"Cybersecurity training is complicated, partnering with CyberHoot keeps it simple. Our users are engaged with little administrative overhead."
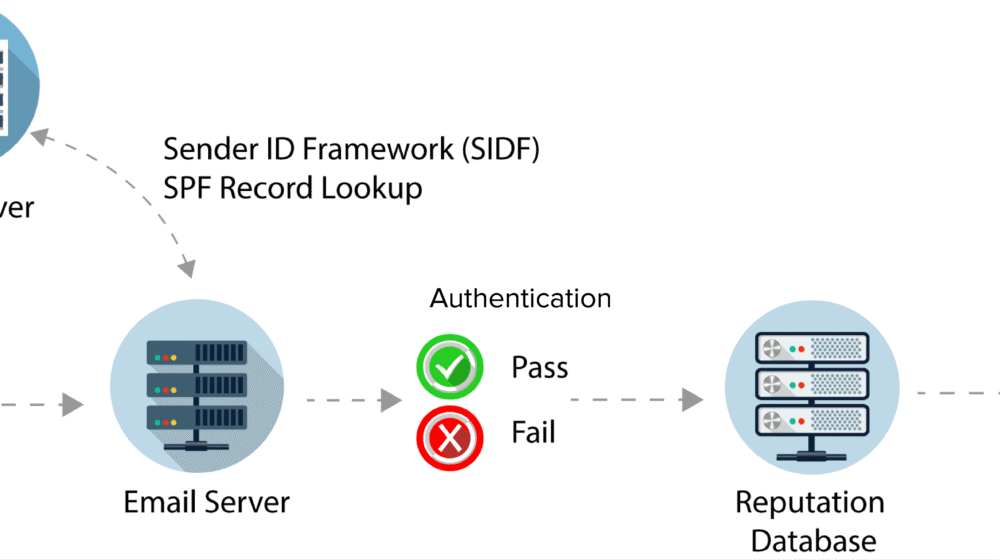
Sender Policy Framework (SPF) is an anti-spam tool where email domains of the senders can be...
Read more
Non-Public Personal Information (NPPI) is personal and private information that's provided by a...
Read more
Anti-Censorship are methods to combat censorship – for example, preventing search results from being...
Read more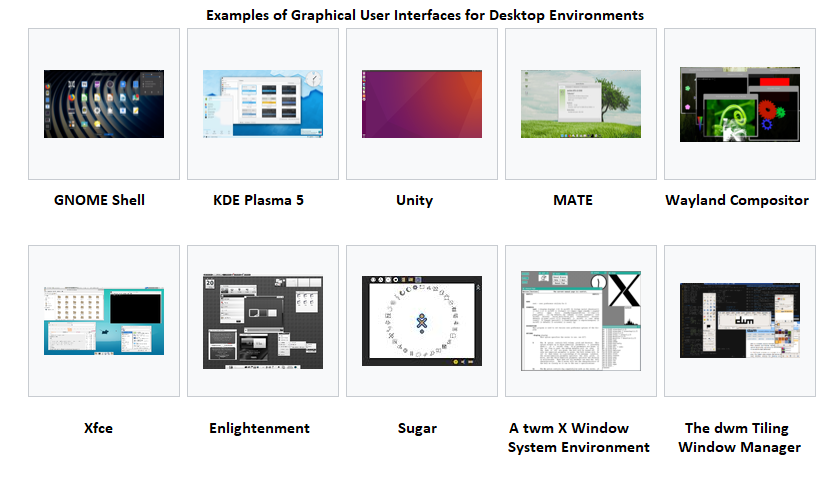
A Graphical User Interface (GUI), often pronounced 'gooey', is a user interface that includes...
Read more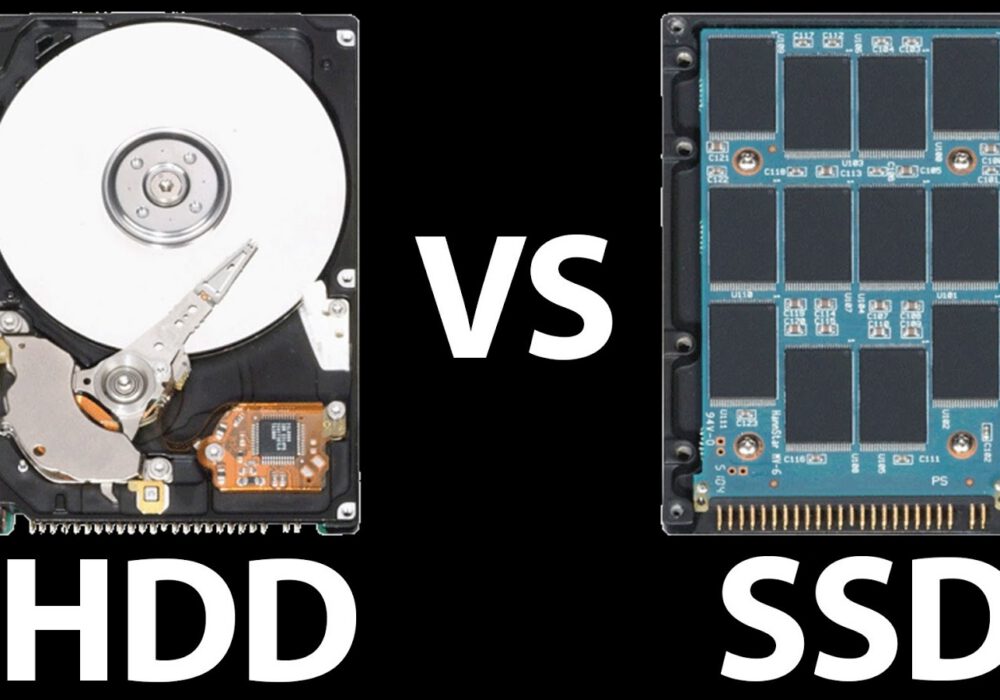
A Solid State Drive (SSD) is a type of storage device that supports reading and writing data and stores...
