A Purple Team is a group of cybersecurity experts that take on the role of the Blue Team and Red Team in a cybersecurity exercise with the intention of providing a stronger, deeper security activity that delivers more tailored, realistic assurance to the organization being tested.
By sharing intelligence data across the red and blue teams during the purple teaming process, organizations can better understand hackers’ Tactics, Techniques, and Procedures (TTPs). By mimicking these TTPs through a series of red team exercises, the blue team has the ability to configure, tune, and improve its detection and response capacity. Highly experienced red and blue teams can provide purple teaming engagements that allow organizations to measure their detection and response capabilities in a way that is much more closely aligned with real-world threats.
Small to medium-sized businesses typically don’t need to run Red, Blue, or Purple Team exercises. These are often done with larger companies that have a significant budget for these exercises. A form of Red Team exercise is Penetration Testing, which as you may know, costs $15,000-$30,000 at a minimum for a high-quality test. Unless your company has a significant budget, and cybersecurity maturity in many other areas critical to your defense-in-depth cybersecurity program posture, paying this much for an red/blue/purple team exercise, may not be smart or affordable for your organization. However, your organization can do many other things to improve its cybersecurity without protections without breaking the bank as outlined below. Additional Cybersecurity Recommendations
These recommendations will help you and your business stay secure with the various threats you may face on a day-to-day basis. All of the suggestions listed below can be gained by hiring CyberHoot’s vCISO Program development services.
All of these recommendations are built into CyberHoot the product or CyberHoot’s vCISO Services. With CyberHoot you can govern, train, assess, and test your employees. Visit CyberHoot.com and sign up for our services today. At the very least continue to learn by enrolling in our monthly Cybersecurity newsletters to stay on top of current cybersecurity updates.
Sources:
Additional Reading:
Red Team VS Blue Team In Cybersecurity
Related Terms:
CyberHoot does have some other resources available for your use. Below are links to all of our resources, feel free to check them out whenever you like:
Note: If you’d like to subscribe to our newsletter, visit any link above (besides infographics) and enter your email address on the right-hand side of the page, and click ‘Send Me Newsletters’.
Discover and share the latest cybersecurity trends, tips and best practices – alongside new threats to watch out for.

Remember 2020? We scanned QR codes for everything. Restaurant menus. Parking meters. That awkward moment at a...
Read more
Phishing emails used to be easy to spot. Bad grammar. Weird links. Obvious scams. Those days are...
Read more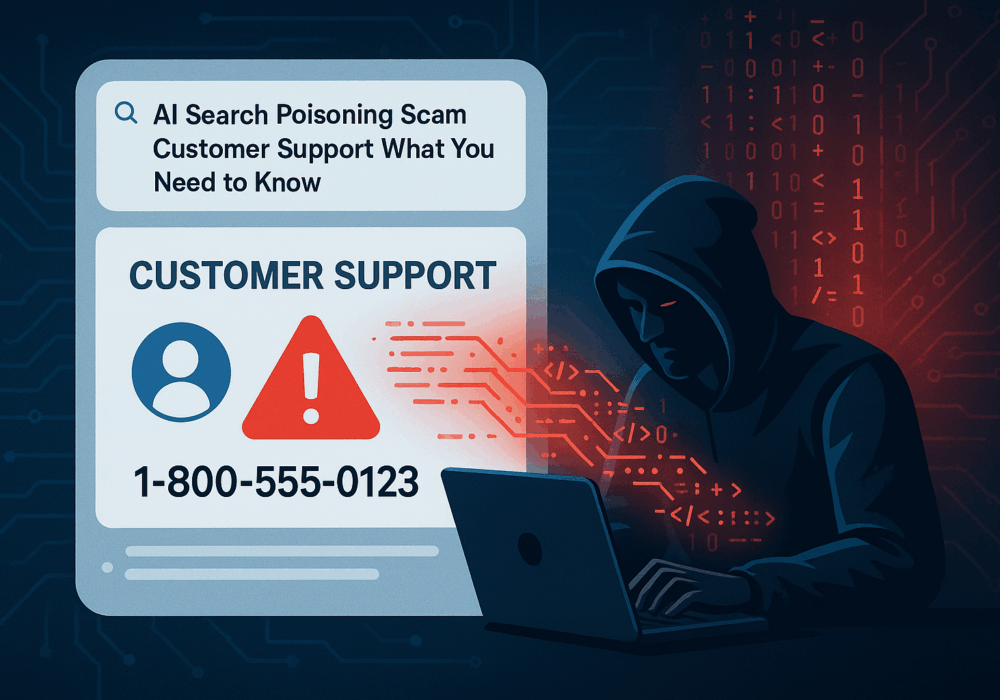
Cybercriminals always follow Internet eyeballs. Not literally, but figuratively. And today's eyeballs are...
Read moreGet sharper eyes on human risks, with the positive approach that beats traditional phish testing.
