"CyberHoot is a great option for Cybersecurity for our schools. The videos and other training are very user-friendly. Their support is fantastic as well."
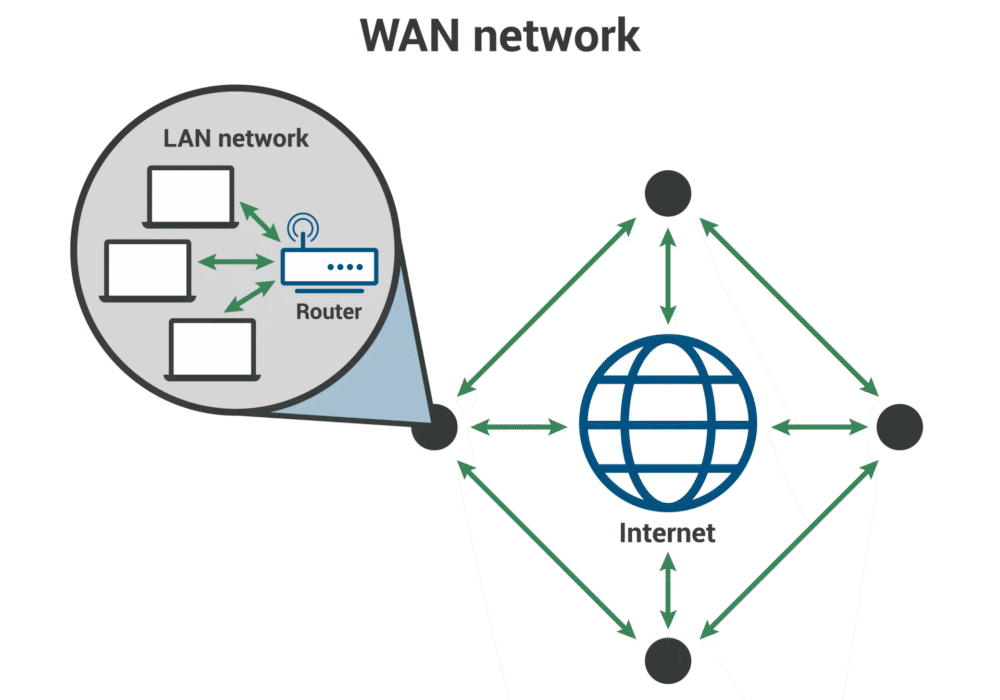
Secure your business with CyberHoot Today!!! Sign Up Now A Wide Area Network (WAN) is a large...
Read more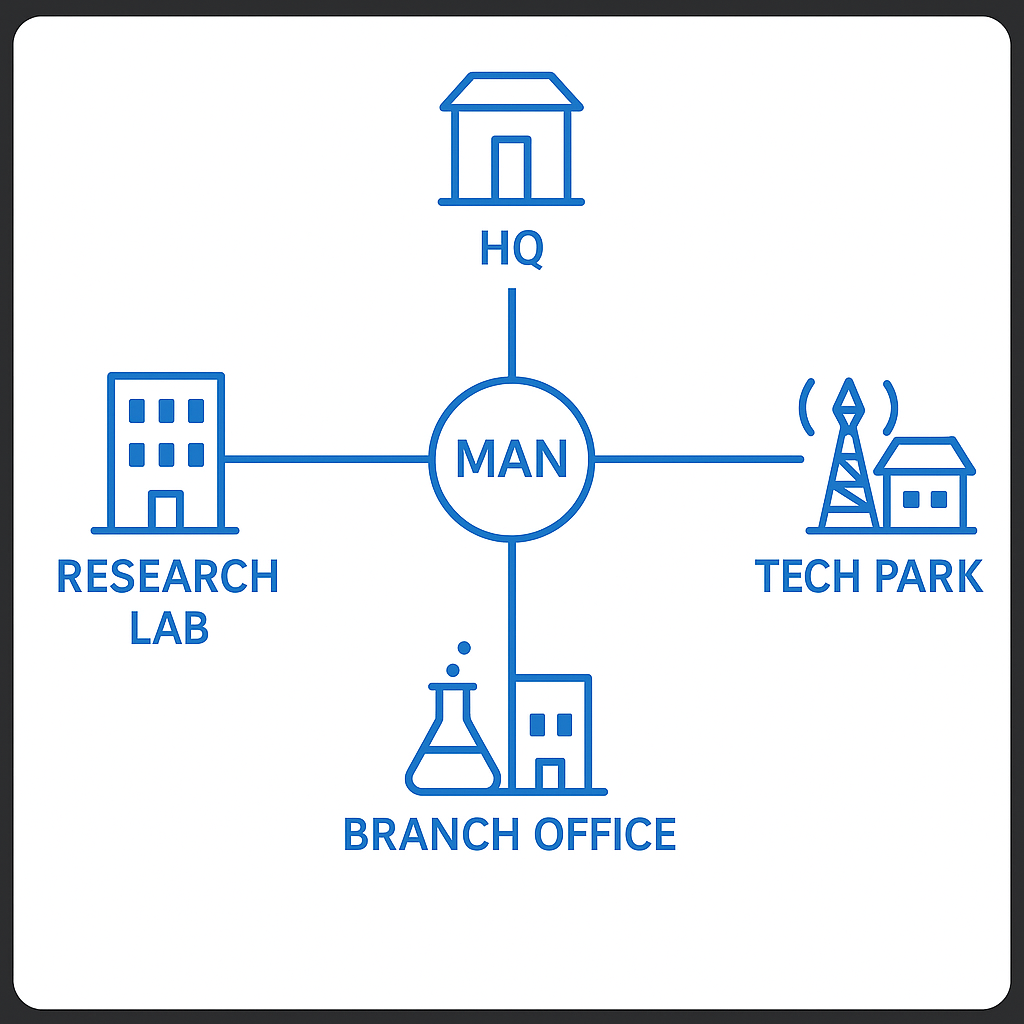
