
April 14th 2020: The MSP Alliance, a 20 year old and 30,000 member online community of MSPs and Cloud Service Providers, interviewed CyberHoot and one of its MSP Resellers – Neoscope – on the importance of cybersecurity programs and awareness training. Checkout the 27 min podcast!
“I absolutely endorse the “CyberHoot” program. Watching these monthly videos has definitely helped our staff spot the bogus emails that we get on occasion. The videos have taught us what to look for and what to do if they we get a suspicious phishing attack email. Thank you CyberHoot! I’m now more aware and more secure!”

Meighan Garnsey
Controller | Bald Peak Colony Club
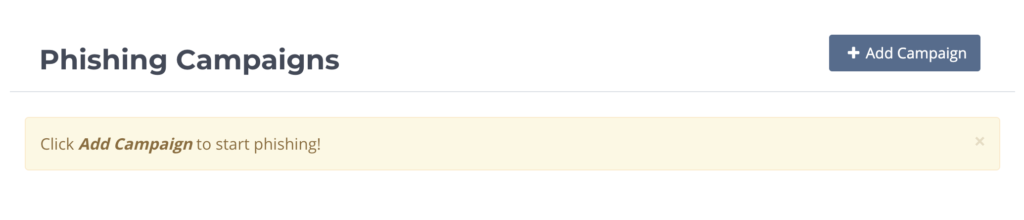
CyberHoot has launched our “Phish Testing” module for all MSP’s to use with their existing clients and prospects. The Phishing module allows administrators to create new and convincing phishing test campaigns to test employees. This testing will encourage employees to stay vigilant watching for and avoiding phishing attacks in their email.
This important module can also helps MSPs pursue and win new clients. A strategic phishing campaign, combined with dark web reports, should show business owners the critical need they have to implement a strong awarenss training program that teaches the most needed cybersecurity skills. CyberHoot has seen that once SMB owners see how many employees clicked on a phishing email, perhaps even entering password credentials, they’re much more willing to purchase MSP security solutions to close and eliminate these gaps. It’s a WIN-WIN for both the MSP and their existing or future Client.
CyberHoot is committed to building tools that empower MSPs to sell, deploy, and support a robust cybersecurity programs for themselves and to their clients.
CYBRARY: HTTPS://CYBERHOOT.COM/CYBRARY/
Dozens of blog articles with detailed analysis and recommendations on hot cybersecurity topics.
Many searchable Administration How To articles from one screen.

CyberHoot “Hoots” are often 5 minutes or less. This ensures your staff get trained quickly with the most effective solution.
CyberHoot is an open cybersecurity training Platform. Any video or PDF can be used to train and govern your employees.

CyberHoot is mandatory company assigned training that takes time and adds work for employees;
yet, over 60% of 100 CyberHoot users surveyed would be “Disappointed” or “Very Disappointed” if CyberHoot was taken away!
Discover and share the latest cybersecurity trends, tips and best practices – alongside new threats to watch out for.

As smart homes get smarter, so do their habits of watching, sensing, and reporting. Enter WiFi Motion Detection, a...
Read more
Spoiler alert: If you’re still using “password123” or “iloveyou” for your login… it’s time for an...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
