"CyberHoot is a great option for Cybersecurity for our schools. The videos and other training are very user-friendly. Their support is fantastic as well."
RADIUS Authentication, also known as Remote Authentication Dial-In User Service (RADIUS), is a...
Read more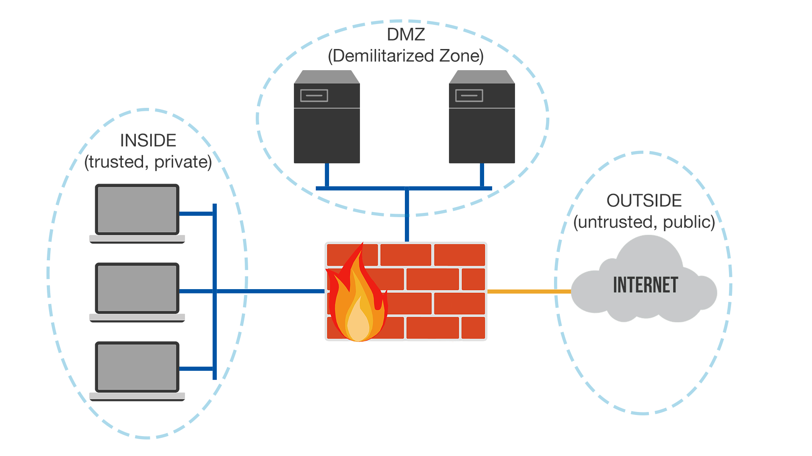
The Demilitarized Zone (DMZ) is sometimes referred to as a "perimeter network", its primary...
Read more
A Guest Wi-Fi Network is a separate network that gives users access to your router. A Guest...
Read moreTrusted Wi-Fi Network refers to a network that is password protected and often is AD (active...
Read more
A Virtual Local Area Network (VLAN) is a logical grouping of devices in the same broadcast...
Read more
A Kill Chain in cybersecurity reveals the phases of a cyber attack, from early reconnaissance...
Read more
A Business Continuity and Disaster Recovery (BCDR) Plan is a set of techniques and processes...
Read more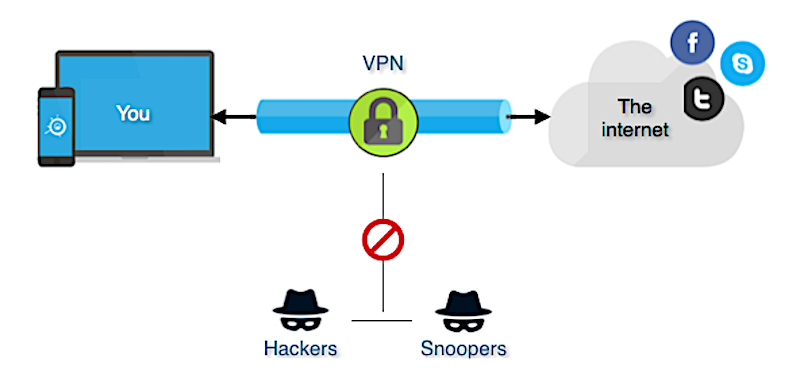
A Virtual Private Network (VPN) is a way to create online privacy and anonymity by creating a...
Read more
A Hacktivist is someone who uses technology systems or networks maliciously to promote a...
Read more
Containment refers to the limiting and preventing of further damage to a computer system or...
Read more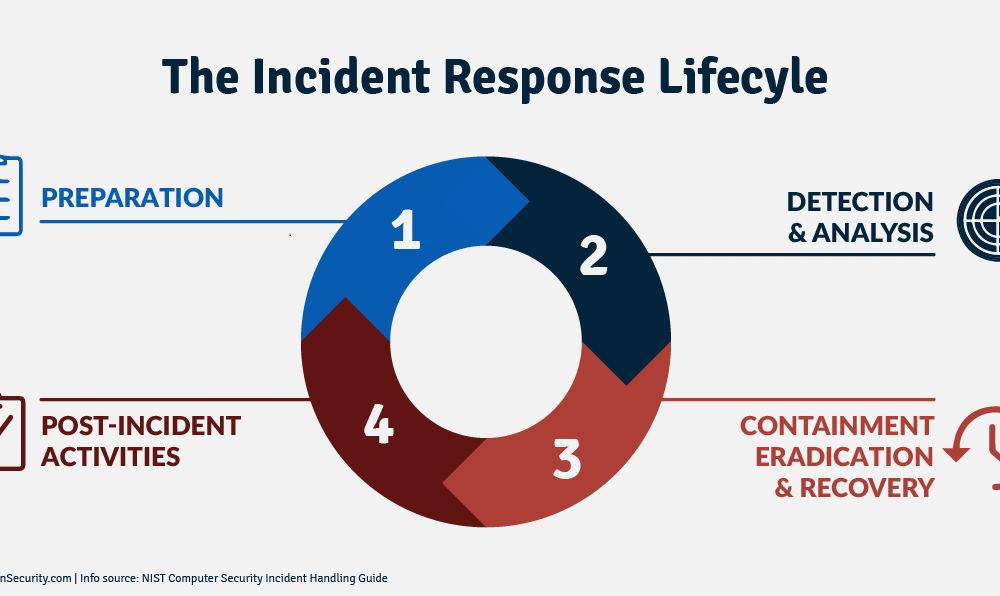
Eradication refers to what happens following containment of a cyber attack incident. After the...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
