"After 9 months of CyberHoot awareness training, a Financial Management firm with $4 Billion in assets was phish tested by the Fellsway Group. They had zero (0%) employees click on the phishing test. In contrast, the exact same phishing attack..."
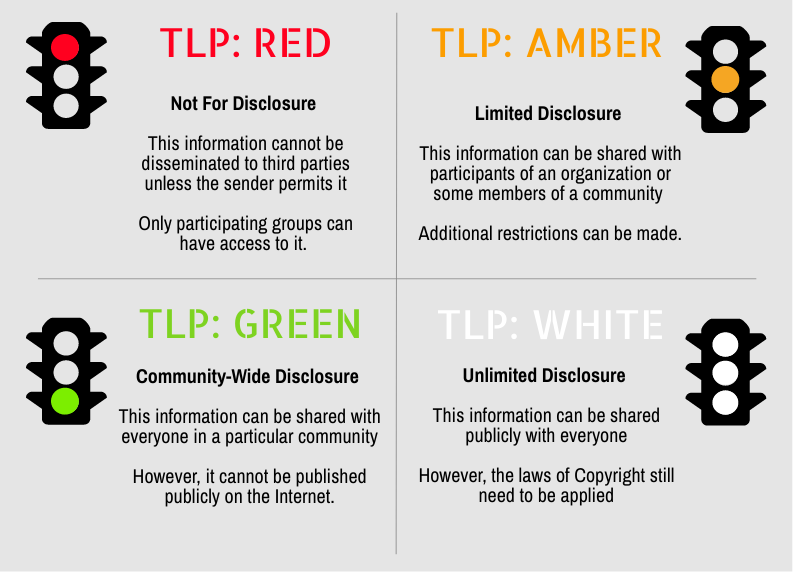
Secure your business with CyberHoot Today!!! Sign Up Now Traffic Light Protocol (TLP) is a set of...
Read more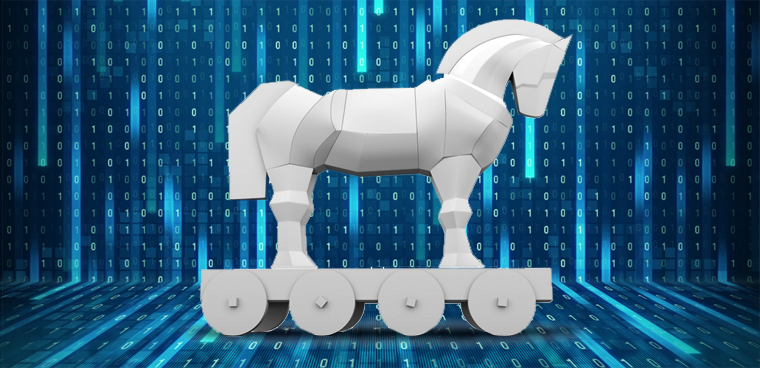
A Trojan Horse is a computer program that appears to have a useful function, but also has a hidden and...
Read more
Image Source A vulnerability is a characteristic or specific weakness that renders an organization...
Read more
An Allow list, also known as a Permit List or (deprecated: White List), is a list of...
Read more
Image Source A Work Factor is an estimate of the effort or time needed by a potential adversary, with...
Read more
Image Source Tokenization is a way for credit card information (also called the Primary Account Number or...
Read more
Image Source Continuity of Operations Plan (COOP) is a document that sets forth procedures for the...
Read more
Image Source A White Team is a group responsible for refereeing an engagement between a Red Team...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
