"After 9 months of CyberHoot awareness training, a Financial Management firm with $4 Billion in assets was phish tested by the Fellsway Group. They had zero (0%) employees click on the phishing test. In contrast, the exact same phishing attack..."

Image Source Enterprise Risk Management is a comprehensive approach to risk management that...
Read more
A Cryptographic Algorithm is a well-defined computational procedure that takes variable inputs, including a...
Read more
Image Source An Industrial Control System is an information system used to control industrial...
Read more
Image Source An investigation is a systematic and formal inquiry into a qualified threat or...
Read more
Image Source Continuity of Operations Plan (COOP) is a document that sets forth procedures for the...
Read more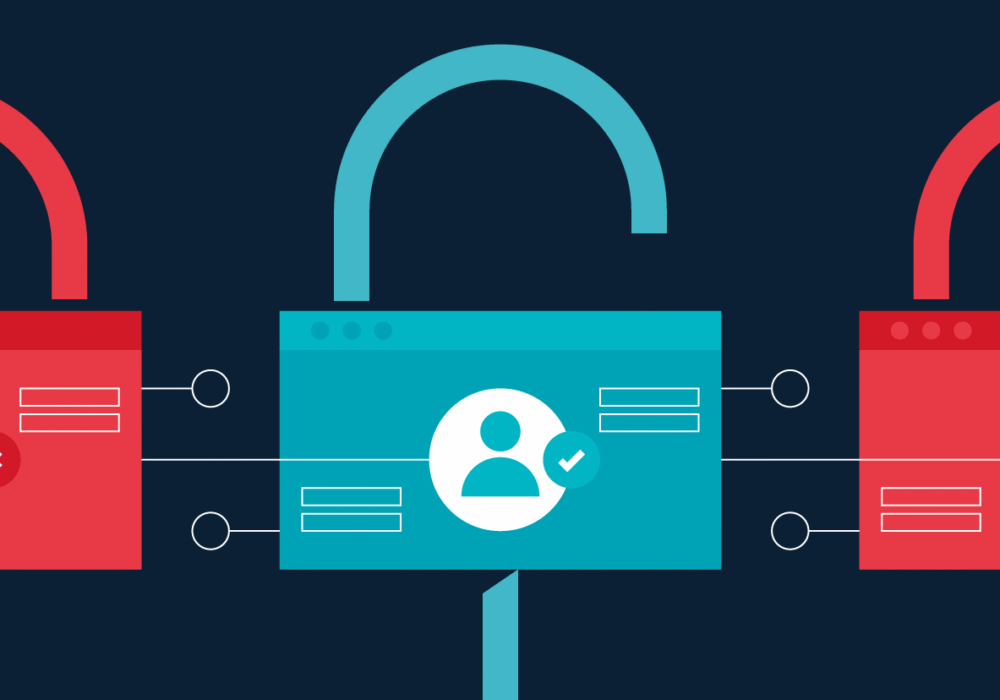
Access Control Access control is a security technique that regulates who or what can view or use...
Read more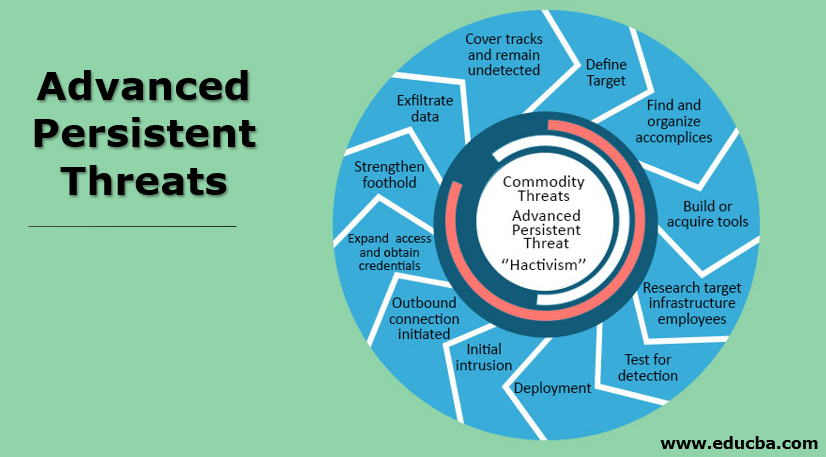
An Advanced Persistent Threat (APT) is an adversary that possesses sophisticated levels of expertise and...
Read more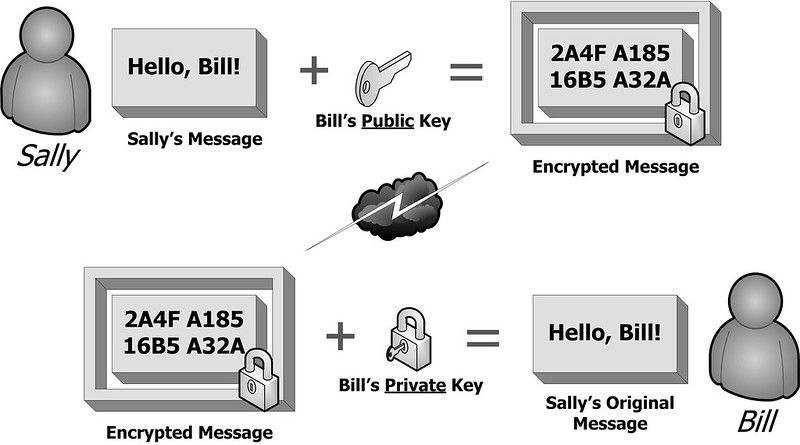
Image Source Public Key Cryptography is technically known as asymmetric encryption, is a...
Read more
Image Source An Adversary is an individual, group, organization, or government that conducts or has...
Read more
Image Source Antivirus Software is a program that monitors a computer or network to detect or...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
