“Using CyberHoot was one of the best decisions we made regarding SAT. Fully automated, training is interesting, and staff participation is high compared to other vendors.”
Attribution in the cybersecurity world refers to the process of tracking, identifying and...
Read more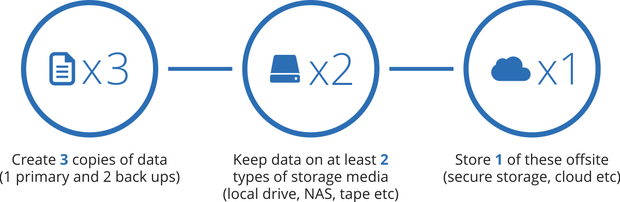
The 3-2-1 Backup Method refers to the "3-2-1 Rule" when backing up information from your...
Read more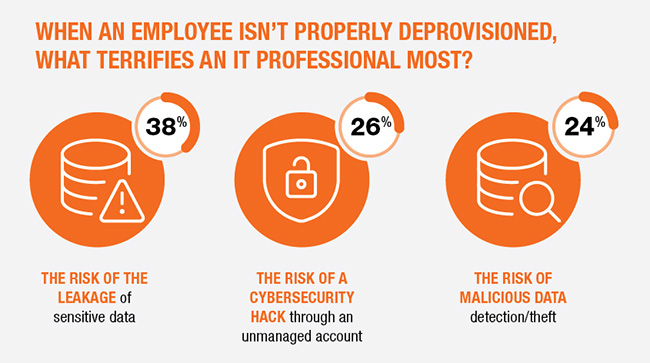
An Off Boarding Process refers to the process an organization follows to deprovision access...
Read more
Two-Factor Authentication (2FA) is the use of two of the following three identification...
Read more
Only a few days after a drone strike killed Iran's highest ranked military leader, Qassim...
Read more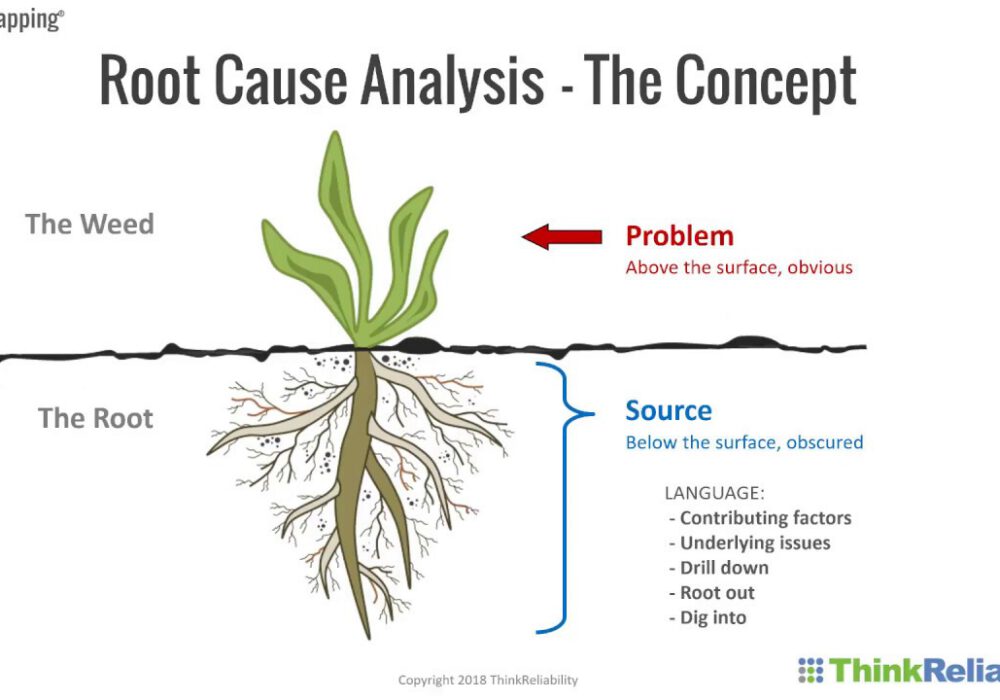
Root Cause Analysis (or RCA) is a vital tool for all businesses to use when evaluating...
Read more
Identification refers to the first step in the incident response process where an organization...
Read more
A Remote Access Trojan (RAT) is malware that includes a backdoor for administrative control...
Read more
A countermeasure in the cybersecurity world, is an action, procedure, or technique that...
Read more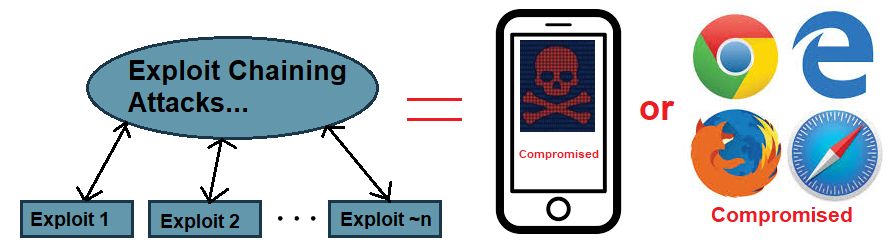
An Exploit Chain is an attack that involves multiple exploits or attacks that are chained...
Read more
RADIUS Authentication, also known as Remote Authentication Dial-In User Service (RADIUS), is a...
Read more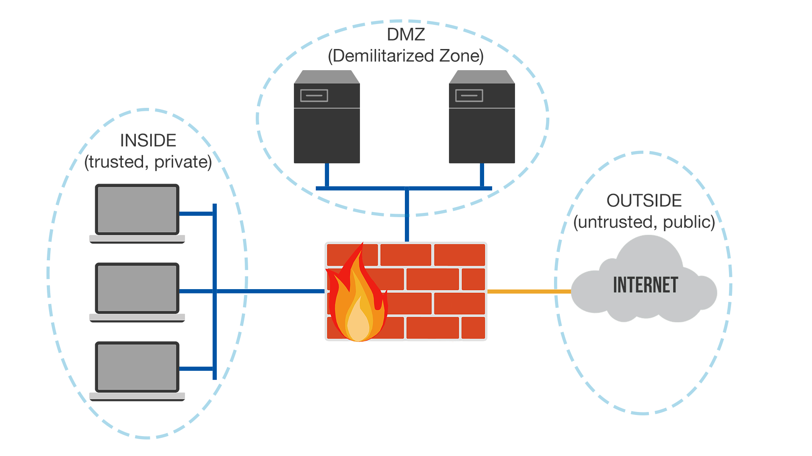
The Demilitarized Zone (DMZ) is sometimes referred to as a "perimeter network", its primary...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