Secure your business with CyberHoot Today!!! Sign Up Now A Metropolitan Area Network (MAN) is a...
Read more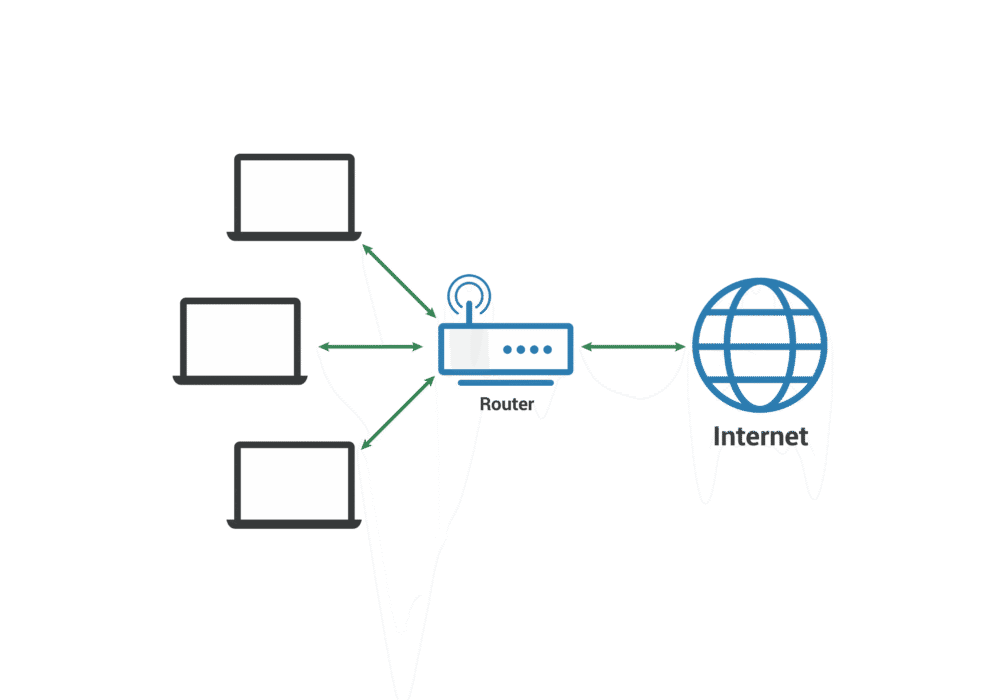
Secure your business with CyberHoot Today!!! Sign Up Now A Local Area Network (LAN) is a group of...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Error Detection in cybersecurity refers to...
