Vulnerability Scanning is the process of identifying security weaknesses and coding flaws in systems and software running on them. This is a vital component of a vulnerability alert management program, which has one overarching goal; to protect the organization from breaches and the exposure of critical and/or sensitive data. These programs rely on assessments to gauge security readiness and minimize risk, and vulnerability scanning is a critical tool in the cybersecurity toolbox.
A vulnerability scanner is an application that identifies and creates an inventory of all systems connected to a network. For each device that it identifies, it attempts to identify the operating system running, user accounts, open ports and protocols, and related software installed on the system. After building up an inventory, the vulnerability scanner checks each item in the inventory against one or more databases of known vulnerabilities. The result is a list of all the systems found and identified on the network, highlighting any that have known vulnerabilities and need attention.
Vulnerability scanning should be performed at SMBs to improve their cybersecurity defenses. Adding this tool into your VAMP toolbox can be highly beneficial as it helps identified a variety of entry points for hackers; from misconfiguration, to vulnerable software that needs upgrading and patching, a vulnerability scan can dramatically improve your cybersecurity defenses.
In addition to vulnerability scanning, SMBs should include all of the following activities and solutions to enhance their cybersecurity protections:
CyberHoot does have some other resources available for your use. Below are links to all of our resources, feel free to check them out whenever you like:
Note: If you’d like to subscribe to our newsletter, visit any link above (besides infographics) and enter your email address on the right-hand side of the page, and click ‘Send Me Newsletters’.
Sources:
Additional Reading:
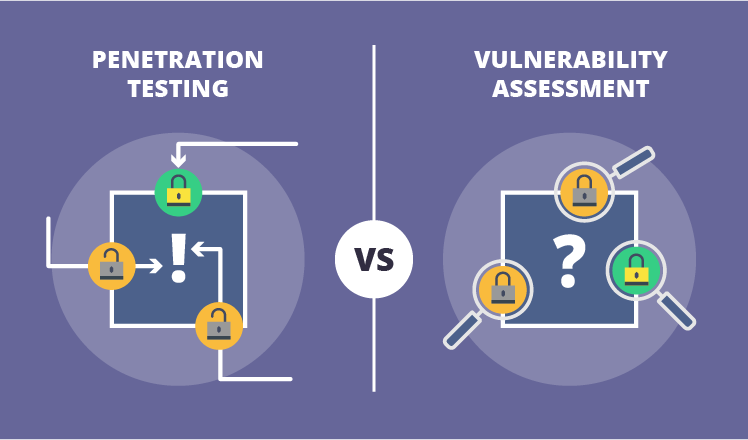
Vulnerability Scanning and Penetration Testing
Vulnerability Alert Management Process (VAMP)
Discover and share the latest cybersecurity trends, tips and best practices – alongside new threats to watch out for.

A Practical Brief for vCISOs THE WARNING WE IGNORED OR COULD NOT UNDERSTAND For years, the most credible...
Read more
A guide to spotting senior executive impersonation scams before the fake CEO gets a real wire transfer. It...
Read more
Artificial Intelligence (or AI) is making phishing emails smarter, malware sneakier, and credential theft easier...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
