"Managed Service Providers (MSP's) are constantly bombarded with new vendors and products that either overlap with a product already in our line cards or is difficult to get client buy in. Cyberhoot brings a new product/service to the MSP space..."
Image Source An investigation is a systematic and formal inquiry into a qualified threat or...
Read more
So similar to the real deal as to be disconcerting... Technology is always improving and hackers are always...
Read more
Access Control Access control is a security technique that regulates who or what can view or use...
Read more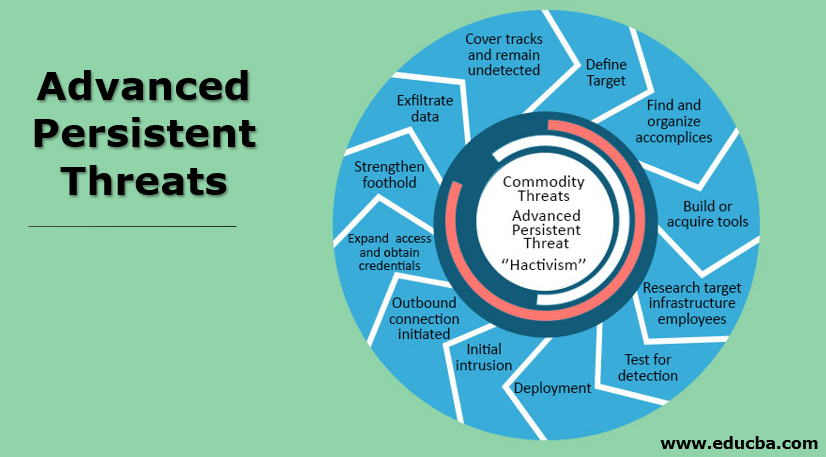
An Advanced Persistent Threat (APT) is an adversary that possesses sophisticated levels of expertise and...
Read more
Image Source An Adversary is an individual, group, organization, or government that conducts or has...
Read more
Image Source Antivirus Software is a program that monitors a computer or network to detect or...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
