions will guide your incident response in containing the event.
The team is confident that a missing patch on your WordPress site was exploited and led to a compromise of your web server. Recent security notices confirm exploit code is in the wild and hackers are breaching WordPress websites. Evidence of a breach has been found on your WordPress Webserver. The incident source has been confirmed. Now what?
If appropriate, call your local police department and report your situation and the potential risk for identity theft, wire fraud, or whatever the incident involves. The sooner law enforcement learns about the event, the more effective they can be. If your local police aren’t familiar with investigating information compromises, contact the local FBI office or the U.S. Secret Service. For incidents involving mail theft, contact the U.S. Postal Inspection Service.
To stop additional data loss, take all affected equipment offline but don’t turn any machines off if forensics is needed. Rebooting a machine can wipe valuable information from memory and disks. Just remove them from the network removing remote hacker access and stopping any data transfers out of your organization.
Examine your all network entry and exit points (typically firewalls) for evidence of remote access. Do you see connections from foreign countries? Was data transferred out of the organization? Are there encrypted files that indicate a ransomware event?
If you have a suite of tools available to you that might identify the presence of malware or remote access trojans etc., you should run it against your impacted machines. In this example, no additional malware is found inside your environment. All damage was to the website hosted externally. No data loss was experienced.
If the website was compromised, it will need to be rebuilt due to the presence of a rootkit installed by the hackers. That is our next step, eradicating the hacker’s backdoors and malware from your environment.
TIPS: Since most incidents happen after hours, tomorrow may also need to engage forensics, legal, human resources, communications/public relations to manage the incident.
Forensics: If forensics will be important, you need to call them in early in your incident response to help avoid damaging evidence in your investigation. Consider hiring an independent forensic investigator to help you determine the source and scope of the breach. They will capture forensic images of affected systems, collect and analyze evidence, and outline remediation steps. But be warned, they charge $400-$500 an hour.
Legal Counsel: Consult with your legal counsel on the incident in question. This provides some protection to incident handlers based upon attorney-client privilege from having to disclose everything known about an incident under investigation. They can also advise you on federal and state laws that may become applicable from the breach.
Breach Notification: In the best-case scenario, you can contain and eradicate a breach in 24 to 48 hours. However, you may have contractual obligations to notify clients within 24 hours of a confirmed breach. Have someone check on this and execute the appropriate communications plan with or without involving Public relationship firms.
If possible, put ‘clean’ machines online in place of affected ones. In addition, update the credentials and passwords of authorized users. If a hacker breached your system for any period of time before taking the website down with their rootkit in place, you must assume all credentials with access to the website and your WordPress site are compromised and your system will remain vulnerable until you change those credentials, even if you’ve removed the hacker’s tools.
If a Managed Service Providers (MSP) is supporting your IT infrastructure, review what personal information they can access and decide if you need to change their access privileges.
In this instance, we suspect the missing patches on the WordPress site were the root cause. So the very next step after containment is to patch the system and bring it back online. Pay particular attention to how you patch. Placing the system online outside your firewall invites calamity all over. Patch from a safe location before making the system available to the Internet at large.
If your service providers say they have remedied vulnerabilities, verify that they really fixed things by direct inspection. Now would be a good time to review the patching status of all your systems (internally and externally) to ensure they are all up-to-current levels. Also check your antivirus software to make sure all systems there are up-to-date, installed universally, and functioning properly with reporting working.
If machines have been compromised with rootkits or advanced malware, there is often no antivirus that is capable of cleansing the machine to a known good state. In these cases, you should wipe the machine clean and rebuild it from scratch before putting back into production.
Following the patching and validation checks in Eradication, you can now move on to recovery. That means placing your now fully-patched WordPress Website back into production and monitoring it closely. There is always the possibility that your root cause was wrong, and the hackers could return.
Next, turn your attention to learning the extent of the breach.
Find out if measures like encryption were enabled when the breach occurred. Analyze backup or preserved data. Review logs to determine who had access to the data at the time of the breach. Examine firewall rules and logs to find out if data was exfiltrated to the Internet. Note: this may not be possible if ANY port is open to ANY destination outbound in your firewall. Consider a Security Incident Event Monitoring solution in the next phase (#5).
