“Using CyberHoot was one of the best decisions we made regarding SAT. Fully automated, training is interesting, and staff participation is high compared to other vendors.”
Image Source Ciphertext is data or information in its encrypted form. Ciphertext is the output when an...
Read more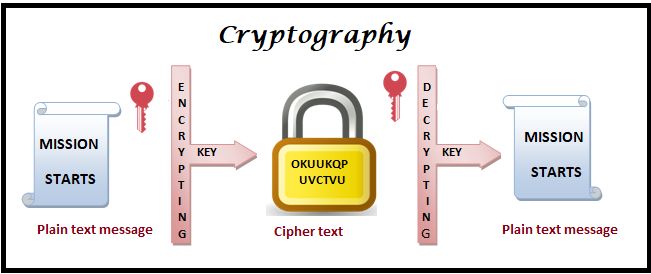
Cryptography is the use of mathematical techniques to provide security services, such as...
Read more
A Cryptographic Algorithm is a well-defined computational procedure that takes variable inputs, including a...
Read more
All credit and debit cards are now being made with "a computer that is 1/4 the size of a postage stamp" this...
Read more
Image Source Continuity of Operations Plan (COOP) is a document that sets forth procedures for the...
Read more
Image Source An Adversary is an individual, group, organization, or government that conducts or has...
Read more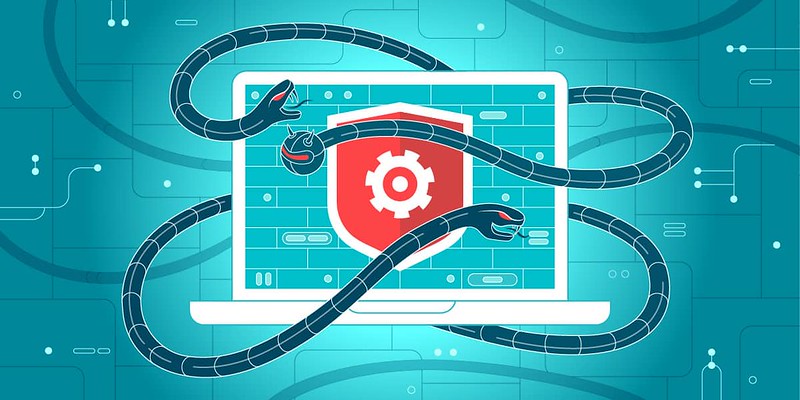
Image Source Antivirus Software is a program that monitors a computer or network to detect or...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
