"CyberHoot has been a game-changer for us - simple to deploy, highly effective in raising awareness, and a great fit for MSPs looking to strengthen client security postures without adding complexity."
Intellectual Property (IP) refers to the ownership of a specific idea, design, manuscript, etc. by the...
Read more
The ILOVEYOU Virus, also known as, the Love Bug, is a computer worm that infected over 10 million...
Read more
This HowTo video outlines how to restore an archived user or employee in a Training Program. When an archived...
Read more
Mandatory Controls, also known as Mandatory Access Controls (MAC), are a type of access control that...
Read more
Discretionary Access Controls, also known as DAC, are types of cybersecurity measures that allow or...
Read more
Sensitive (or restricted) Information is data from a company or organization that is generally not...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Critical (or Confidential) Information in a...
Read more
Clearview AI has created one of the broadest and most powerful facial recognition databases in the...
Read more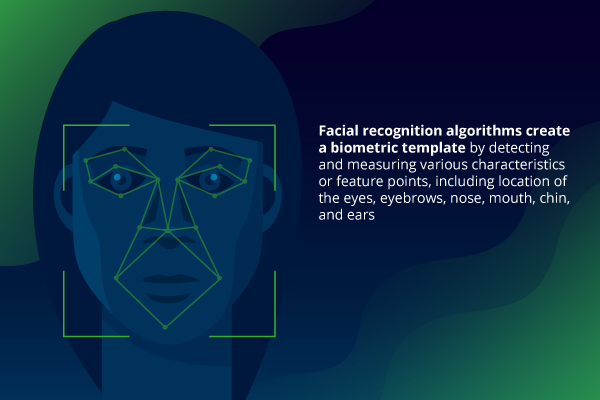
Facial Recognition is an increasingly effective and popular technology capable of identifying a...
Read more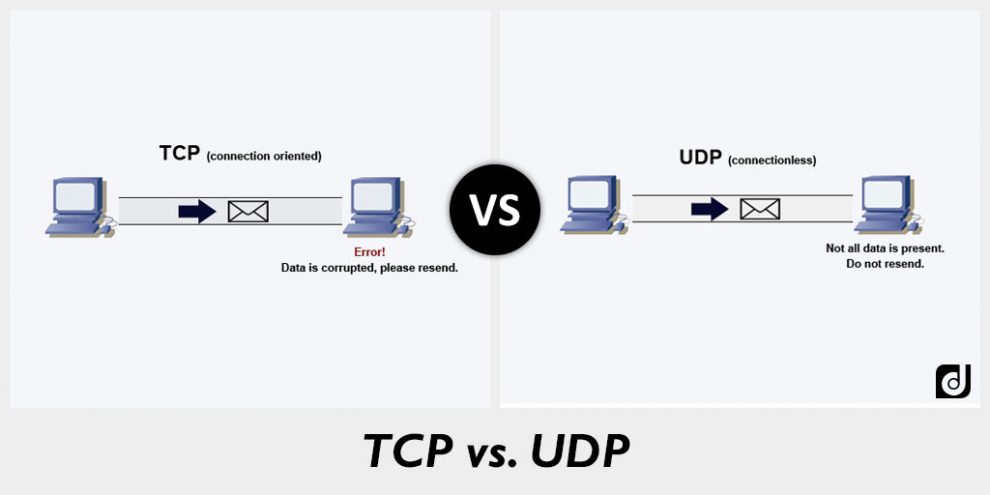
User Datagram Protocol (UDP) is an alternative communications protocol to Transmission Control Protocol...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
