"Cybersecurity training is complicated, partnering with CyberHoot keeps it simple. Our users are engaged with little administrative overhead."

Fake IRS Tax Forms This week, AbnormalSecurity reported an attack on an estimated 15-50 thousand email...
Read more
Anti-Censorship are methods to combat censorship – for example, preventing search results from being...
Read more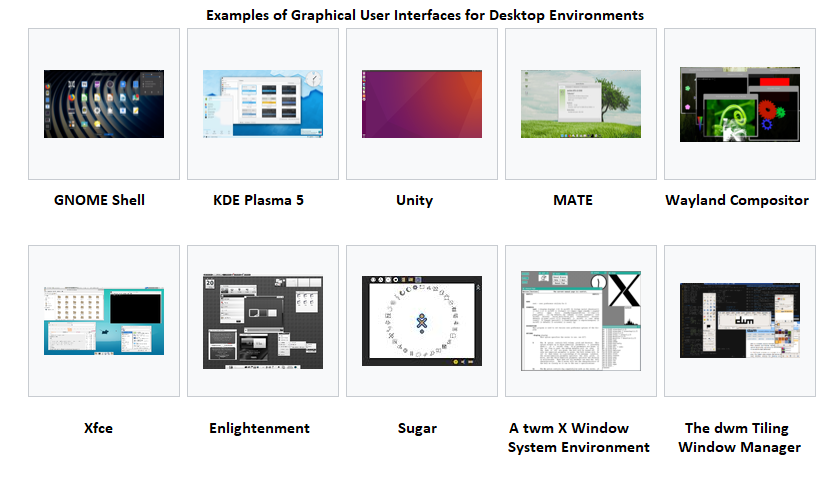
A Graphical User Interface (GUI), often pronounced 'gooey', is a user interface that includes...
Read more
A Solid State Drive (SSD) is a type of storage device that supports reading and writing data and stores...
Read more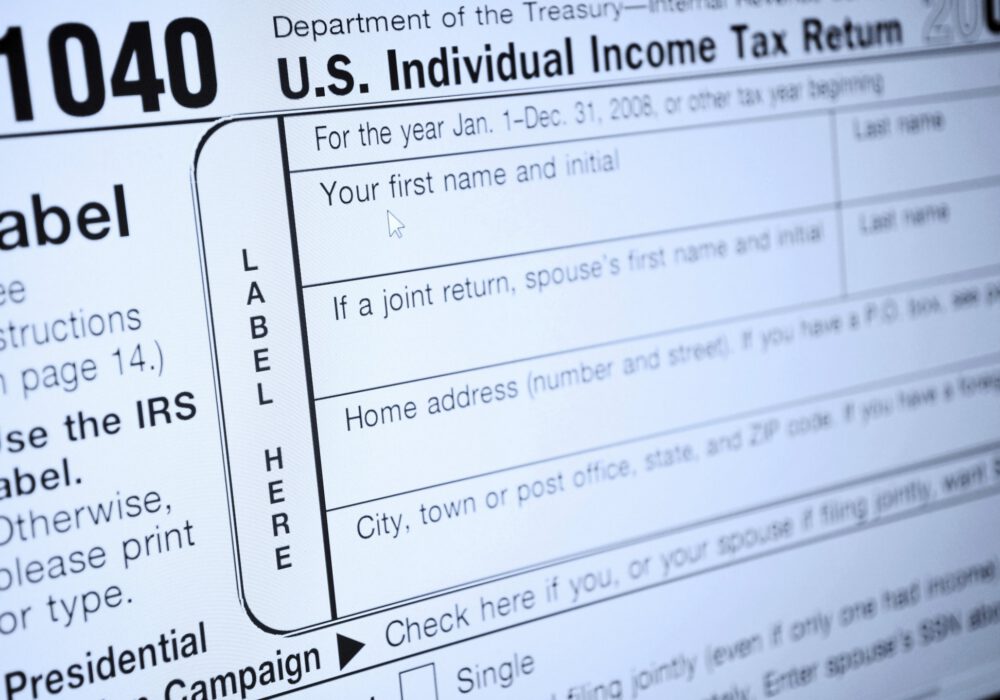
The Internal Revenue Service (IRS) announced this week that in January 2021 taxpayers can apply for an...
