"Using CyberHoot was one of the best decisions we made regarding SAT. Fully automated, training is interesting, staff participation is high compared to other vendors."
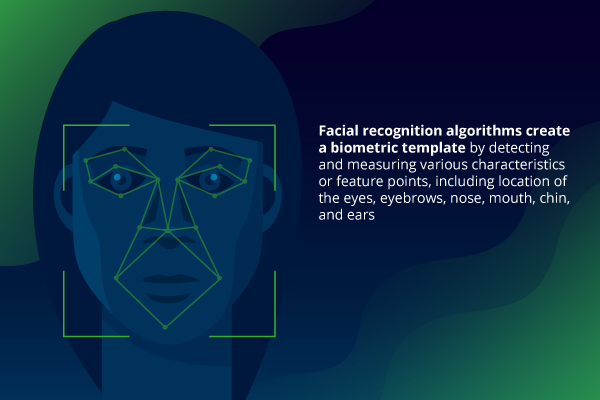
Facial Recognition is an increasingly effective and popular technology capable of identifying a...
Read more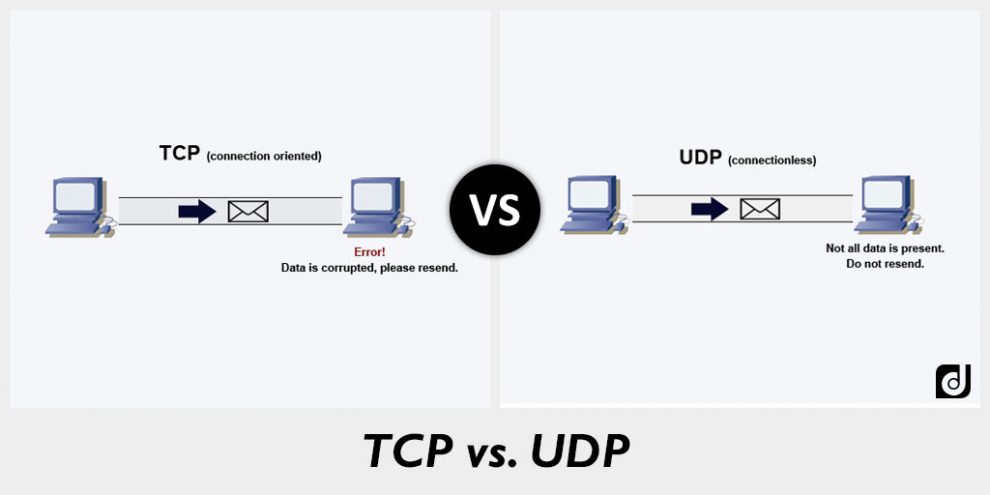
User Datagram Protocol (UDP) is an alternative communications protocol to Transmission Control Protocol...
Read more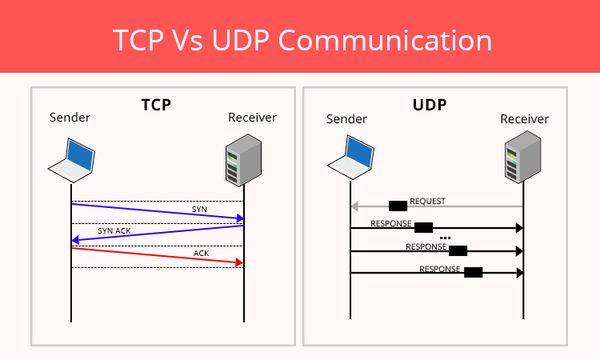
Transmission Control Protocol (TCP) is a standard that defines how to establish and maintain a...
Read more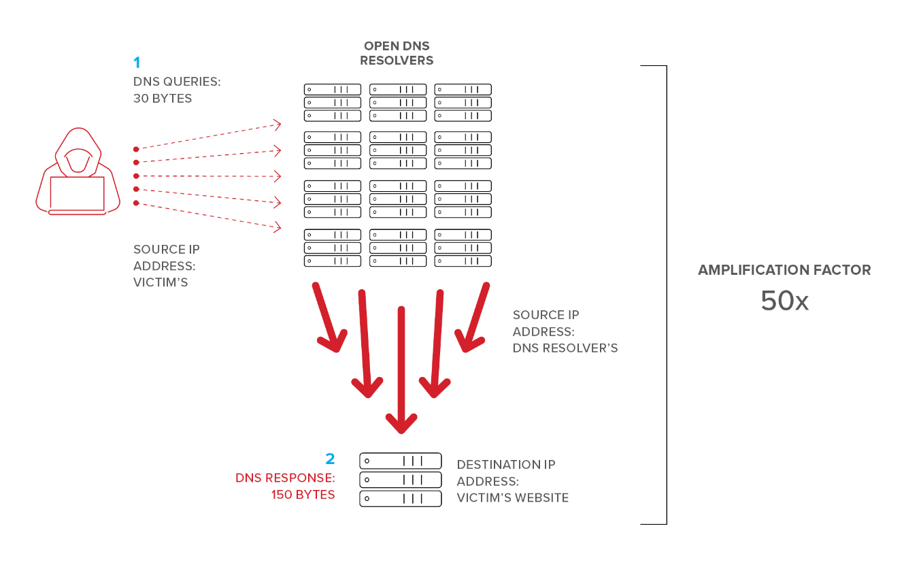
A DNS Reflection Attack, also known as a DNS Amplification Attack, is a form of a Distributed Denial of...
Read more
Hackers never cease to stop evolving and finding new ways to get your information. Hackers...
Read more
Remote Desktop Protocol (RDP) is software commonly used by customer support representatives...
Read more
A False Flag is the pretending to be one hacking entity when you are in fact another. False...
Read more
January 14th, 2020: Today Microsoft released their monthly patches and amongst them were three critical Severity...
Read more
Attribution in the cybersecurity world refers to the process of tracking, identifying and...
Read more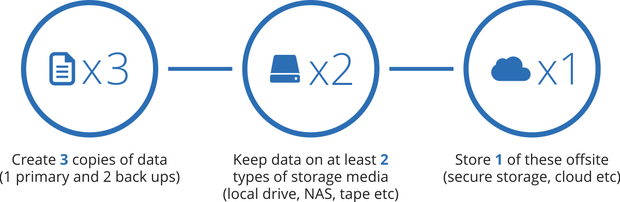
The 3-2-1 Backup Method refers to the "3-2-1 Rule" when backing up information from your...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
