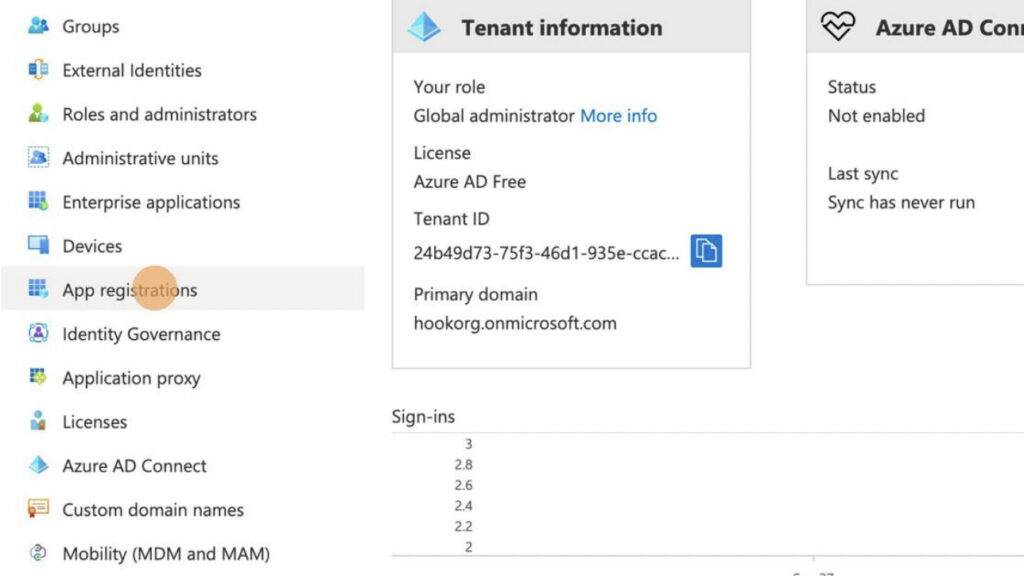
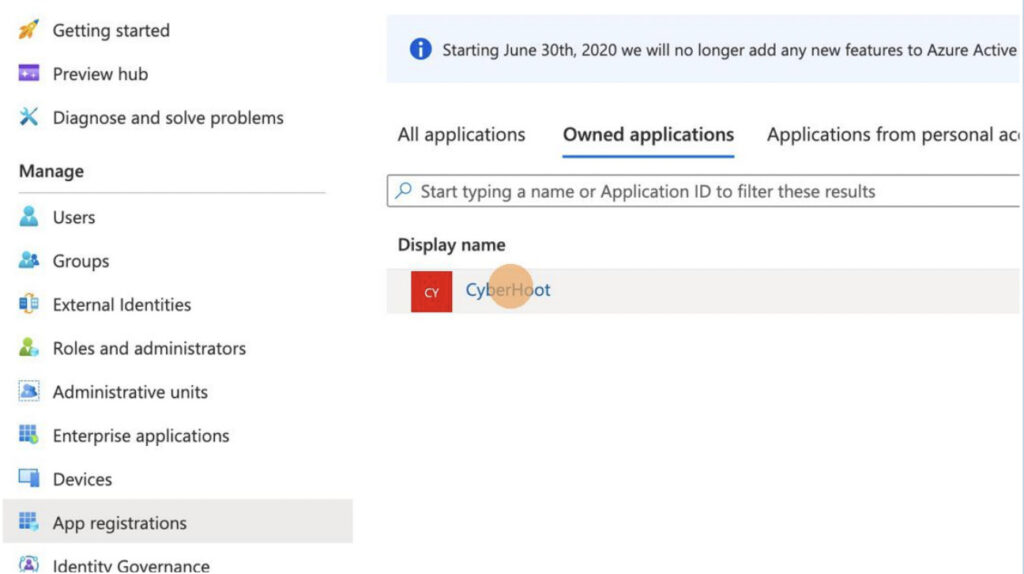
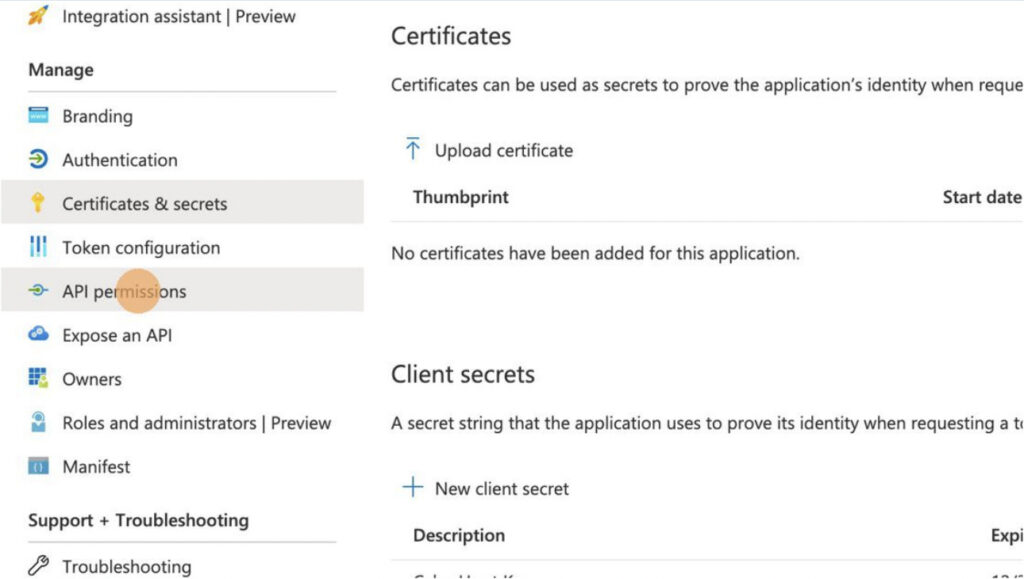
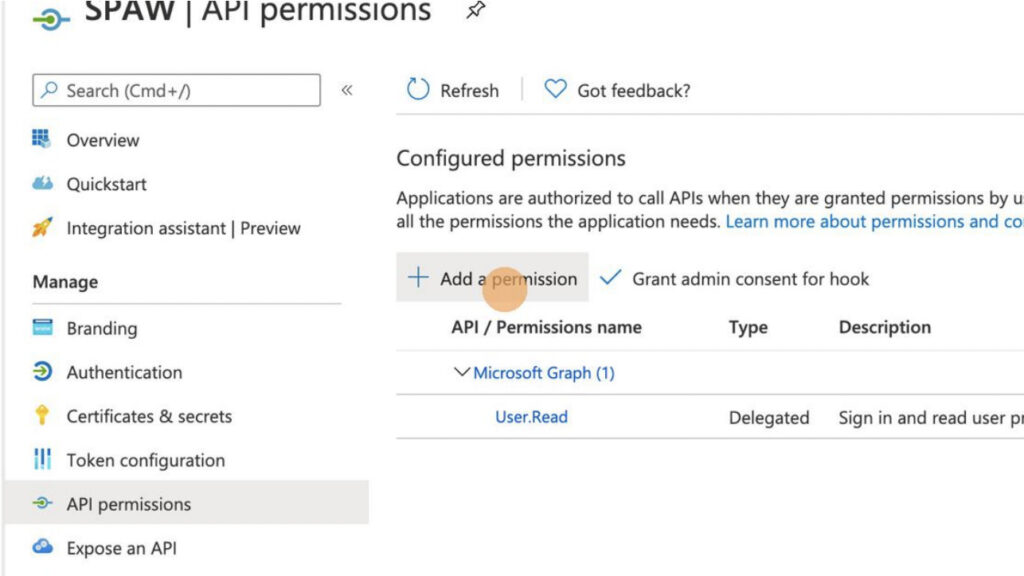
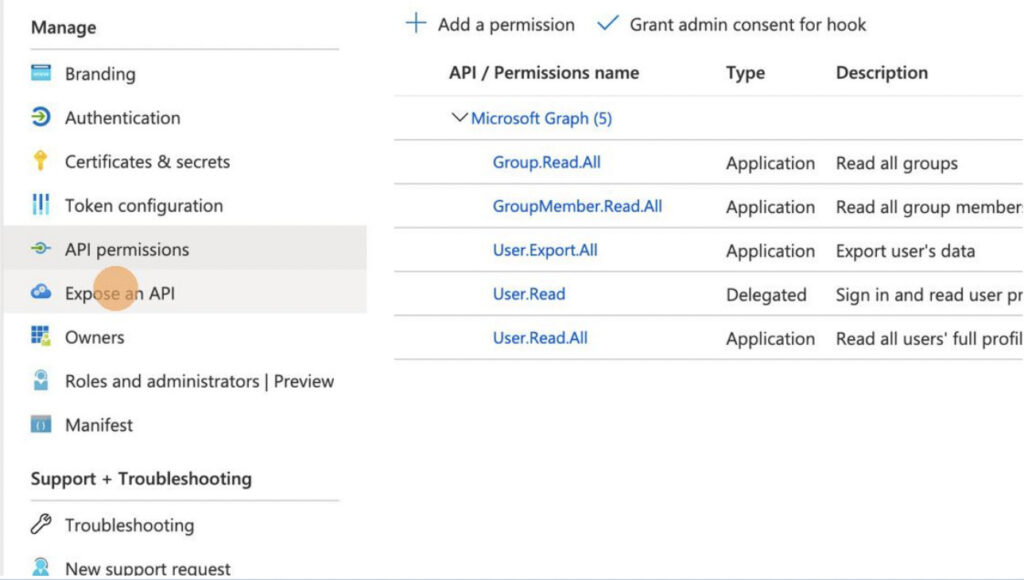
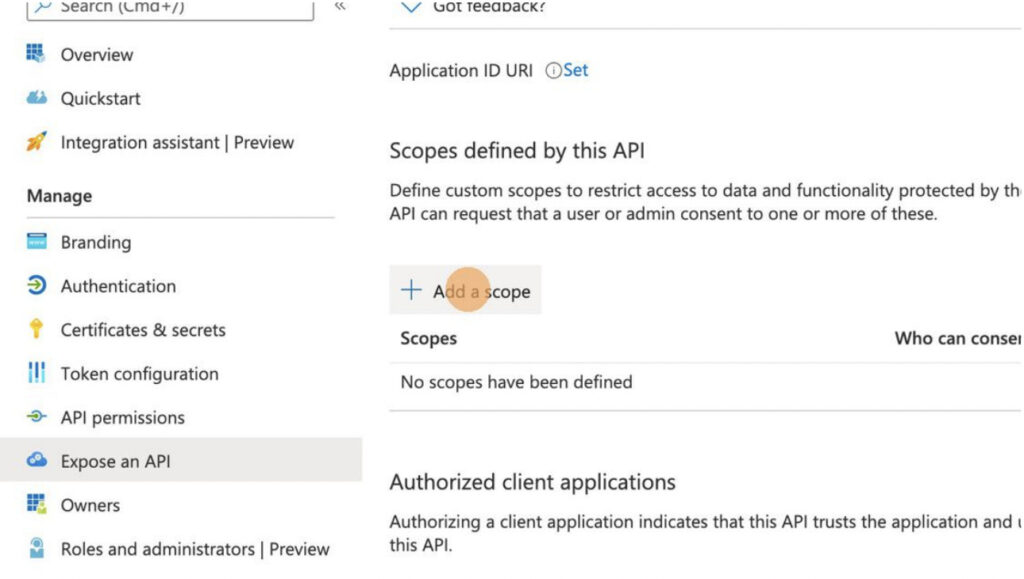
