"Managed Service Providers (MSP's) are constantly bombarded with new vendors and products that either overlap with a product already in our line cards or is difficult to get client buy in. Cyberhoot brings a new product/service to the MSP space..."
A Buffer Overflow Attack happens when a program tries to fill a block of memory (a memory...
Read more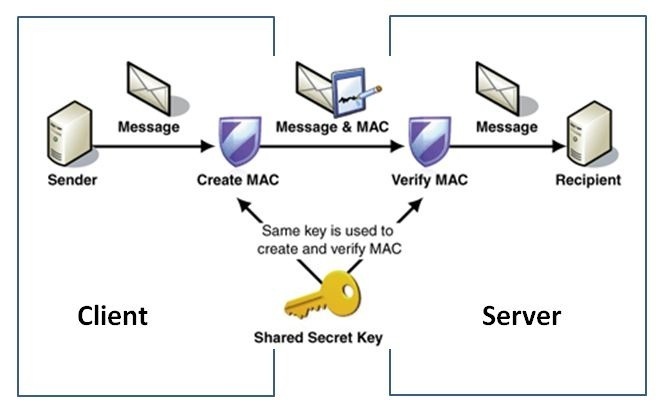
HMAC Authentication is short for Hash-Based Message Authentication Code, a strategy used to...
Read more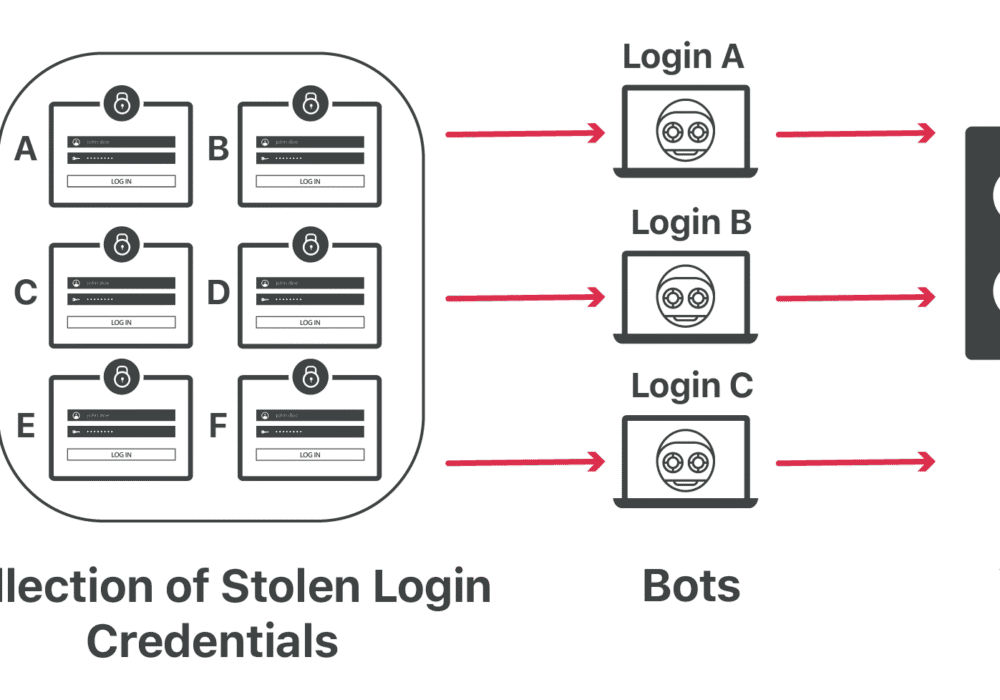
Credential Stuffing is the autonomous injection of stolen username and password credentials in a web...
Read more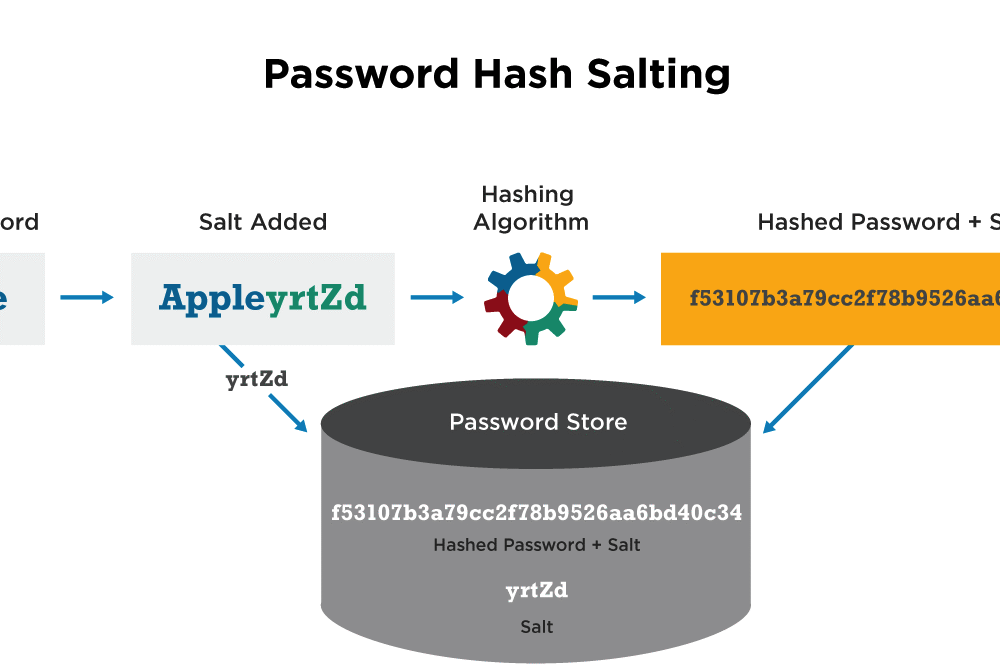
Password Salting is a technique used to help protect passwords stored in a database from being...
