"Managed Service Providers (MSP's) are constantly bombarded with new vendors and products that either overlap with a product already in our line cards or is difficult to get client buy in. Cyberhoot brings a new product/service to the MSP space..."
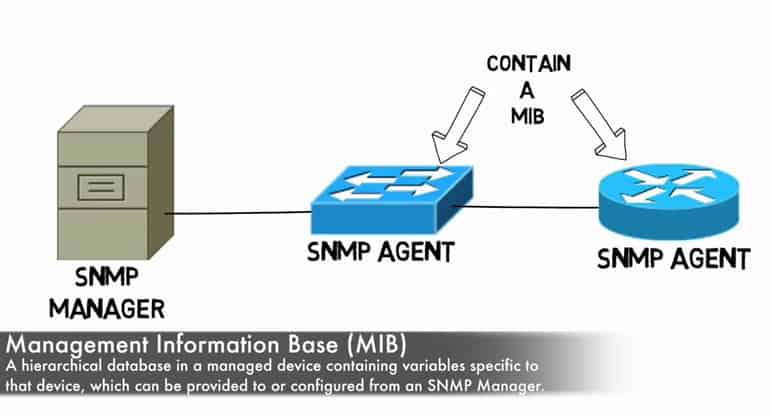
Secure your business with CyberHoot Today!!! Sign Up Now A Management Information Base...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now There is a...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now A Network Management System (NMS) is an...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Cybersecurity awareness training should be a...
Read more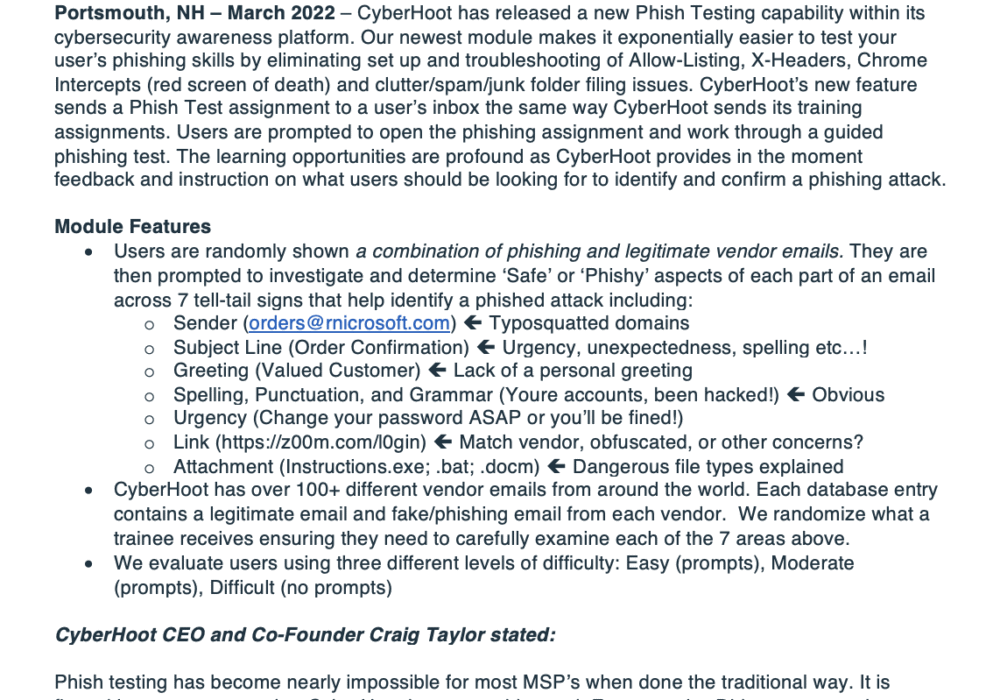
Click the image below to view a larger version Overview of the New Assignment-Based Phishing...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now A Self Assessment Questionnaire...