When your business experiences a data breach, you should notify law enforcement, other affected businesses, and affected individuals. When doing this, the first thing you should do is to determine your legal requirements. All states, the District of Columbia, Puerto Rico, and the Virgin Islands have enacted legislation requiring notification of security breaches involving personal information. In addition, depending on the types of information involved in the breach, there may be other laws or regulations that apply to your situation. Check specific state and federal laws or regulations for any specific requirements for your business.
If the breach involved more than 500 electronic personal health records, then you’re obligated under the Health Breach Notification Rule to notify the Department of Health and Human Services (DHHS). You may also have to notify the FTC and, in some cases, the media. Before you engage with the media on a major news-worthy breach, you will want to consult a public relations firm.
Depending upon what data was exposed or stolen, you may have obligations to notify your clients. Some MSA’s require breach notification in a specific time frame, so the clock may be ticking on your legal obligation to notify certain parties. If HIPAA data was breached or Non-Public Personal Information, there are legislative reporting requirements here. Consult your privacy expert, HIPAA expert, legal, and contract teams to ensure you deal with the compliance and contractual obligations at this point.
Follow your communications and notification plan ensuring you reach all affected parties (clients, employees, investors, business partners, and other stakeholders). Make factual statements about the breach and don’t withhold key details that might help consumers protect themselves. It’s important to note that you shouldn’t publicly share information that might put consumers at further risk.
One final point on breach notification is that law enforcement may prohibit you from notifying affected parties due to their “active investigation”. All contracts have a notification delay for this situation.
Once systems are back online, and your recovery is mostly complete, you can turn your attention to learning from the event. Consider hosting a ‘lesson learned’ or “Root Cause Analysis“. This is where you capitalize on the incident to improve your defenses, your alerting, and your business processes.
When you set up your network, you may have segmented it so that a breach on one server or in one site could not lead to a breach on another server or site. Work with your Information Technology team (MSP) to analyze whether your segmentation plan was effective in containing the breach. If you need to make any changes, do so now.
If the data breach involved personal information improperly posted on your website, immediately remove it. Be aware that internet search engines store, or “cache,” information for a period of time. You can contact the search engines to ensure that they don’t archive personal information posted in error.
You can also search for your company’s exposed data to make sure that no other websites have saved a copy. If you find any, contact those sites and ask them to remove it.
If account information like credit card or bank account numbers, or Social Security numbers have been stolen, businesses should contact the major credit bureaus for additional information, advice, and protection. Businesses may be forced to pay for fraud /credit monitoring on the impacted individuals. You may even have insurance coverage to pay for this monitoring.
The best protection for individuals involved in a breach of financial records is for them to freeze their credit at the following credit bureaus:
Transunion Credit Freeze
Equifax Credit Freeze
Experian Freeze Center
Innovis Security Freeze
ChexSystems Security Freeze
Certegy Security Freeze
Clarity Services Security Freeze
CoreLogic Teletrack Credit Freeze
CoreLogic Credco Credit Freeze
When notifying individuals it’s recommended you:
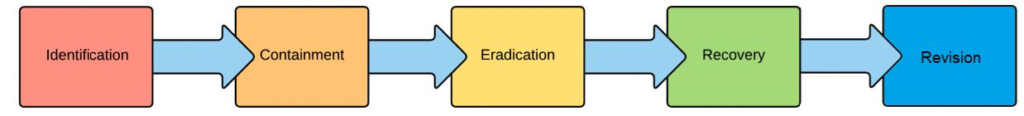
The best time to prepare for an incident is before it happens. Define your Cybersecurity Incident Handling Process (CIMP) before you need it. Then practice it before one actually happens. Having your team assembled to review the 5 steps of a security incident is critical to long-term success. Then you’ll be able to move smoothly through Identification, Containment, Eradication, Recovery, and Revision.
Don’t skimp on lessons learned either. You have valuable information that you can learn from at the ready following any incident. Following these measures and steps can ensure the long-term viability of your company.
Source:
Related Resources:
Discover and share the latest cybersecurity trends, tips and best practices – alongside new threats to watch out for.

Spoiler alert: If you’re still using “password123” or “iloveyou” for your login… it’s time for an...
Read more
Stop tricking employees. Start training them. Take Control of Your Security Awareness Training with a Platform...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
