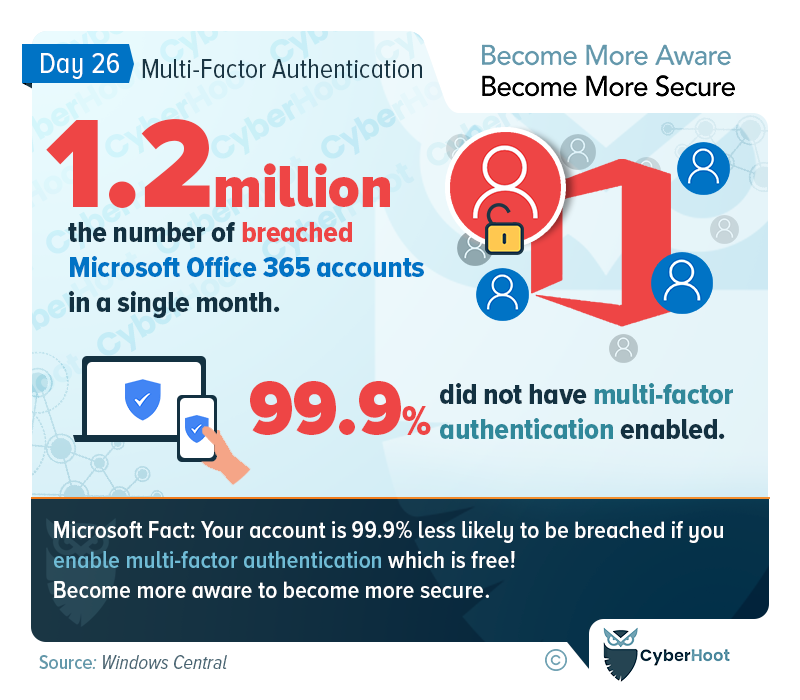
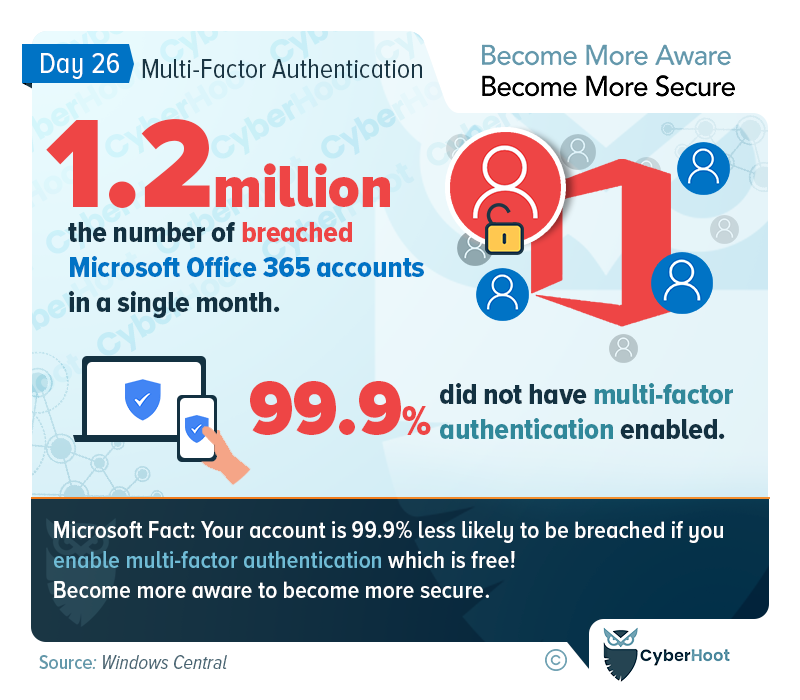
Sometimes in life, you come across a Life Hack that just leaves you stunned with how easy it is and why haven’t I adopted or used this before now? MFA or 2FA is one such Life Hack for cybersecurity that everyone needs to learn and adopt for all their online accounts. MFA or 2FA is using a second factor beside your password, to identify yourself to a SaaS application. It prevents hackers from stealing our accounts when they possess our passwords through a breach of some 3rd party website.
In addition to MFA/2FA, you should also adopt a password manager as soon as humanly possible. This is a second Life Hack that you’ll be glad you adopted mere weeks after learning how to use these two tools. Take home message: Adopt MFA / 2FA and a Password Manager as soon as possible to protect yourself online. You’ll be so happy you did!
Also consider signing up with CyberHoot and implementing the best practices shown below.
CyberHoot believes that for many small to medium sized businesses and MSPs, you can greatly improve your defenses and chances of not becoming another victim of cyberattack if you follow the advice above.
We hope you’re enjoying Cybersecurity Awareness Month (CAM). Visit or subscribe to CyberHoot’s Facebook, LinkedIn, or Twitter pages to get daily updates throughout the month.
Discover and share the latest cybersecurity trends, tips and best practices – alongside new threats to watch out for.

A Practical Brief for vCISOs THE WARNING WE IGNORED OR COULD NOT UNDERSTAND For years, the most credible...
Read more
A guide to spotting senior executive impersonation scams before the fake CEO gets a real wire transfer. It...
Read more
Artificial Intelligence (or AI) is making phishing emails smarter, malware sneakier, and credential theft easier...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
