"Craig and the CyberHoot team are great business partners! They are always open to enhancing their product, and ready to help my team with any deployment questions they may have. I am also an end user of the CyberHoot security..."

Secure your business with CyberHoot Today!!! Sign Up Now The National Institute of Standards and...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now The Cybersecurity and Infrastructure...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Geofencing is a technology for setting...
Read more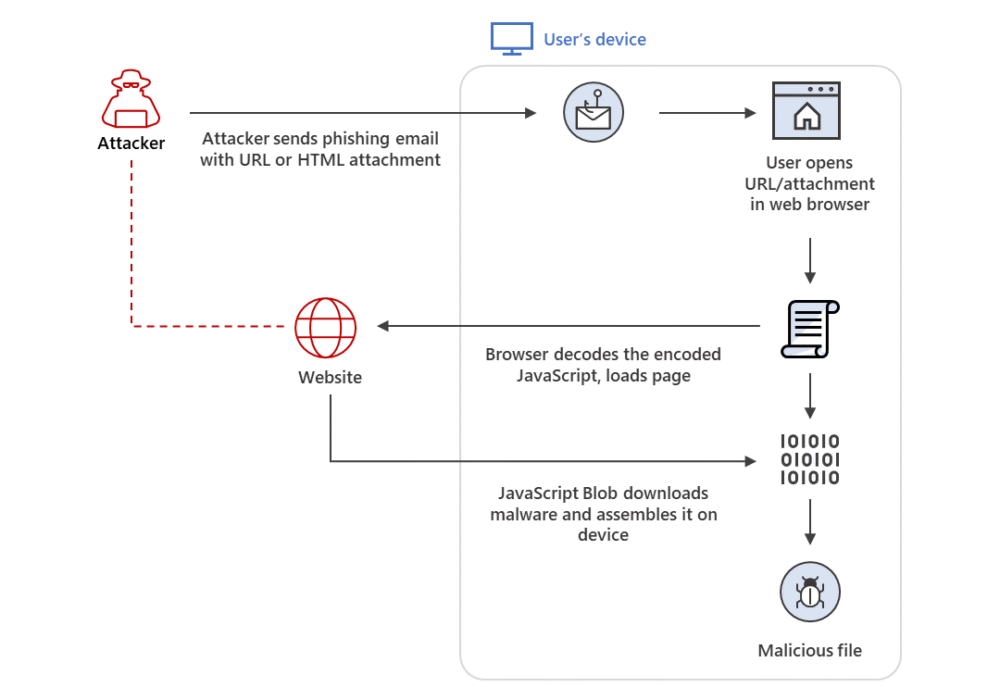
Secure your business with CyberHoot Today!!! Sign Up Now HTML Smuggling is an evasive malware...
Read more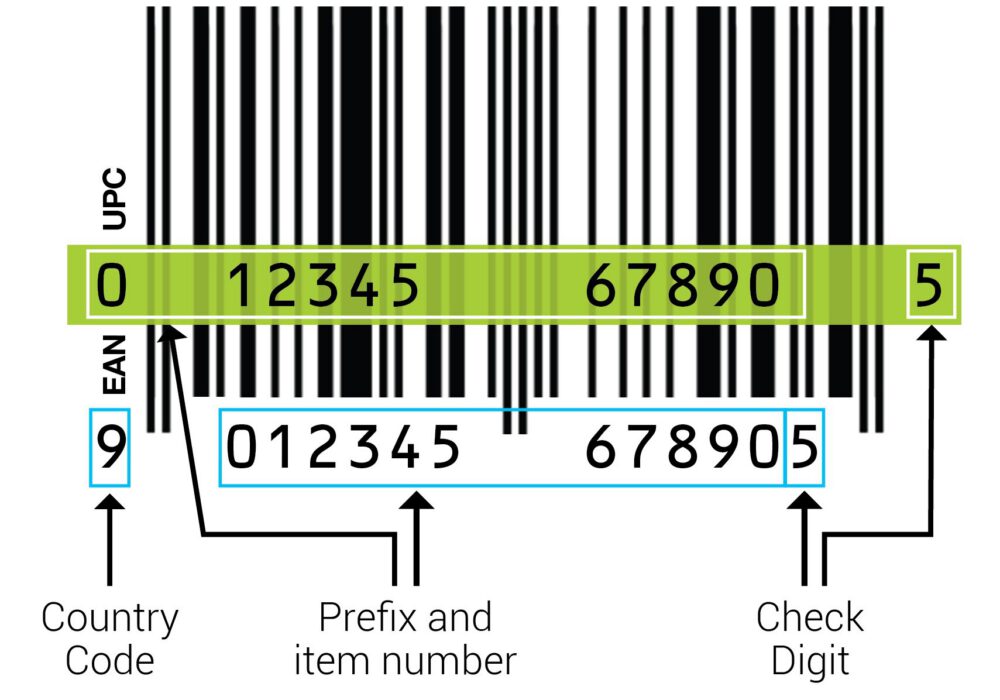
Secure your business with CyberHoot Today!!! Sign Up Now A Check Digit is a digit added to a string...
