"After 9 months of CyberHoot awareness training, a Financial Management firm with $4 Billion in assets was phish tested by the Fellsway Group. They had zero (0%) employees click on the phishing test. In contrast, the exact same phishing attack..."

File Transfer Protocol (FTP) is a communications protocol used for transferring or exchanging files...
Read more
High-Level Instructions: This HowTo video walks you through allow-listing CyberHoot’s Mail-Relay by either...
Read more
The Coronavirus has been on the front of everyone's mind lately, causing fear and concern across the...
Read more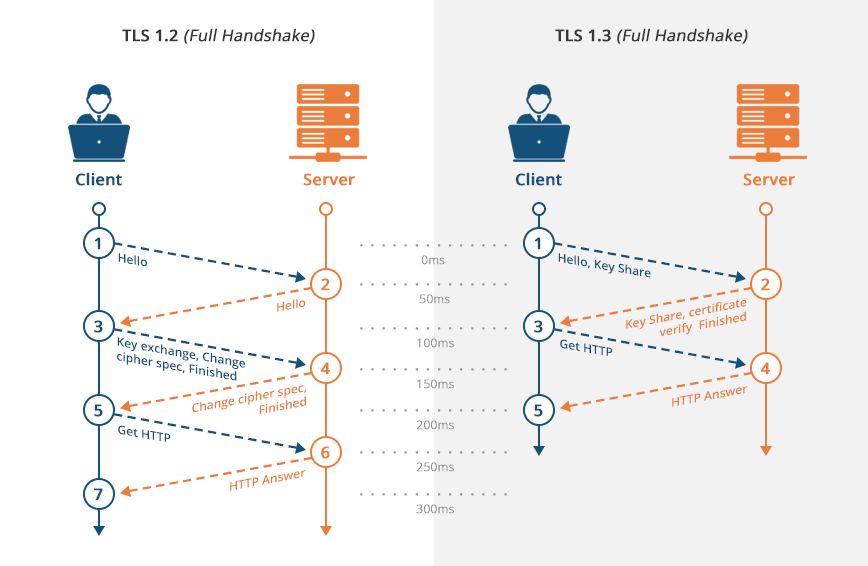
Transport Layer Security (TLS) is a security protocol made for privacy and data security for...
Read more
Dissemination of Information refers to the distributing of a company's or customer specific...
Read more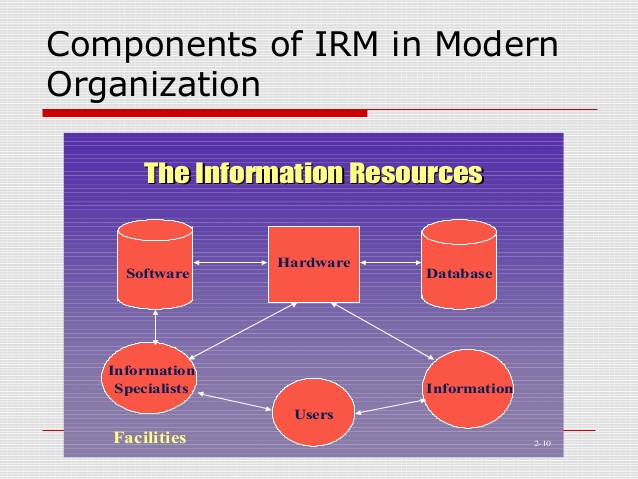
Information Resources Management (IRM) is the planning, budgeting, organizing, directing,...
Read more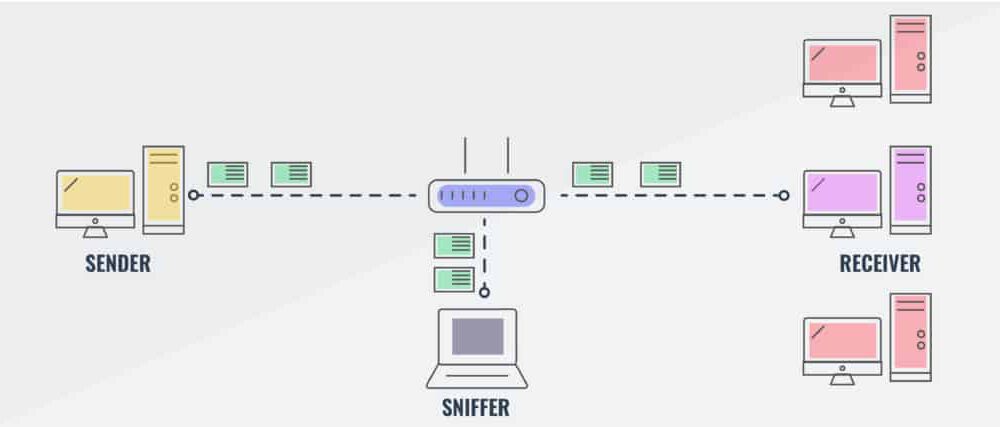
Packet Sniffing is the practice of gathering, collecting, and logging the packets that pass through a...
Read more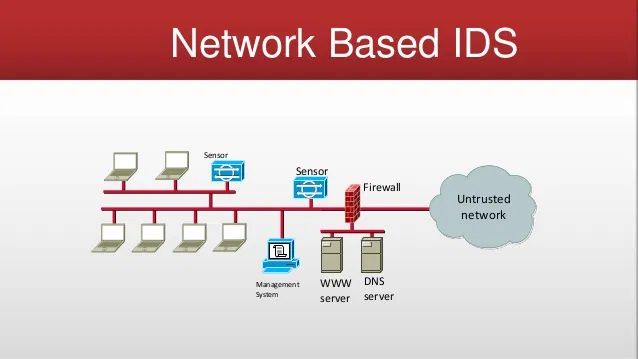
A Network Based Intrusion Detection System (NIDS), or Network Based IDS, is security hardware that is placed...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