Read more
How can I adjust my payment/billing information? Sign in with your credentials (Administrators) Click on your...
Read more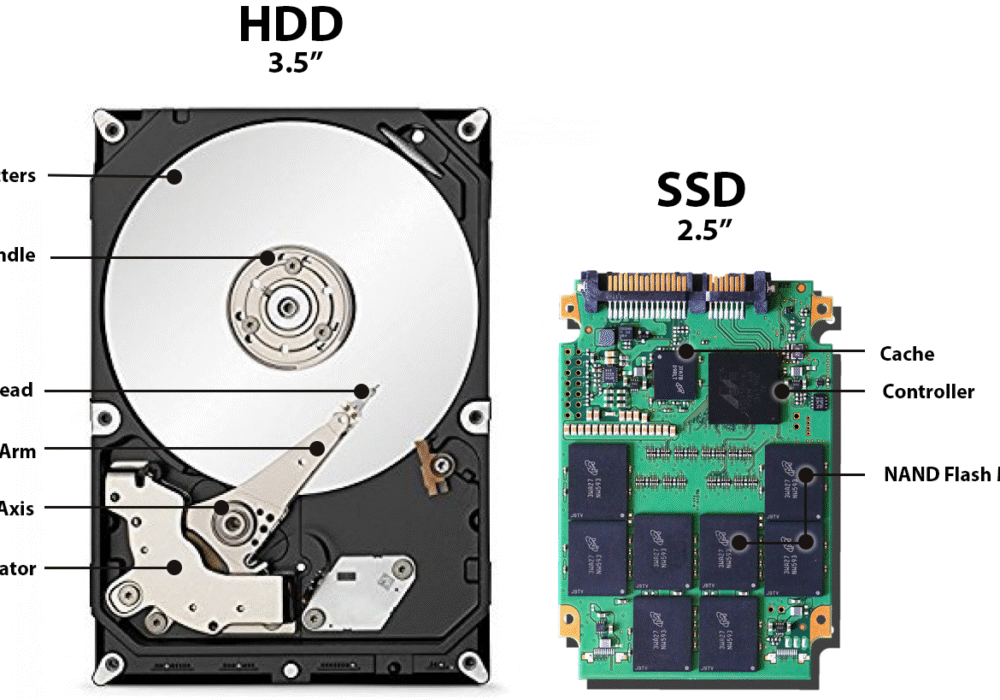
A Hard Disk Drive (HDD), also known as a hard drive, is a computer storage device holding magnetic...
Read more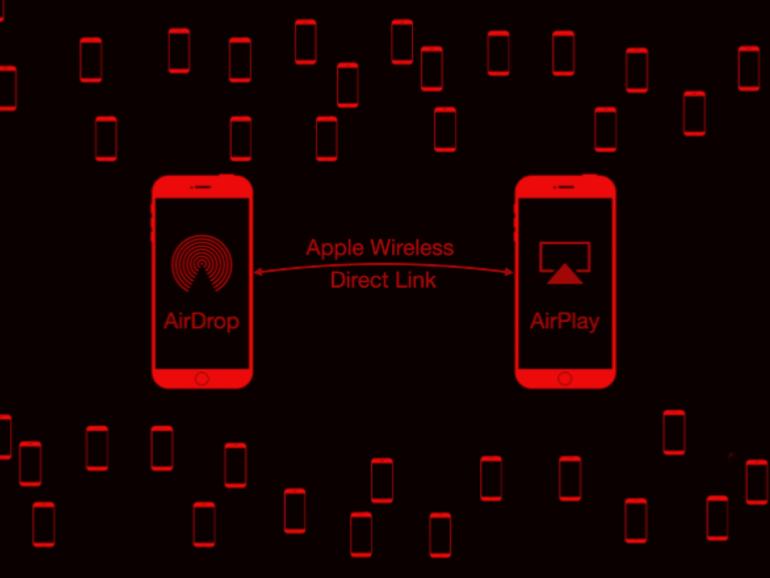
Google's Project Zero cybersecurity researcher (and white-hat hacker) Ian Beer published an article in...
Read more
A Polymorphic Virus is a type of 'shape-shifting' virus, producing malicious code that is able to...
Read moreApple Wireless Direct Link (AWDL) is a low latency/high-speed Wi-Fi peer-to peer-connection Apple uses...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