Read more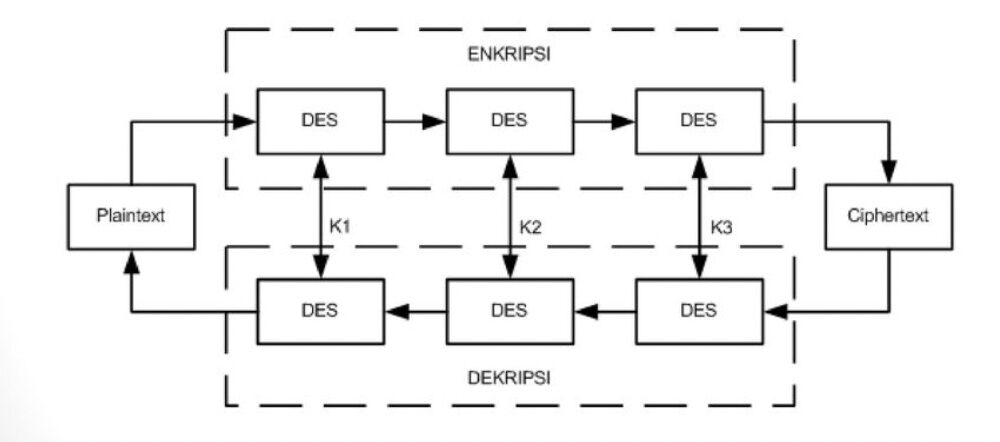
Secure your business with CyberHoot Today!!! Sign Up Now 3DES Encryption, also known as Triple Data...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Assembly Language is the most basic...
Read more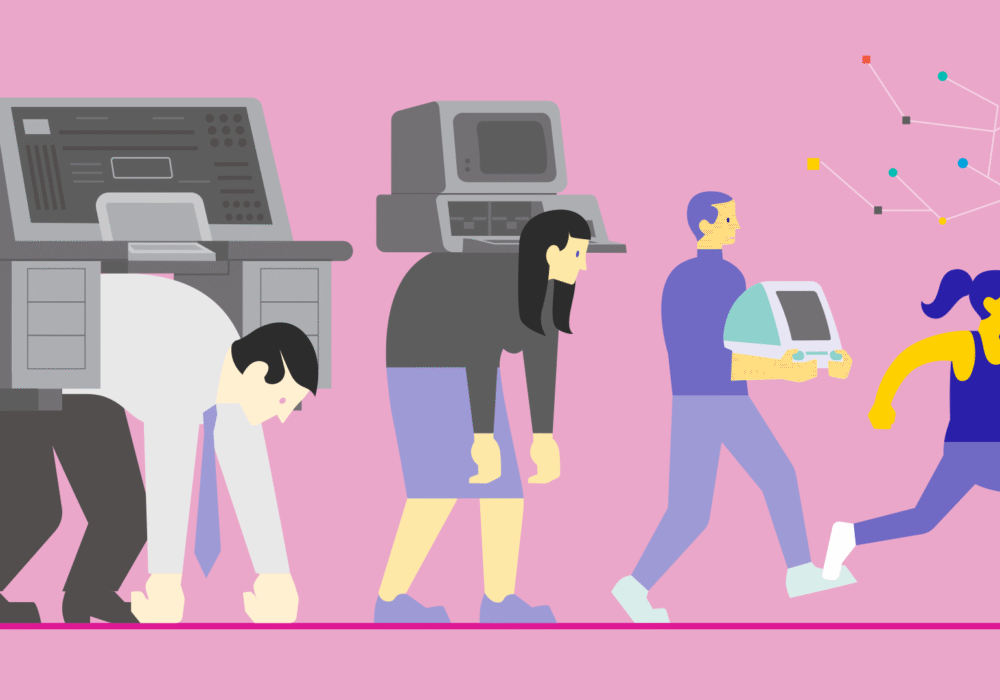
Secure your business with CyberHoot Today!!! Sign Up Now Moore’s Law is a 1965 observation made by...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
