"CyberHoot has been a game-changer for us - simple to deploy, highly effective in raising awareness, and a great fit for MSPs looking to strengthen client security postures without adding complexity."
Encryption is the process of transforming plaintext into ciphertext. This is done by converting data...
Read more
Image Source Incident Response is the activities that address the short-term, direct effects of an incident...
Read more
Image Source Integrated Risk Management is the structured approach that enables an enterprise or...
Read more
Image Source Enterprise Risk Management is a comprehensive approach to risk management that...
Read more
A Cryptographic Algorithm is a well-defined computational procedure that takes variable inputs, including a...
Read more
Image Source An Industrial Control System is an information system used to control industrial...
Read more
Image Source An investigation is a systematic and formal inquiry into a qualified threat or...
Read more
Image Source Continuity of Operations Plan (COOP) is a document that sets forth procedures for the...
Read more
So similar to the real deal as to be disconcerting... Technology is always improving and hackers are always...
Read more
Access Control Access control is a security technique that regulates who or what can view or use...
Read more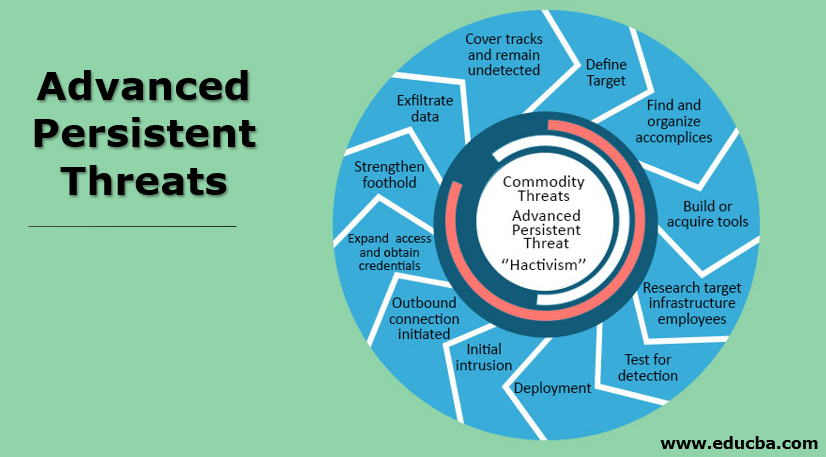
An Advanced Persistent Threat (APT) is an adversary that possesses sophisticated levels of expertise and...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
