"I reviewed over a dozen learning management platforms, and I have to say, CyberHoot is soaring way above the others."
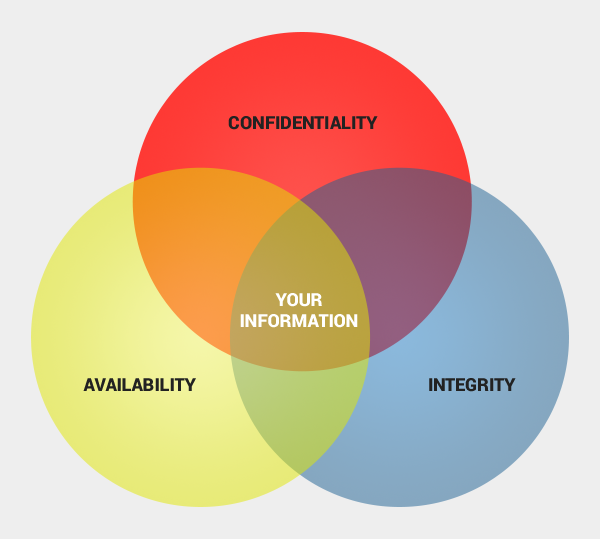
Availability is the property of being accessible and usable upon demand, where in cyber security...
Read more
Confidentiality is one of three critical data protections in cybersecurity. The other two are Integrity...
Read more
Image Source An Attack Signature is an arrangement of information that can be used to identify an attacker...
Read more
Combining public and private keys to electronically sign messages. A Digital Signature is a value computed...
Read more
Image Source Ciphertext is data or information in its encrypted form. Ciphertext is the output when an...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