Read more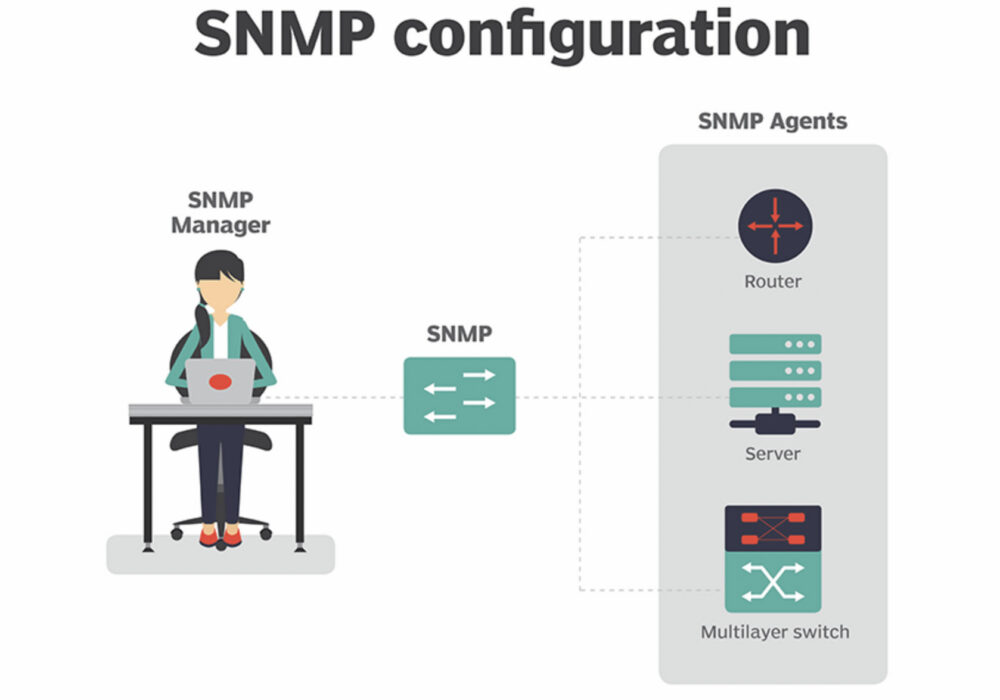
Secure your business with CyberHoot Today!!! Sign Up Now Simple Network Management Protocol...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now An Error correction code (ECC) checks read...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Quantum Computing is an area of computing...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now In January 2021, reports emerged of a...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Moore’s Law is a 1965 observation made by...
Read more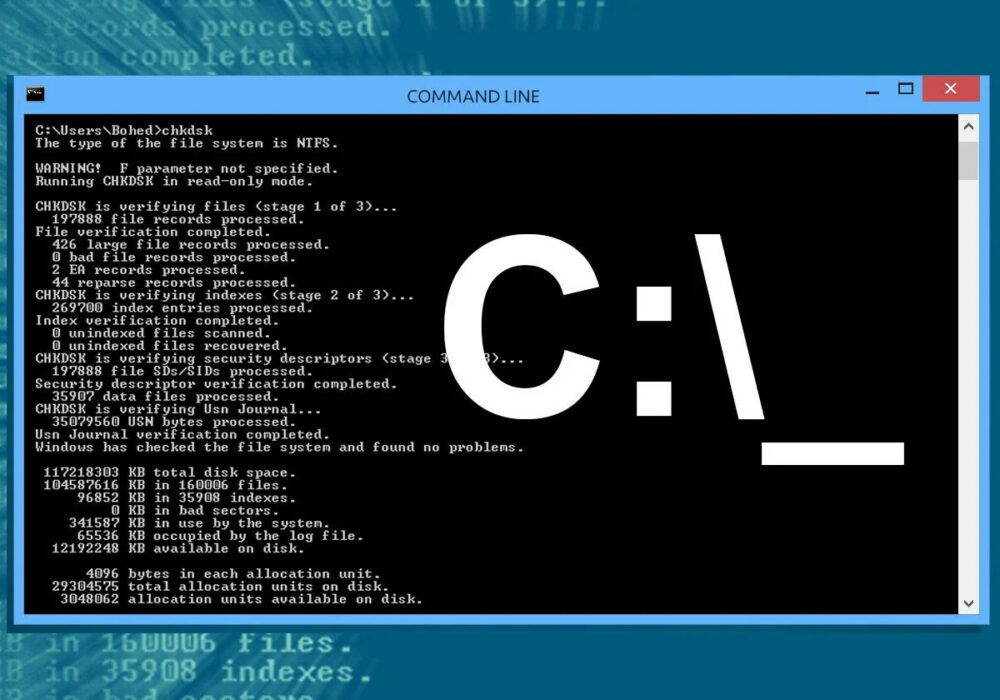
Secure your business with CyberHoot Today!!! Sign Up Now A Command Line Interface (CLI) is a...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