Read more
Cyberwarfare is the use of sophisticated cyber weapons (viruses, worms, trojans, etc.) by one...
Read more
If you run or bike, you probably heard about the Garmin Ransomware attack, taking down its...
Read more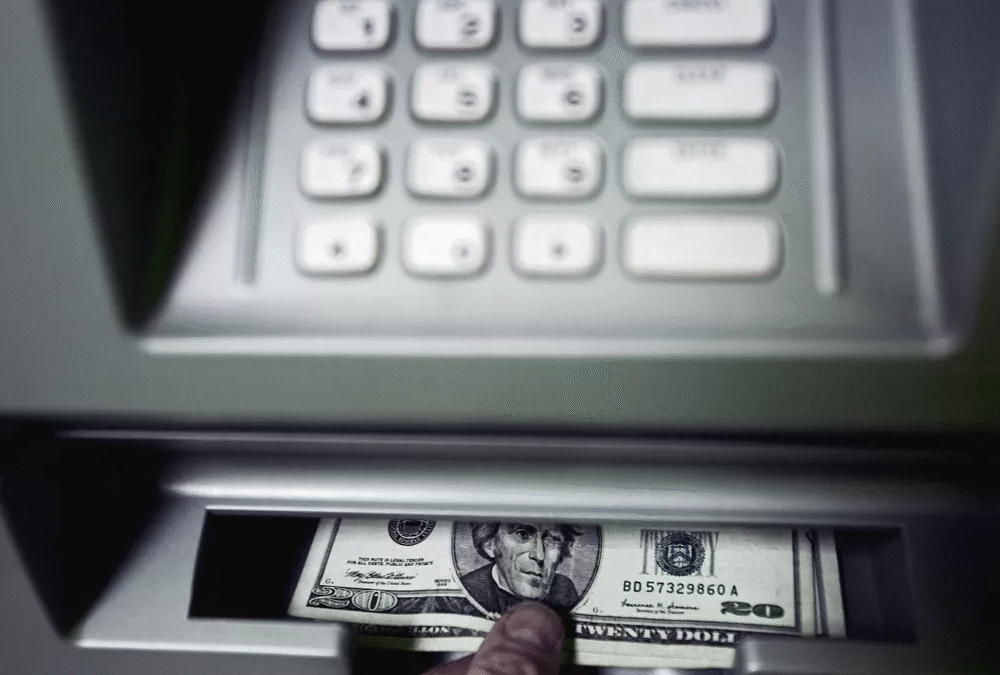
Automatic Teller Machines (ATM) have long been a target of enterprising criminals. In the 1980's when...
Read more
The Internet of Things (IoT) is any device or machine that has the ability to transfer data over a...
Read more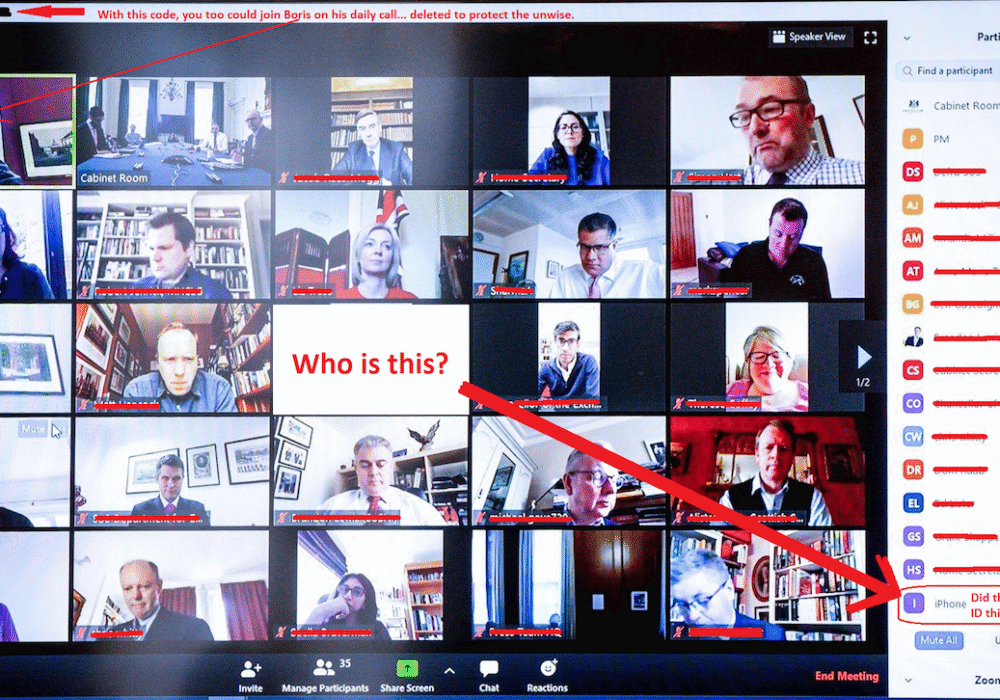
Zoom Bombing is where an unauthorized person enters your Zoom video conference to cause disruptions or to gain...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
