"CyberHoot has been a game-changer for us - simple to deploy, highly effective in raising awareness, and a great fit for MSPs looking to strengthen client security postures without adding complexity."
Discover and share the latest cybersecurity trends, tips and best practices – alongside new threats to watch out for.

Introduction: As a Managed Service Provider (MSP), your main aim is to enhance your clients' operational...
Read more
Cybercriminals are always looking for new ways to infiltrate your devices. Recently, they've been using...
Read more
January 14th, 2020: Today Microsoft released their monthly patches and amongst them were three critical Severity...
Read more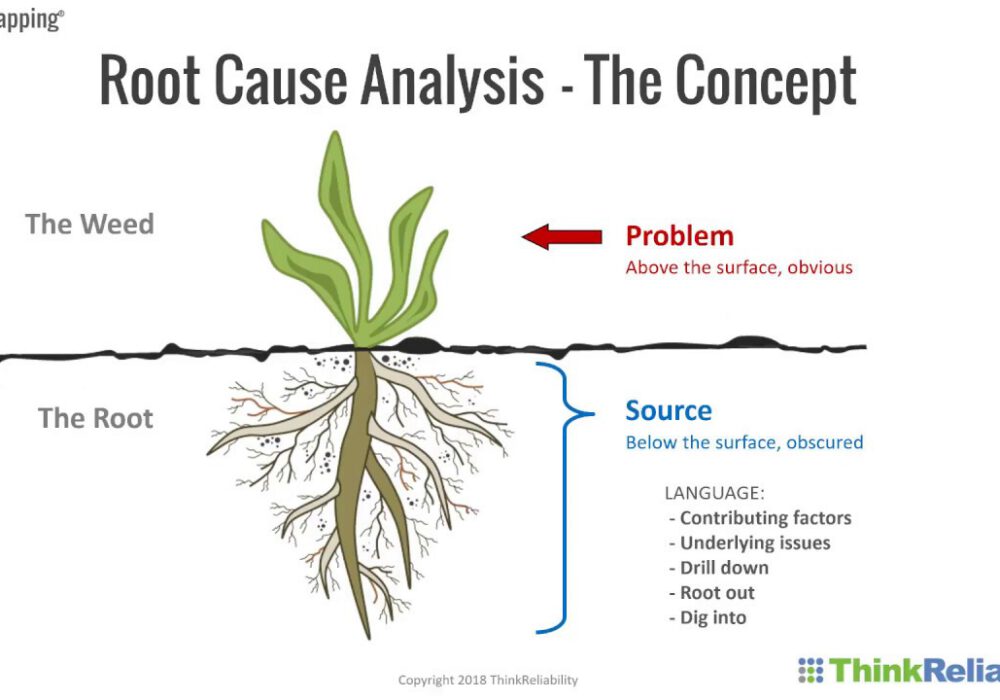
Root Cause Analysis (or RCA) is a vital tool for all businesses to use when evaluating...
Read more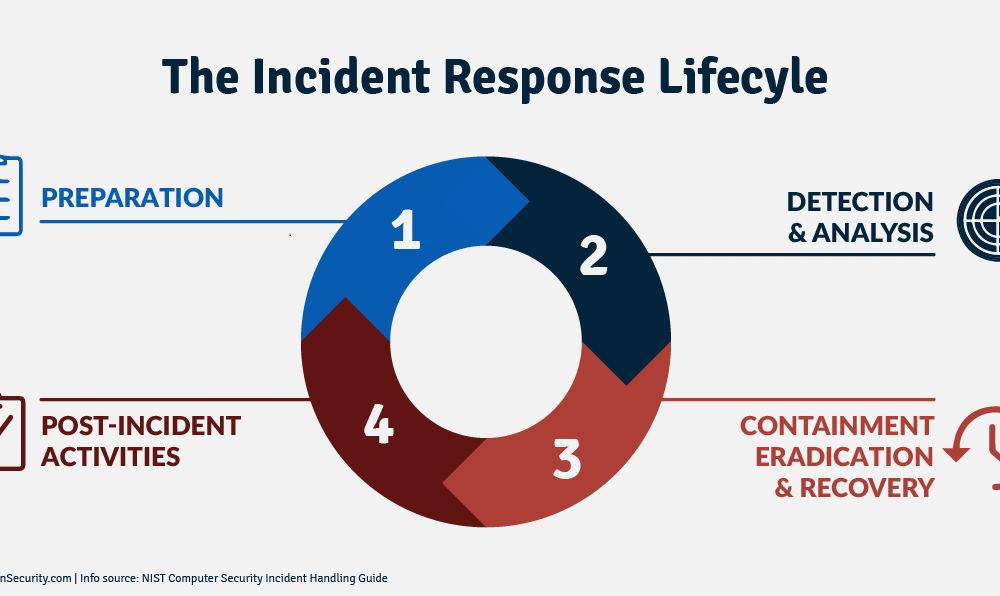
Eradication refers to what happens following containment of a cyber attack incident. After the...
Read more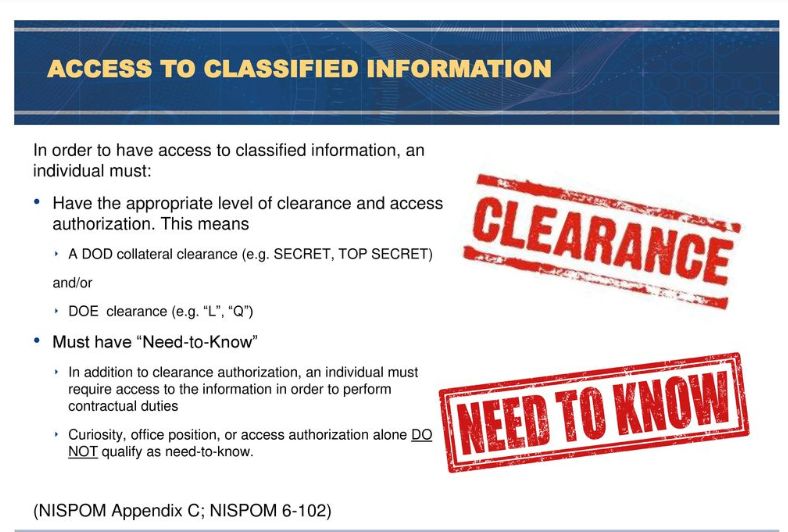
Need to Know is a term that applies to sensitive and often classified information. It is a...
Read more
Image Source Cloud Computing is a model for enabling on-demand network access to a shared pool of...
Read more
Computer Network Defense is the actions taken to defend against unauthorized activity within computer...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