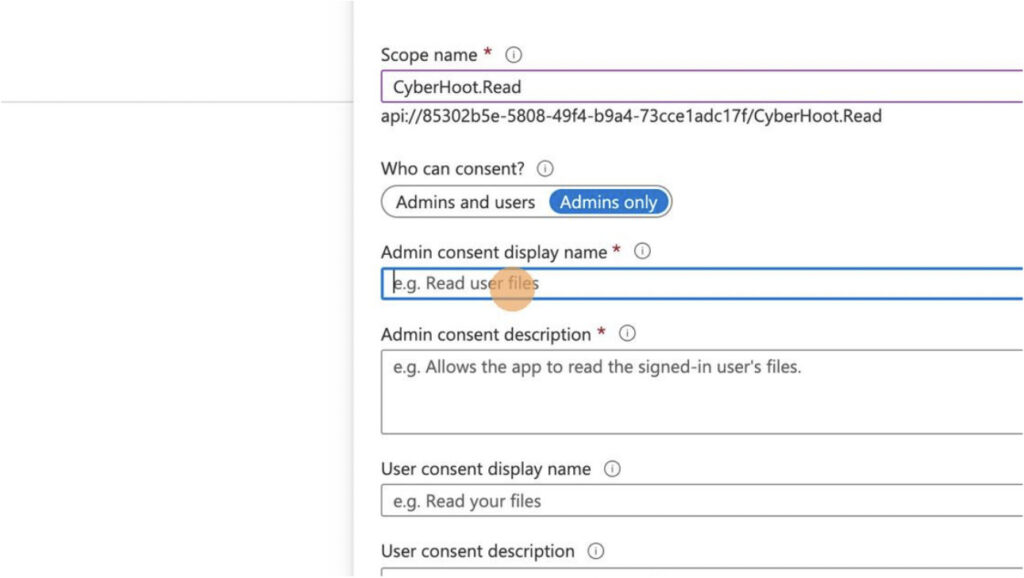
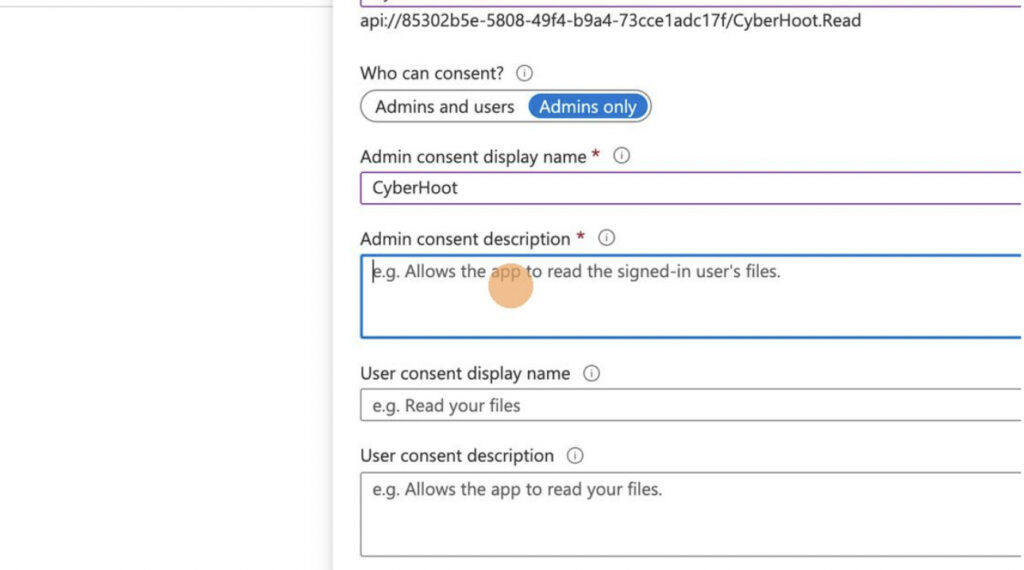
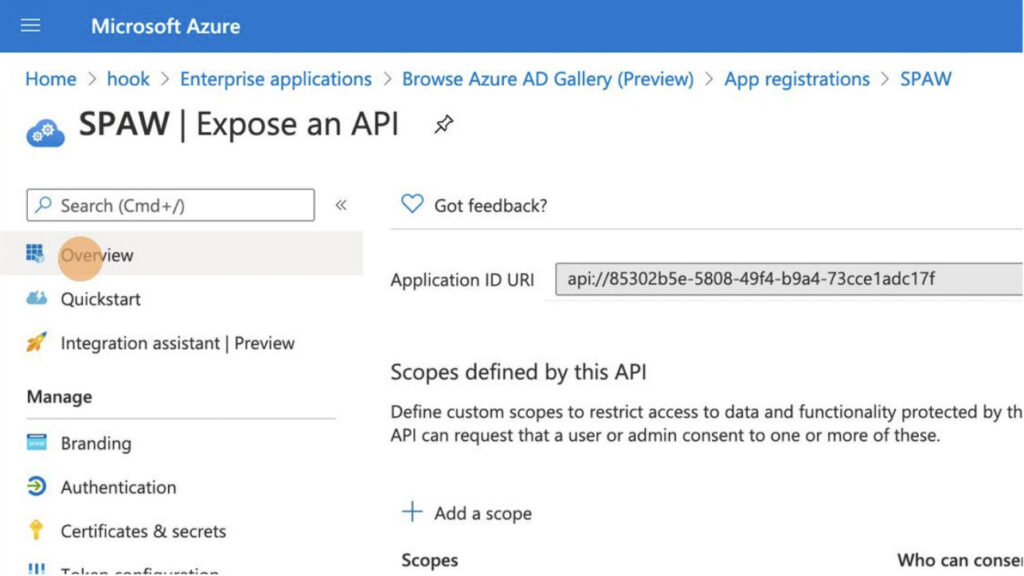
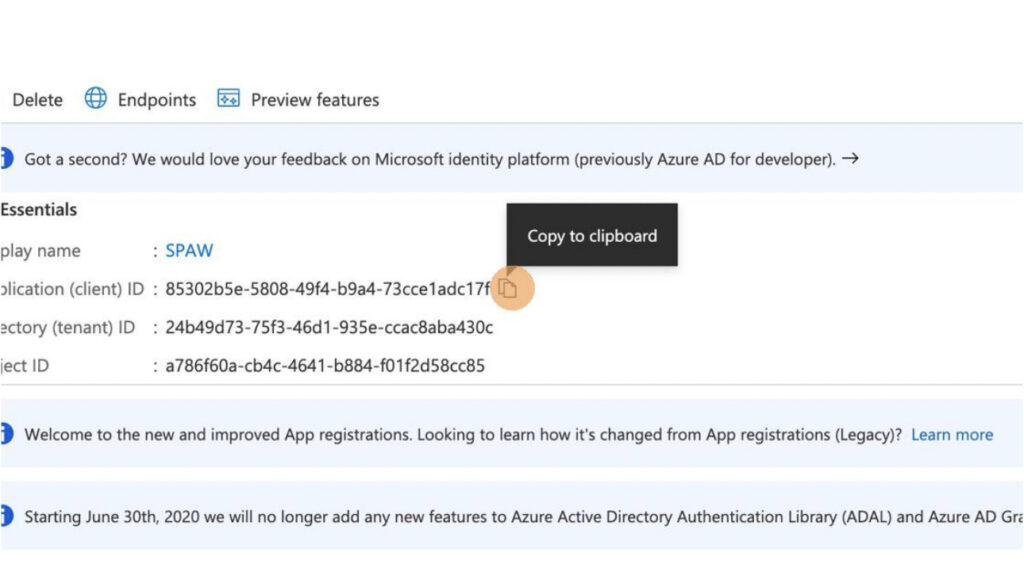
Please note: Only Azure AD Government Community Cloud (GCC) environments need to follow these instructions.
For more instructional ‘HowTo’ videos, head over to our HowTo Library for more guidance. If you’re unsure where to start, review the following recommended videos and articles around common Administrator (or SuperAdministrator) pain points:
Discover and share the latest cybersecurity trends, tips and best practices – alongside new threats to watch out for.

A Practical Brief for vCISOs THE WARNING WE IGNORED OR COULD NOT UNDERSTAND For years, the most credible...
Read more
A guide to spotting senior executive impersonation scams before the fake CEO gets a real wire transfer. It...
Read more
Artificial Intelligence (or AI) is making phishing emails smarter, malware sneakier, and credential theft easier...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
