"CyberHoot lets us access expert cybersecurity guidance without hiring a full-time specialist."
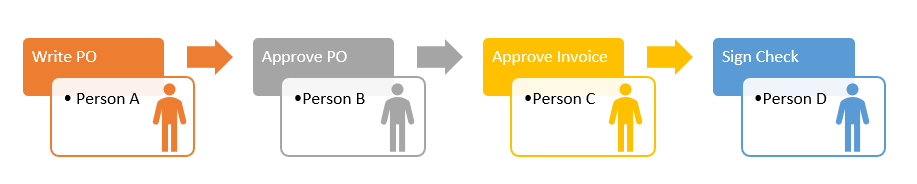
Separation of Duties involves dividing roles and responsibilities to minimize the risk of a single...
Read more
General Information, also known as Public information, is data that is commonly found in marketing...
Read more
Intellectual Property (IP) refers to the ownership of a specific idea, design, manuscript, etc. by the...
Read more
The ILOVEYOU Virus, also known as, the Love Bug, is a computer worm that infected over 10 million...
Read more
Mandatory Controls, also known as Mandatory Access Controls (MAC), are a type of access control that...
Read more
Discretionary Access Controls, also known as DAC, are types of cybersecurity measures that allow or...
Read more
Sensitive (or restricted) Information is data from a company or organization that is generally not...
Read more
Secure your business with CyberHoot Today!!! Sign Up Now Critical (or Confidential) Information in a...
Read more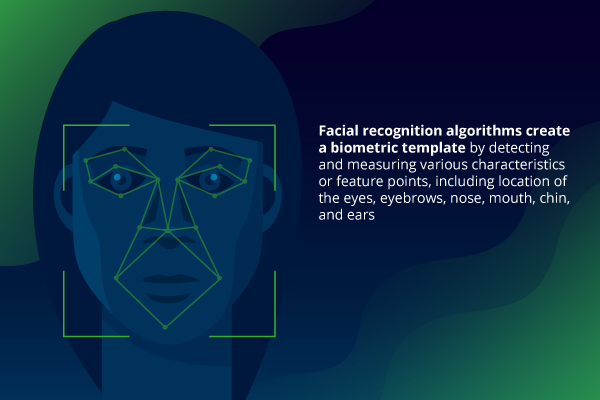
Facial Recognition is an increasingly effective and popular technology capable of identifying a...
Read more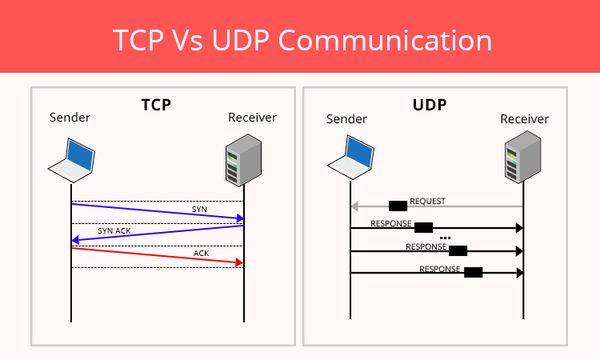
Transmission Control Protocol (TCP) is a standard that defines how to establish and maintain a...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