Read more
Commercial Off-The-Shelf (COTS) in cybersecurity is a computer hardware or software product made for...
Read more
Anti-Malware is a solution that maintains computer security and protects sensitive data that is transmitted by a...
Read more
Safe Links (also known as URL Protection) are tools used by anti-SPAM technology solutions that...
Read more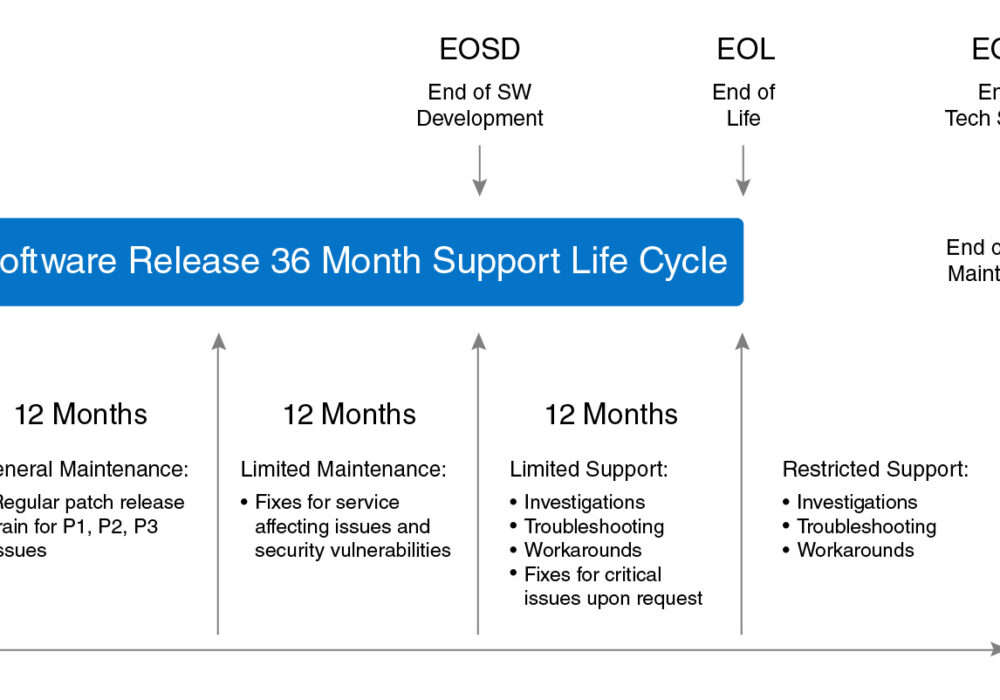
End-of-Life (EOL)/End-of-Support(EOS) describe the final stage of a product's lifecycle. Once a product...
Read more
Remote Monitoring and Management (RMM) is a set of Information Technology (IT) tools that are...
Read moreMonthly Recurring Revenue (MRR) is the most important topic for Managed Service Providers (MSPs). MRR...
Read more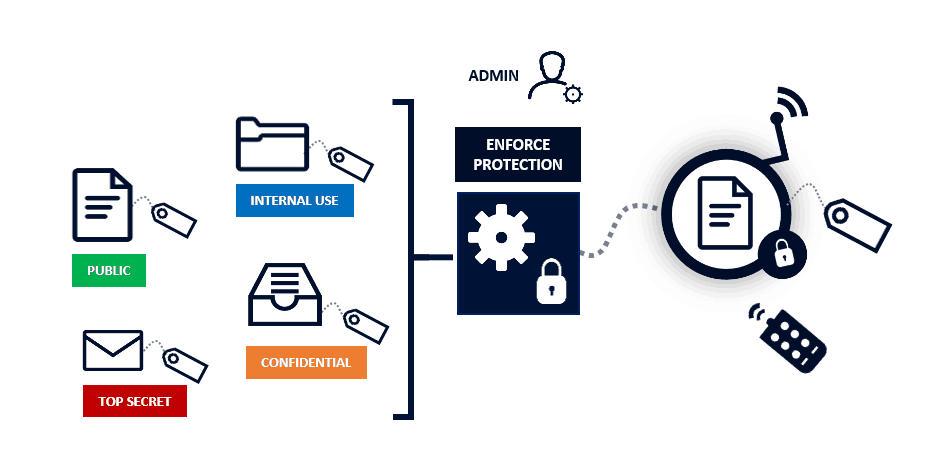
Data Classification is about categorizing data into buckets to make it easier to retrieve,...
Read more
Contact Tracing is a medical term which describes a process used to identify, trace, and contact people...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