Read more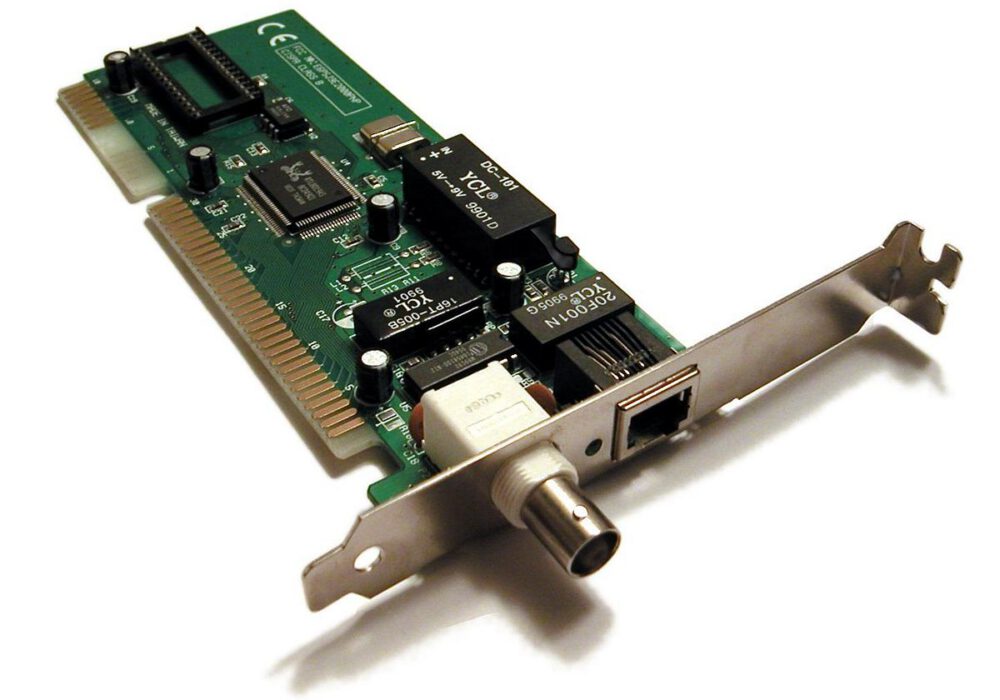
Secure your business with CyberHoot Today!!! Sign Up Now A Network Interface Card (NIC) provides...
Read more
The Open Systems Interconnection (OSI) Model is a conceptual model created by the International...
Read more
Layer 2 Networks refers to the second layer of the Open Systems Interconnection (OSI) Model, which is...
Read more
A Layer 3 Network is the third layer of the Open Systems Interconnection (OSI) Model, or network layer....
Read more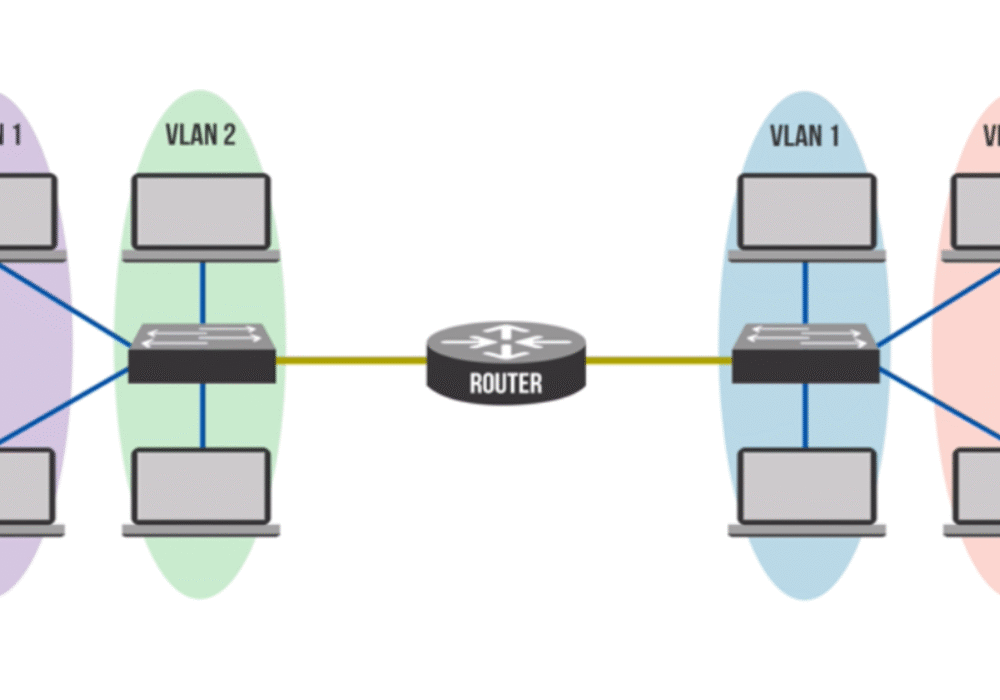
Private Virtual Local Area Network (PVLAN), also known as port isolation, is a network...
Read more
Fleeceware is a malicious application that tricks users into paying money for simple apps with...
Read more
Peer-to-Peer (P2P) Networks exist where groups or "peers" of computer systems are linked to each other through...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
