"CyberHoot is an excellent cybersecurity training platform that educates teams on security practices through training content, phishing simulations, and actionable analytics."
The Internal Revenue Service (IRS) announced this week that in January 2021 taxpayers can apply for an...
Read more
How can I adjust my payment/billing information? Sign in with your credentials (Administrators) Click on your...
Read more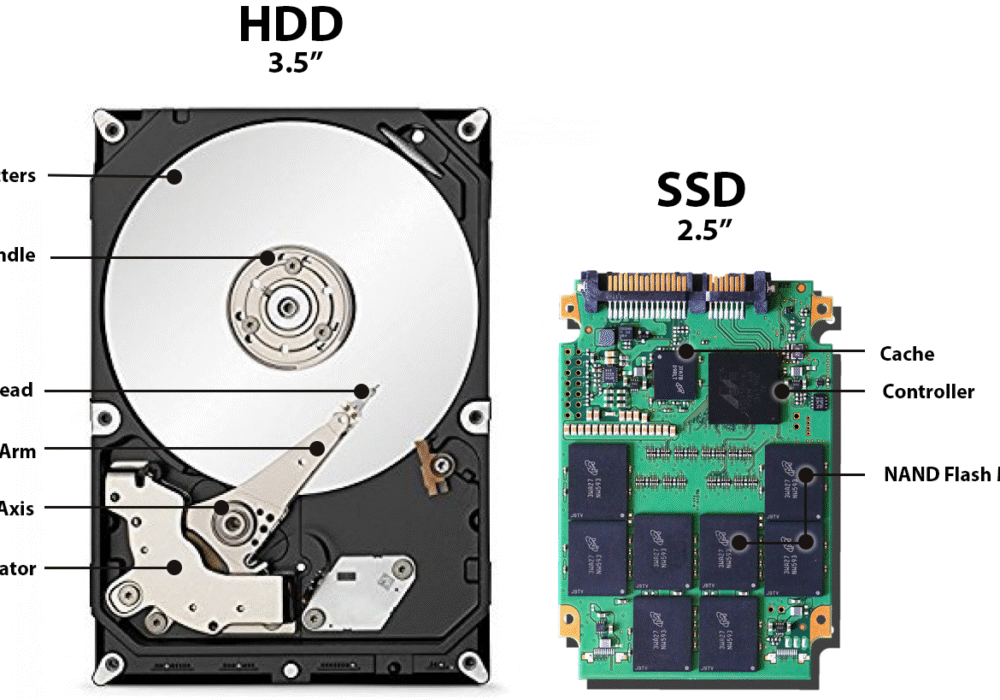
A Hard Disk Drive (HDD), also known as a hard drive, is a computer storage device holding magnetic...
Read more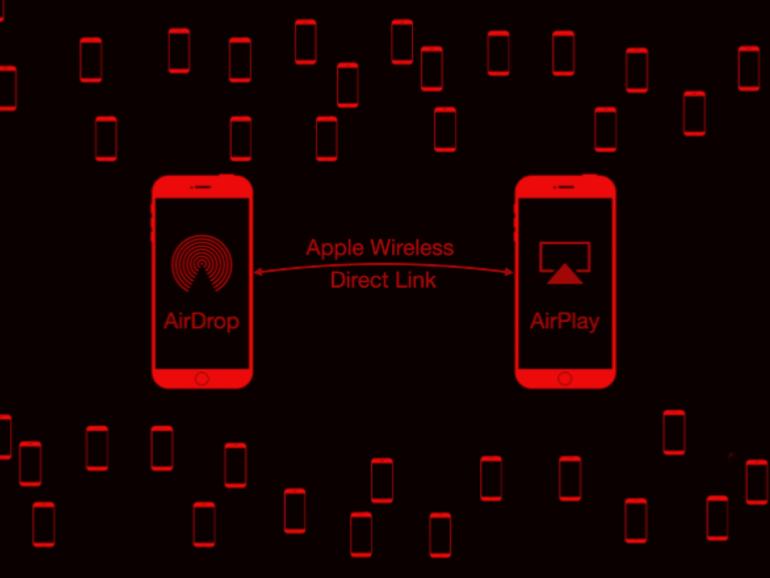
Google's Project Zero cybersecurity researcher (and white-hat hacker) Ian Beer published an article in...
Read more
A Polymorphic Virus is a type of 'shape-shifting' virus, producing malicious code that is able to...
Read moreApple Wireless Direct Link (AWDL) is a low latency/high-speed Wi-Fi peer-to peer-connection Apple uses...
Read more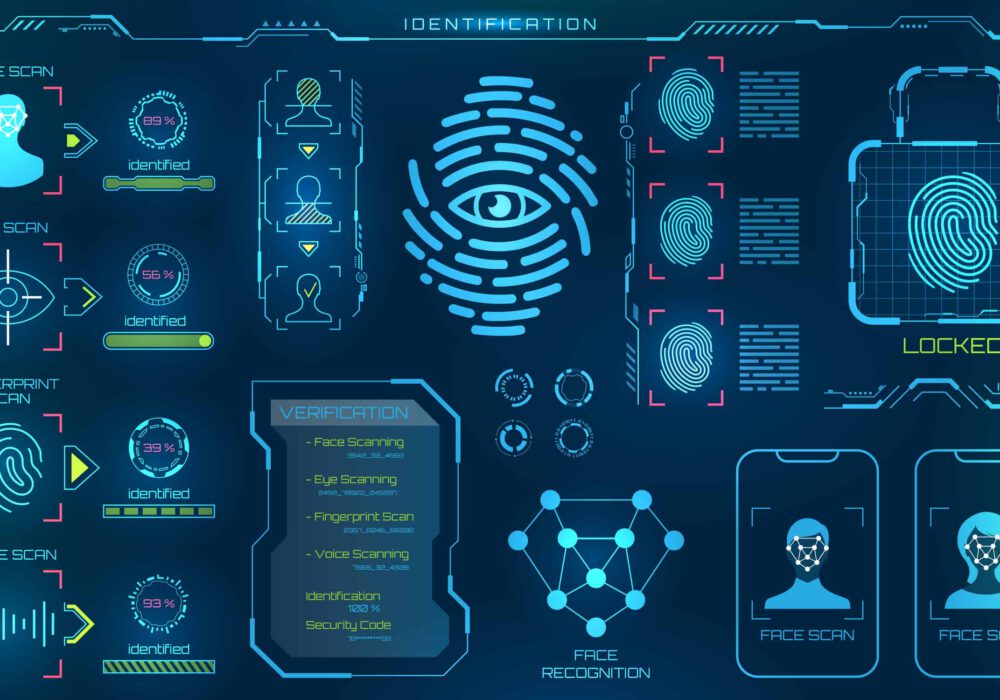
Biometrics identification refers to computer-based data that identifies a person based on unique...
Read more
A Parasitic Virus, also known as a file virus, is spread by attaching itself to executable programs....
Read more
A Boot Sector Virus is a virus that infects the 'boot sector' of floppy disks or the 'Master Boot...
Read more
A Macro Virus is a virus that adds its code to the macros embedded within documents, spreadsheets,...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
