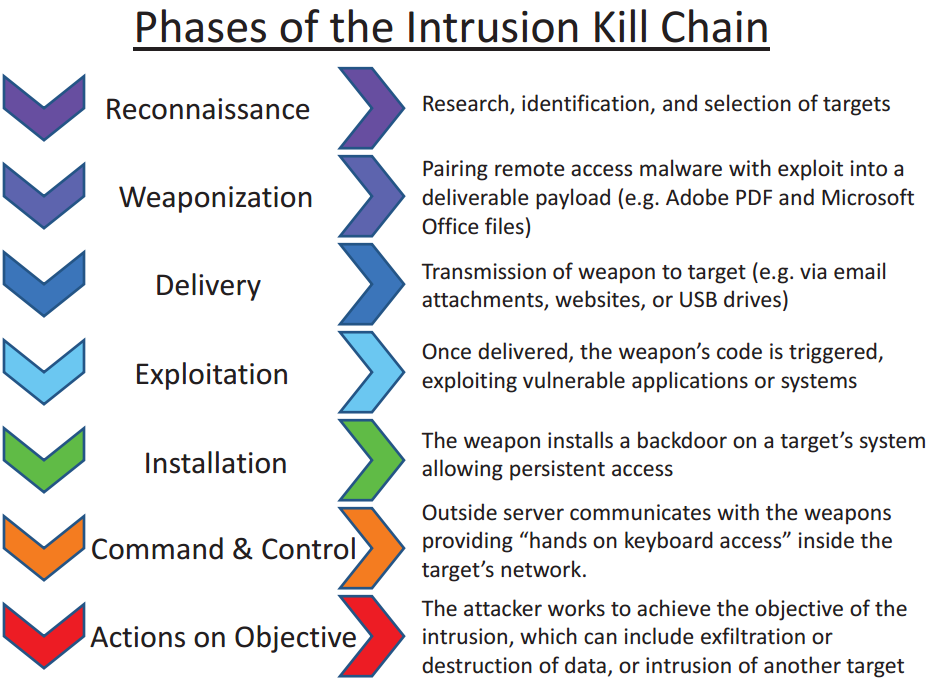
A Kill Chain in cybersecurity reveals the phases of a cyber attack, from early reconnaissance to the goal of data exfiltration. Kill chains are also used as management tools for security professionals to help continuously improve their systems and network’s security. According to Lockheed Martin, threats must pass through many phases in the kill-chain, including:
In a word. Yes. Kill chains simply illustrate the process by which hackers infiltrate your network. Interrupting the kill chain means discovering the hacker before they complete objective 7 – Actions on Objective. As an SMB owner, you want to build a robust cybersecurity program that can identify hackers before they execute their objective. In most cases, that’s installing a ransomware attack to force a bitcoin payment out of you. SMB’s can interrupt the Kill Chain through education and awareness training to prevent steps 3 to 7 from occurring.
Source: Lockheed Martin, Varonis
Discover and share the latest cybersecurity trends, tips and best practices – alongside new threats to watch out for.

A Practical Brief for vCISOs THE WARNING WE IGNORED OR COULD NOT UNDERSTAND For years, the most credible...
Read more
A guide to spotting senior executive impersonation scams before the fake CEO gets a real wire transfer. It...
Read more
Artificial Intelligence (or AI) is making phishing emails smarter, malware sneakier, and credential theft easier...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
